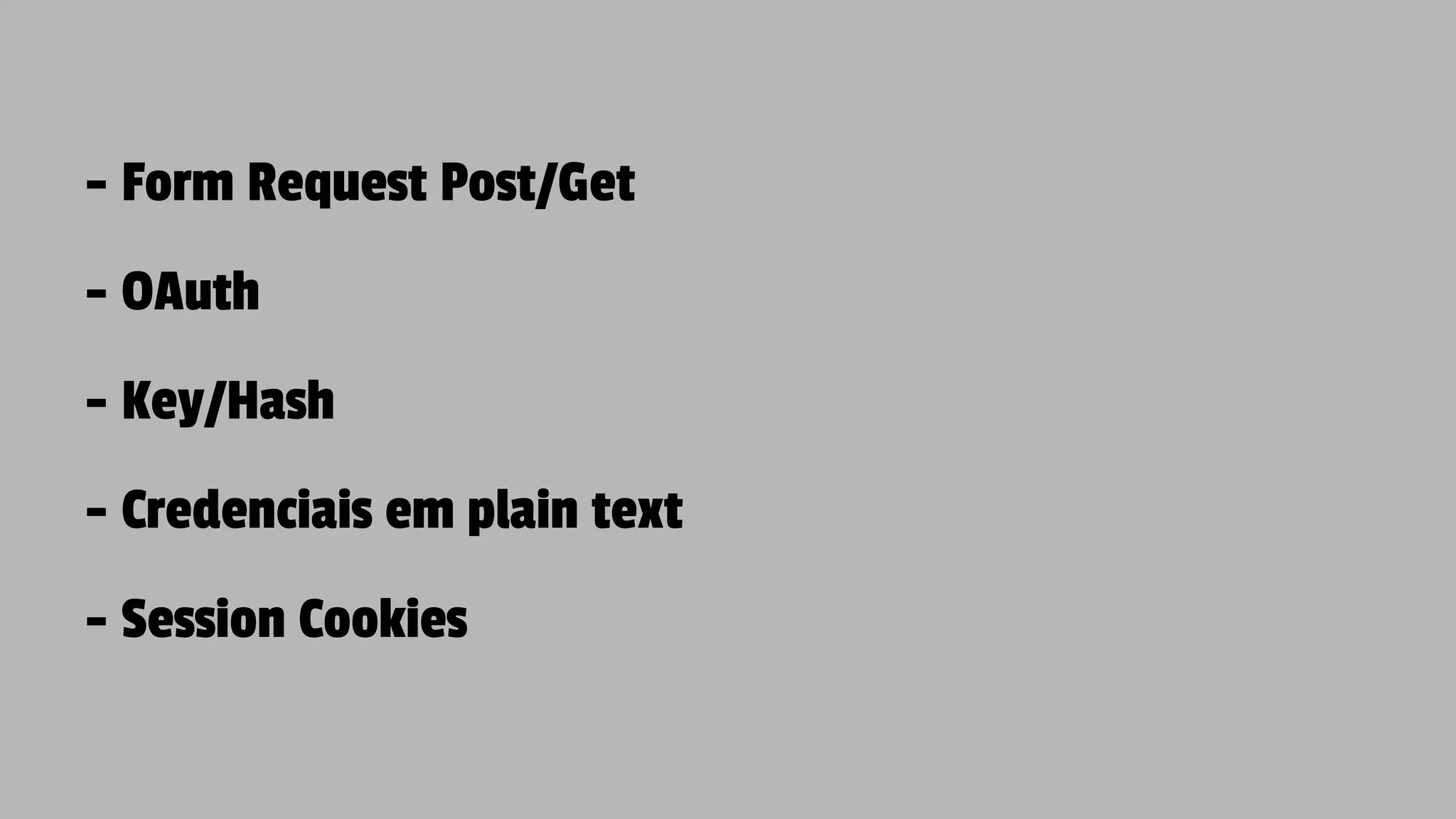
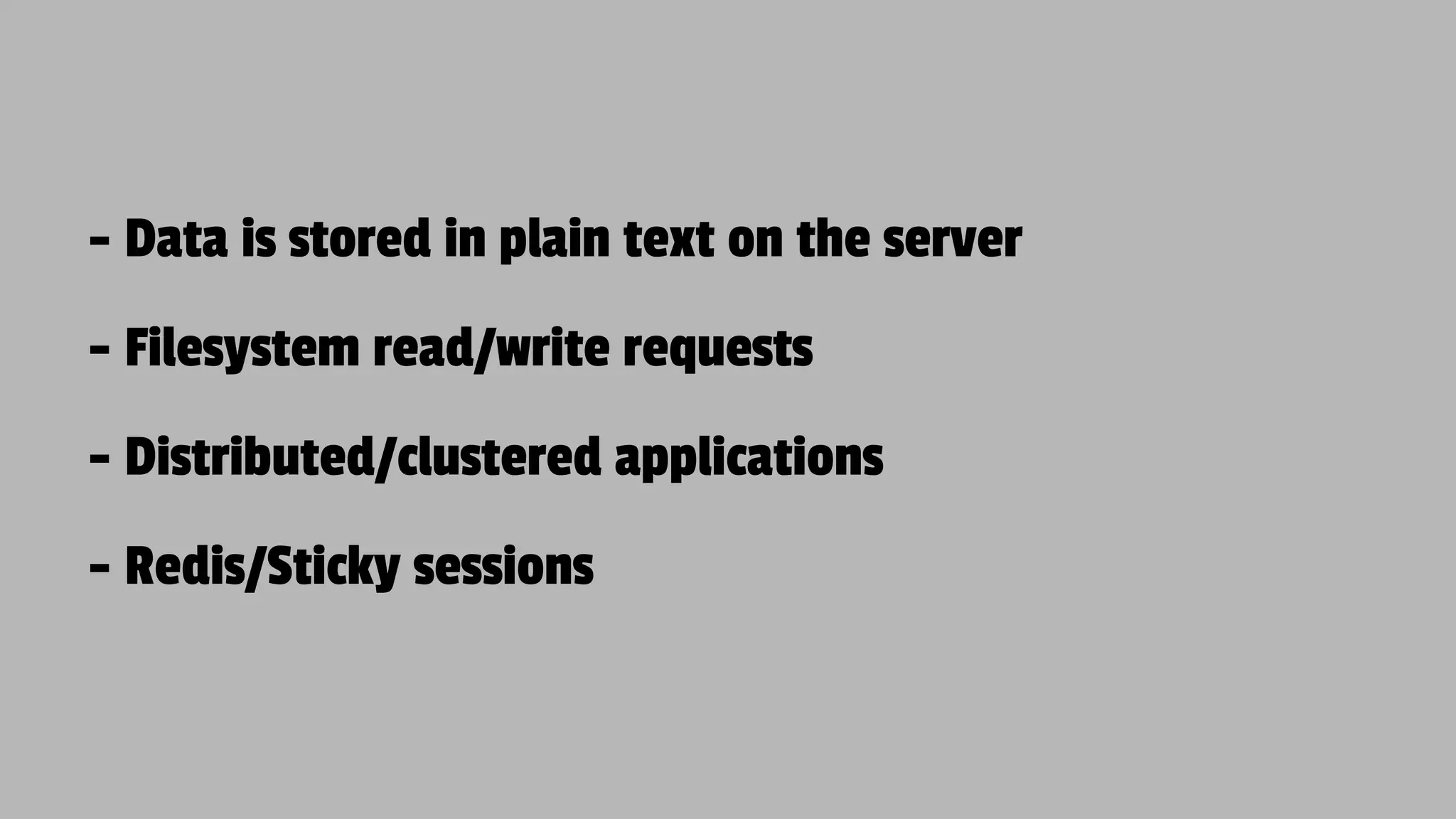
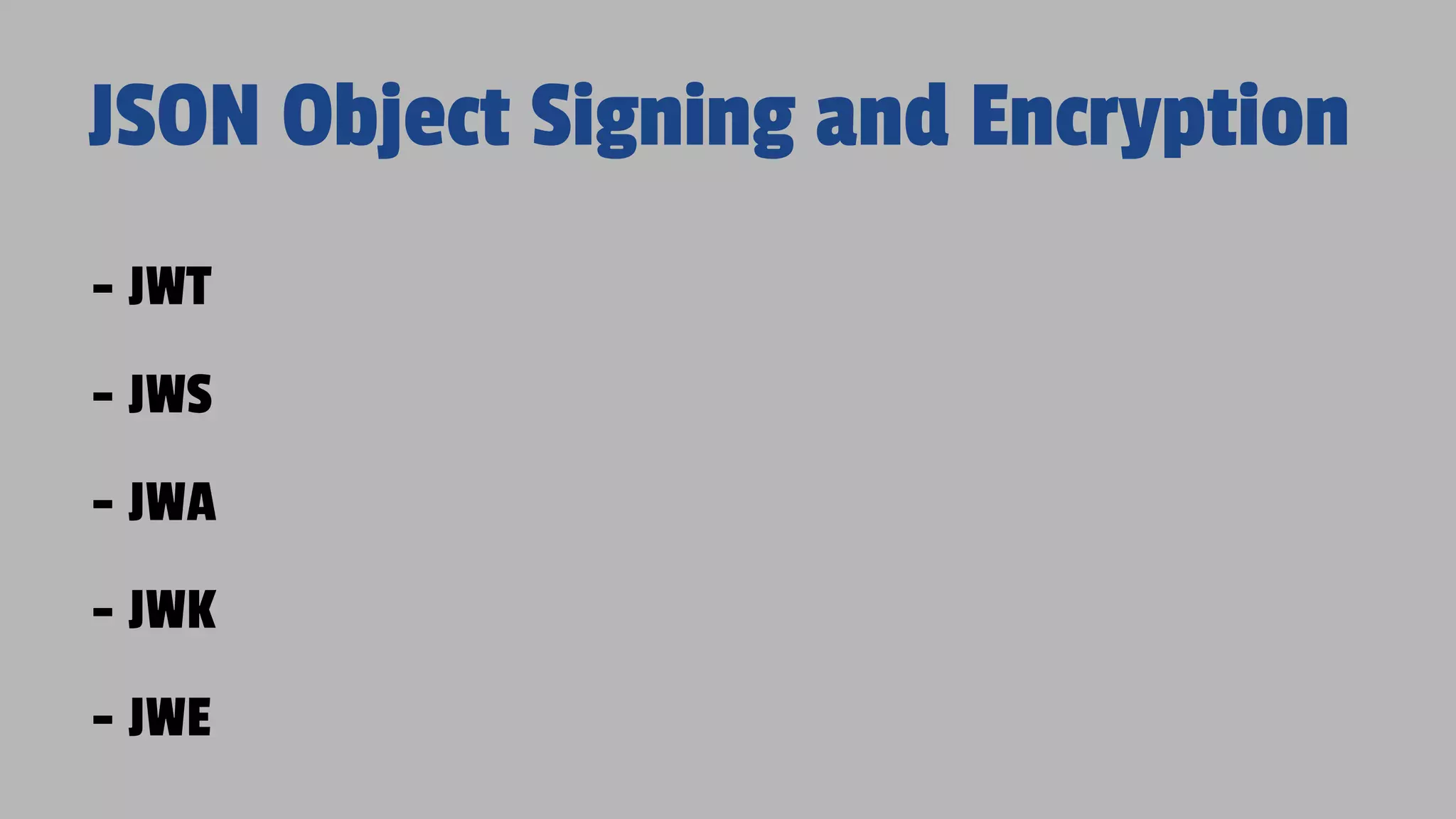
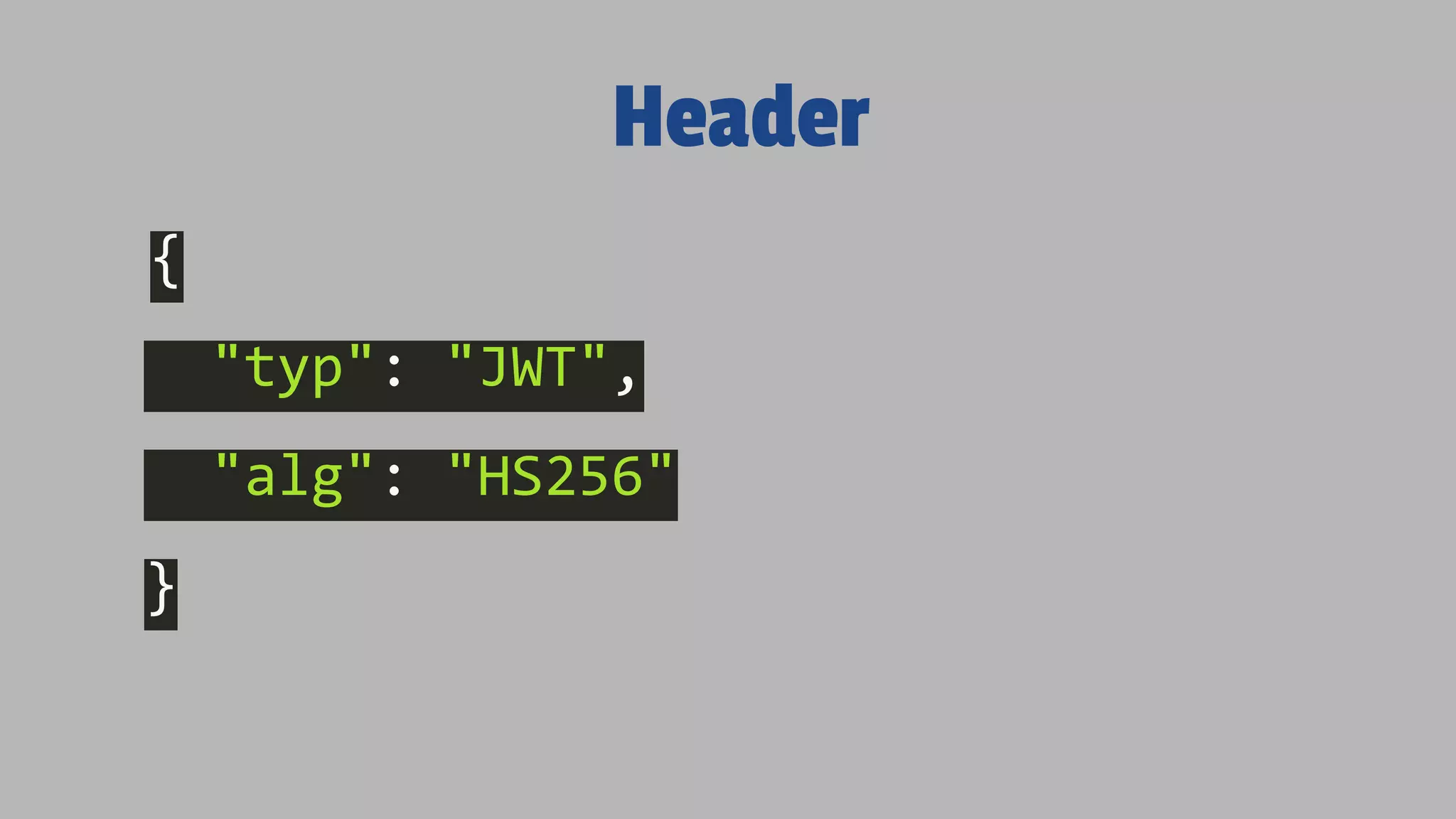
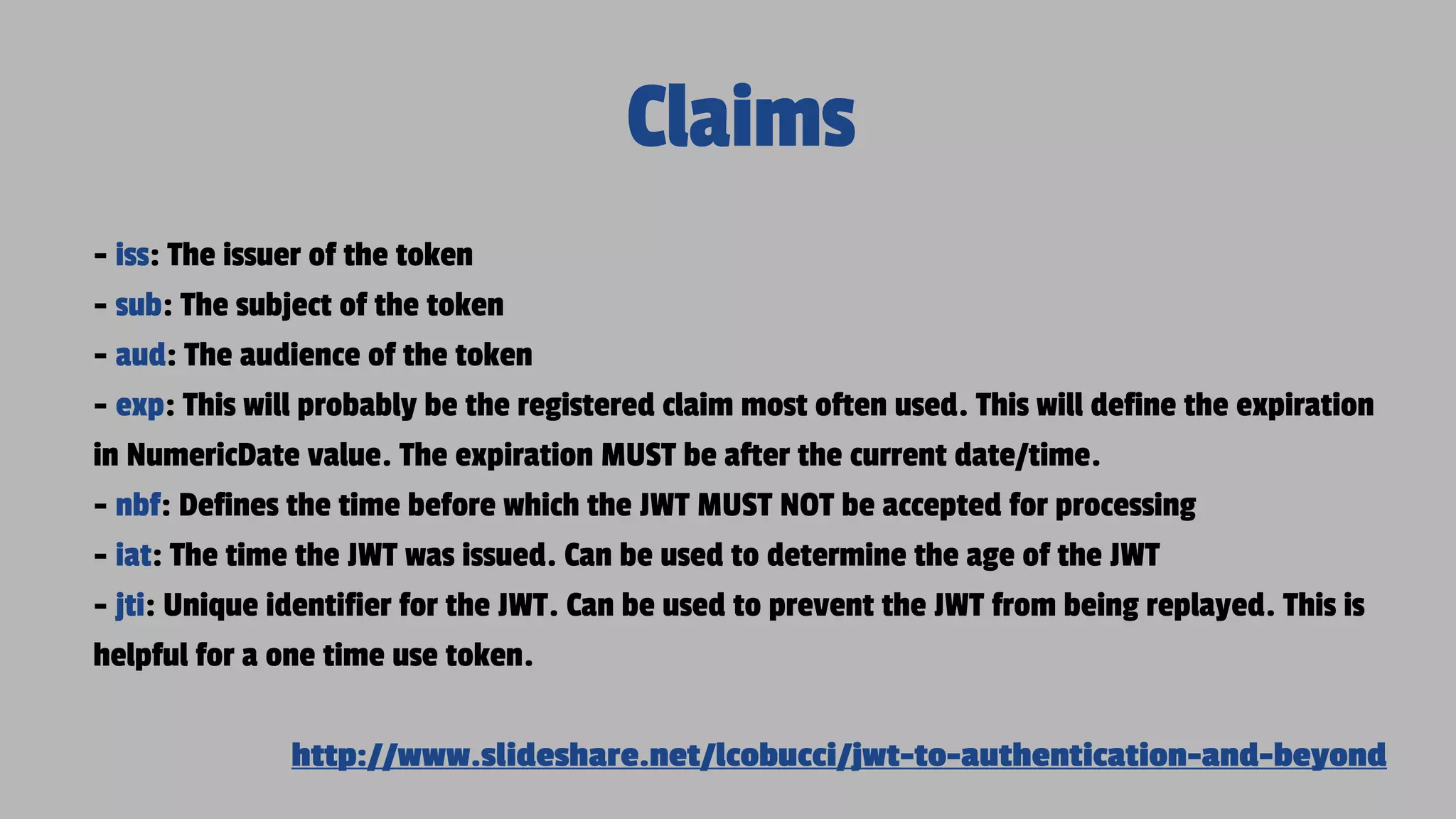
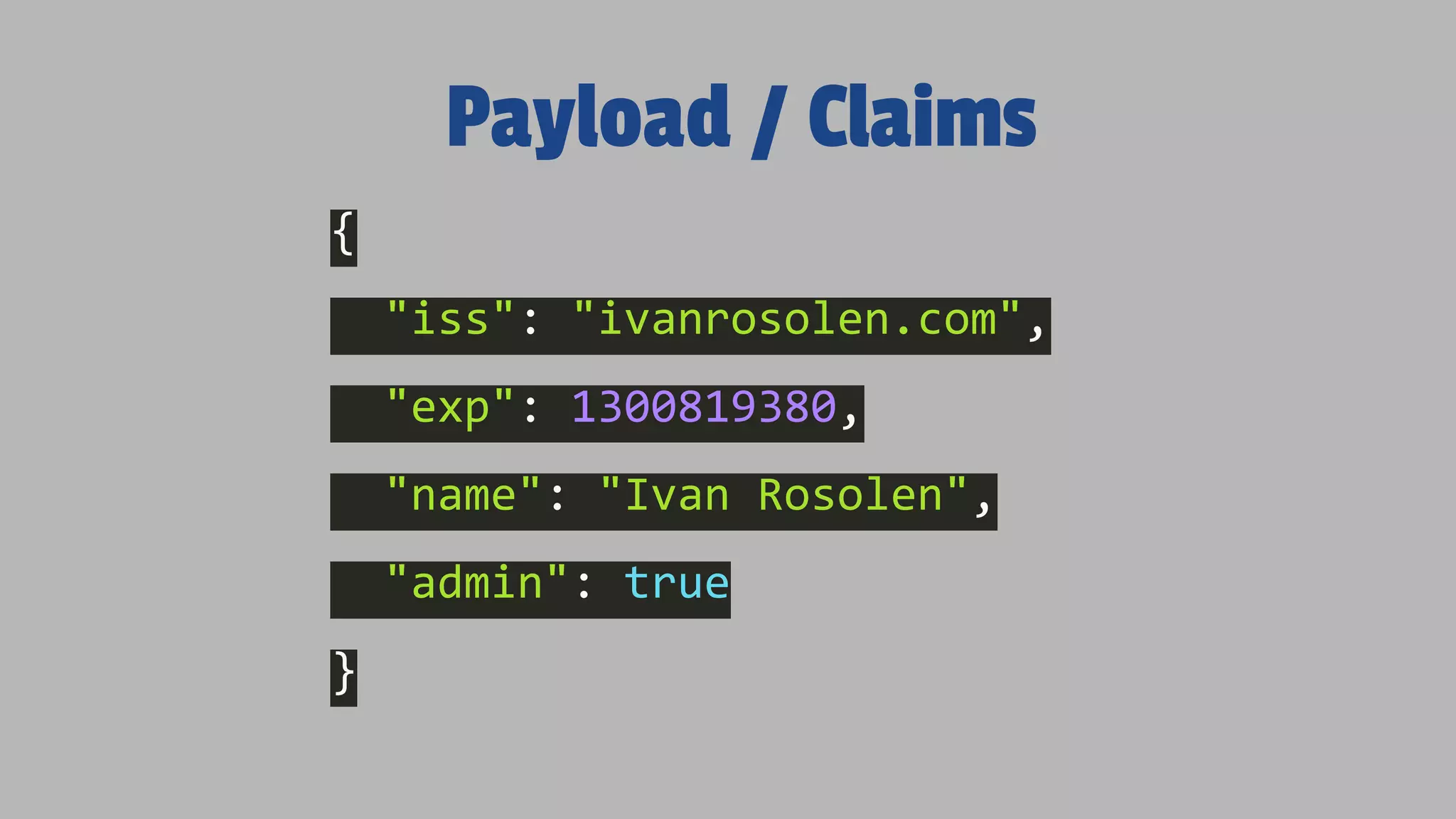
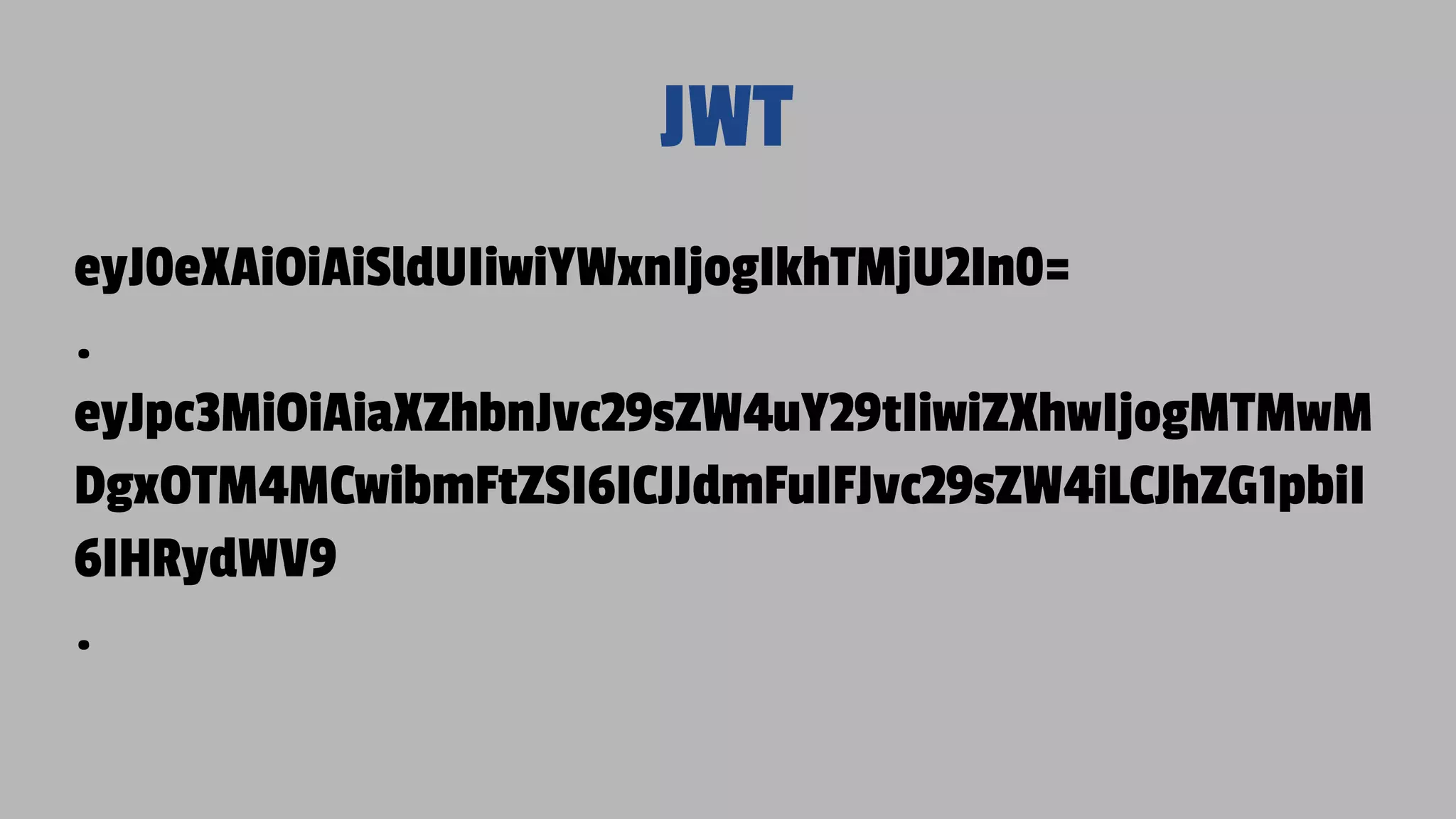
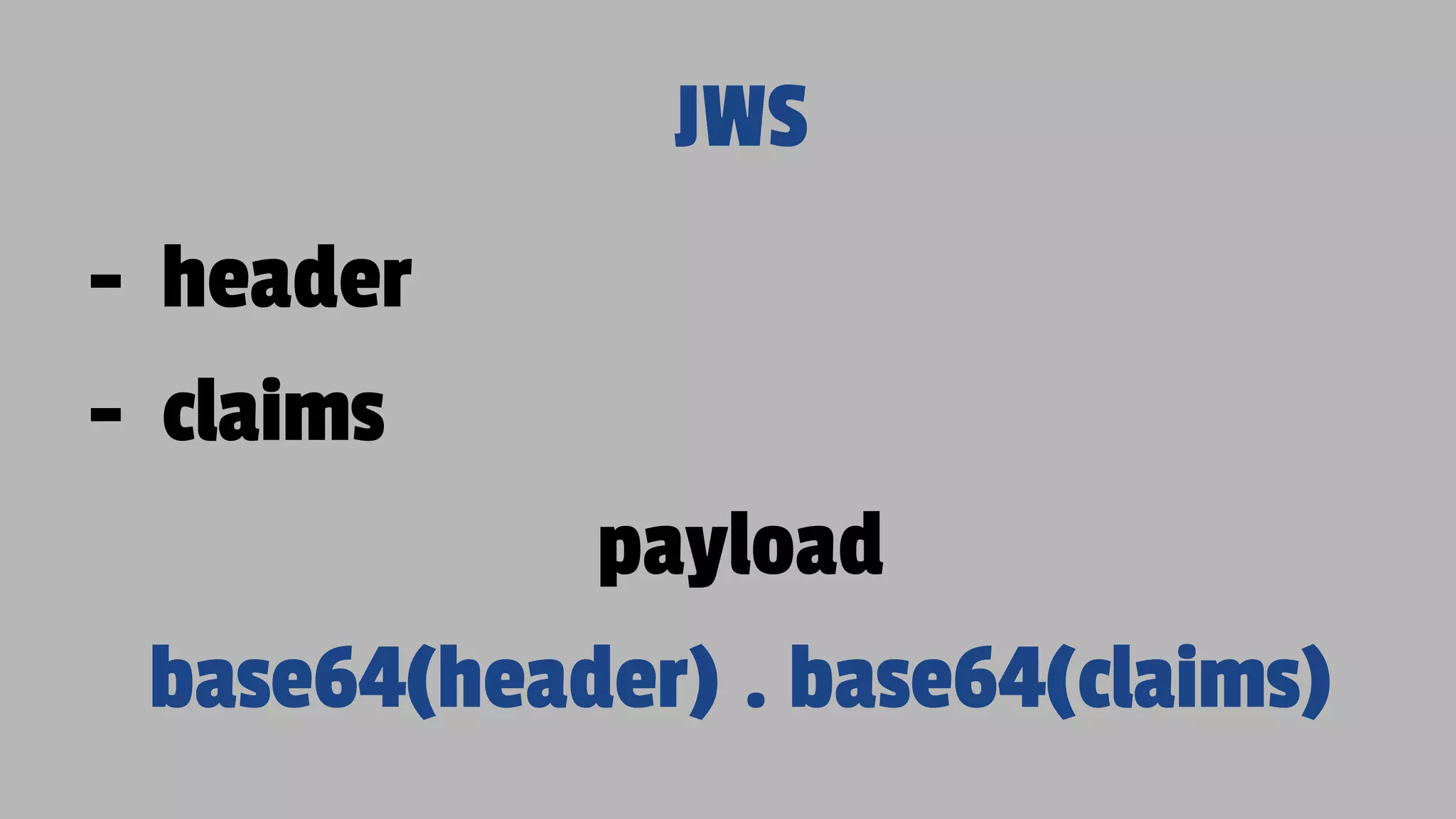
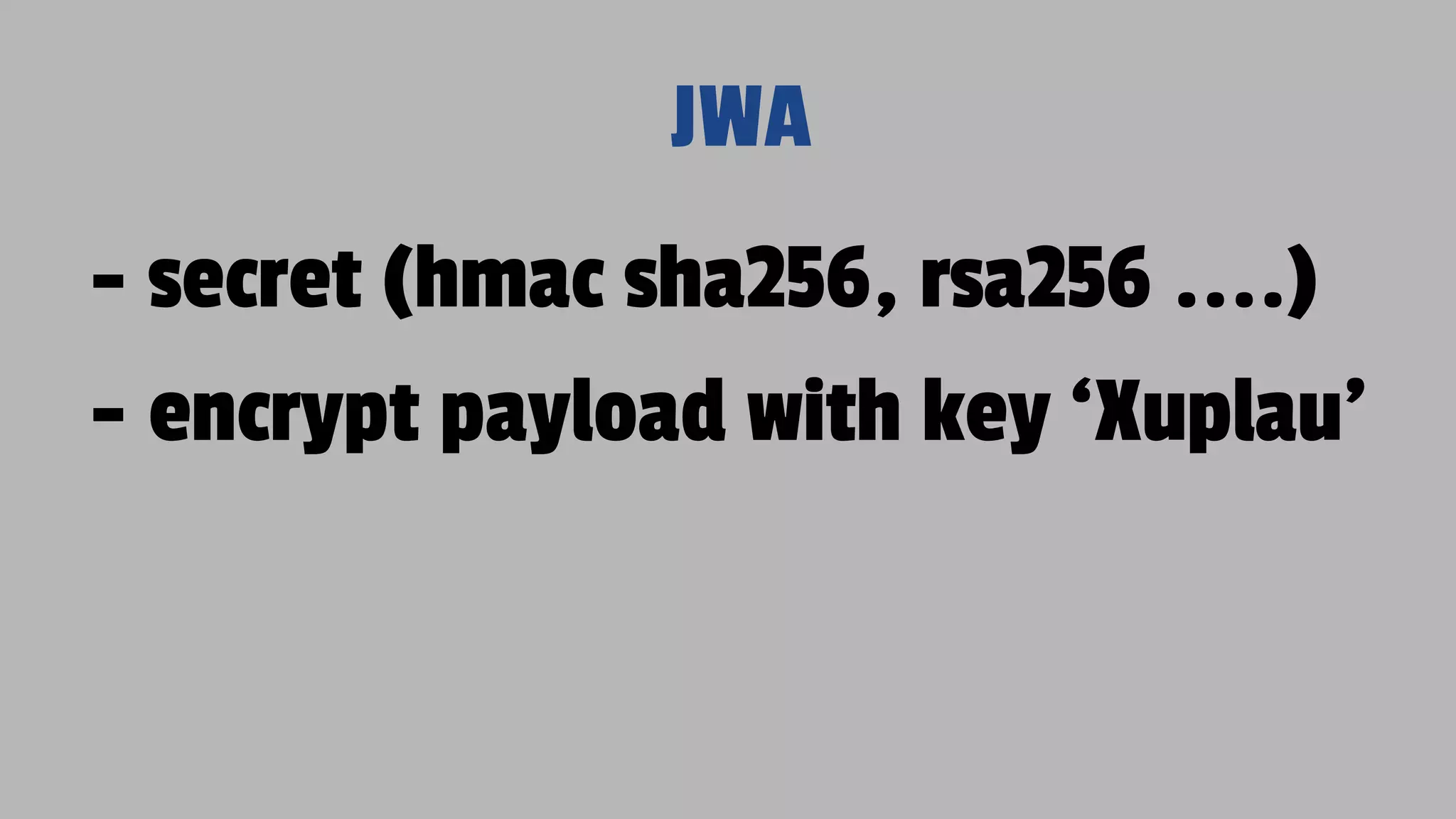
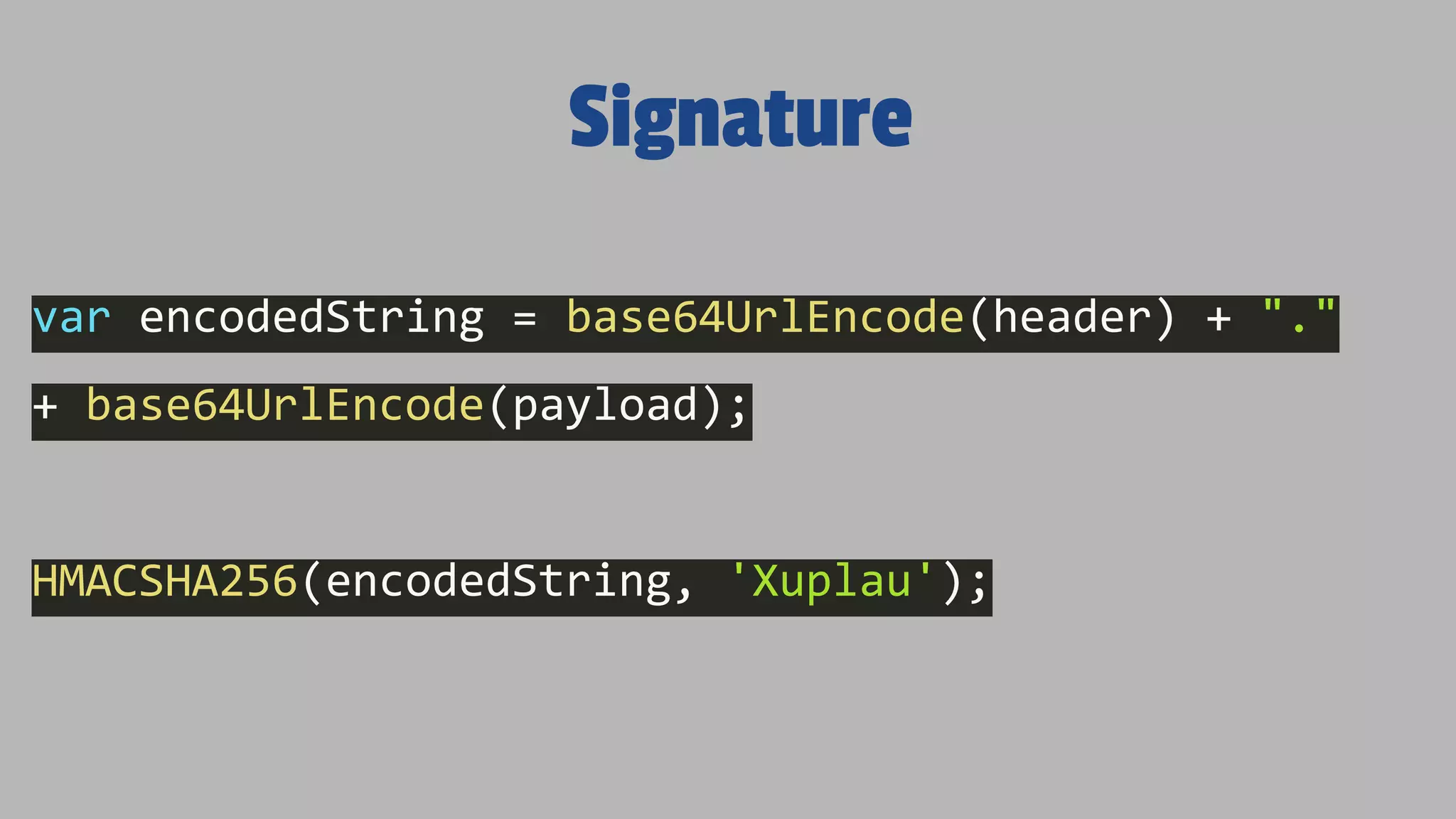
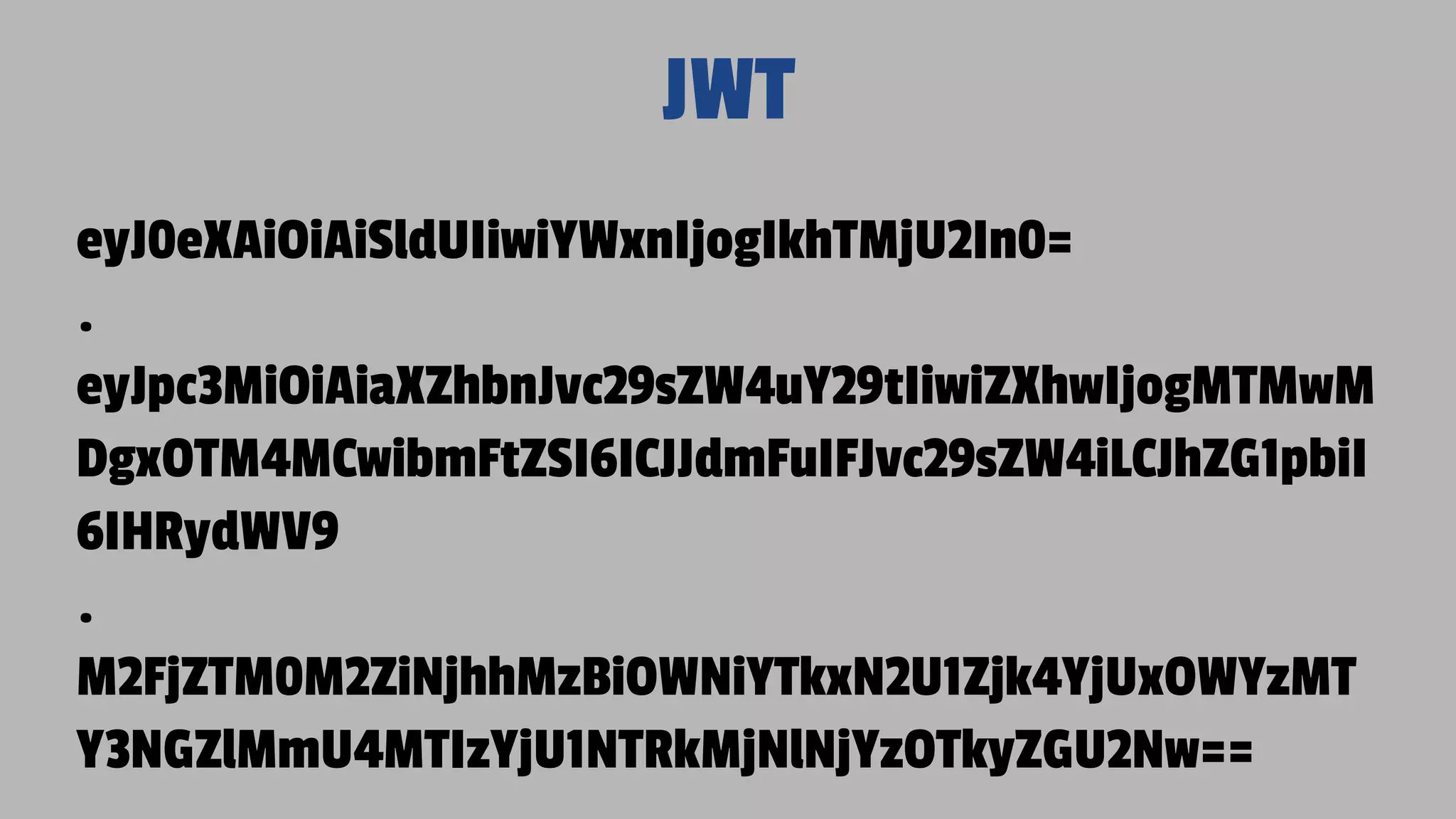
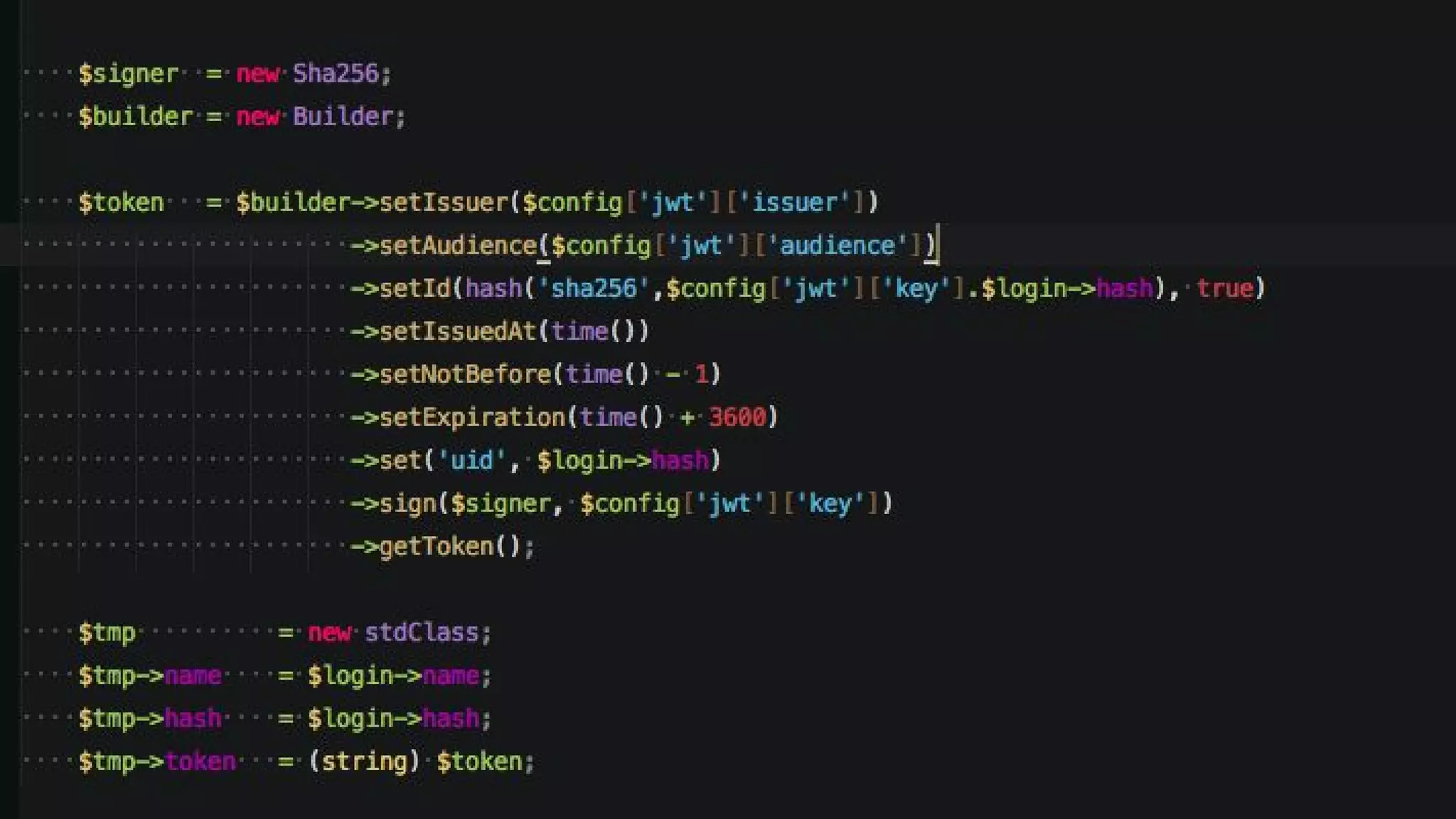
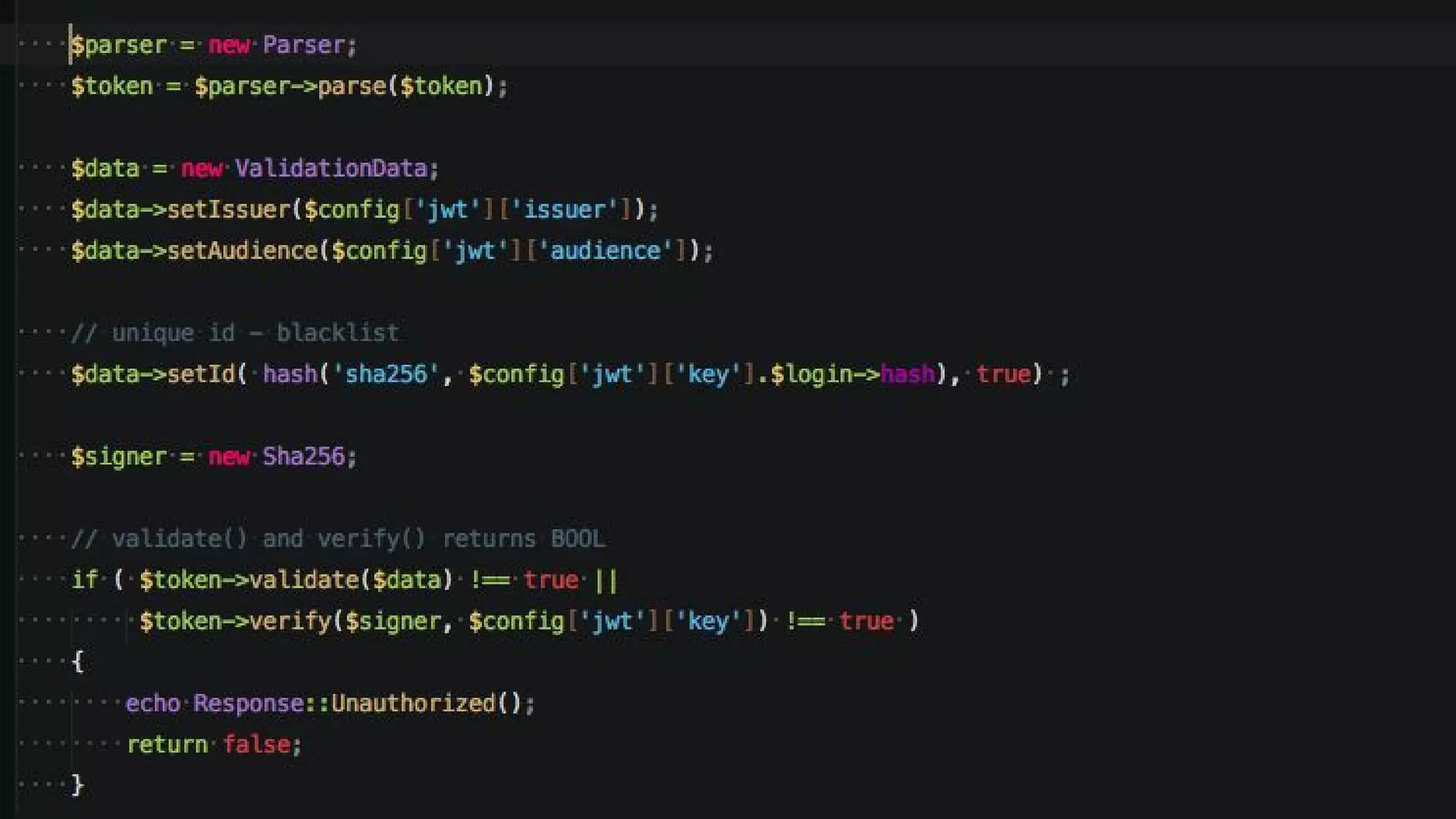
Ivan Rosolen is an expert in information systems and project management, with over 15 years of experience in development, focusing on JSON Web Tokens (JWT) for authentication and authorization. The document details aspects of JWT, including its structure, advantages, security considerations, and how it facilitates stateless authentication. It also includes code references, usage examples, and numerous resources for further learning on JWT and related technologies.