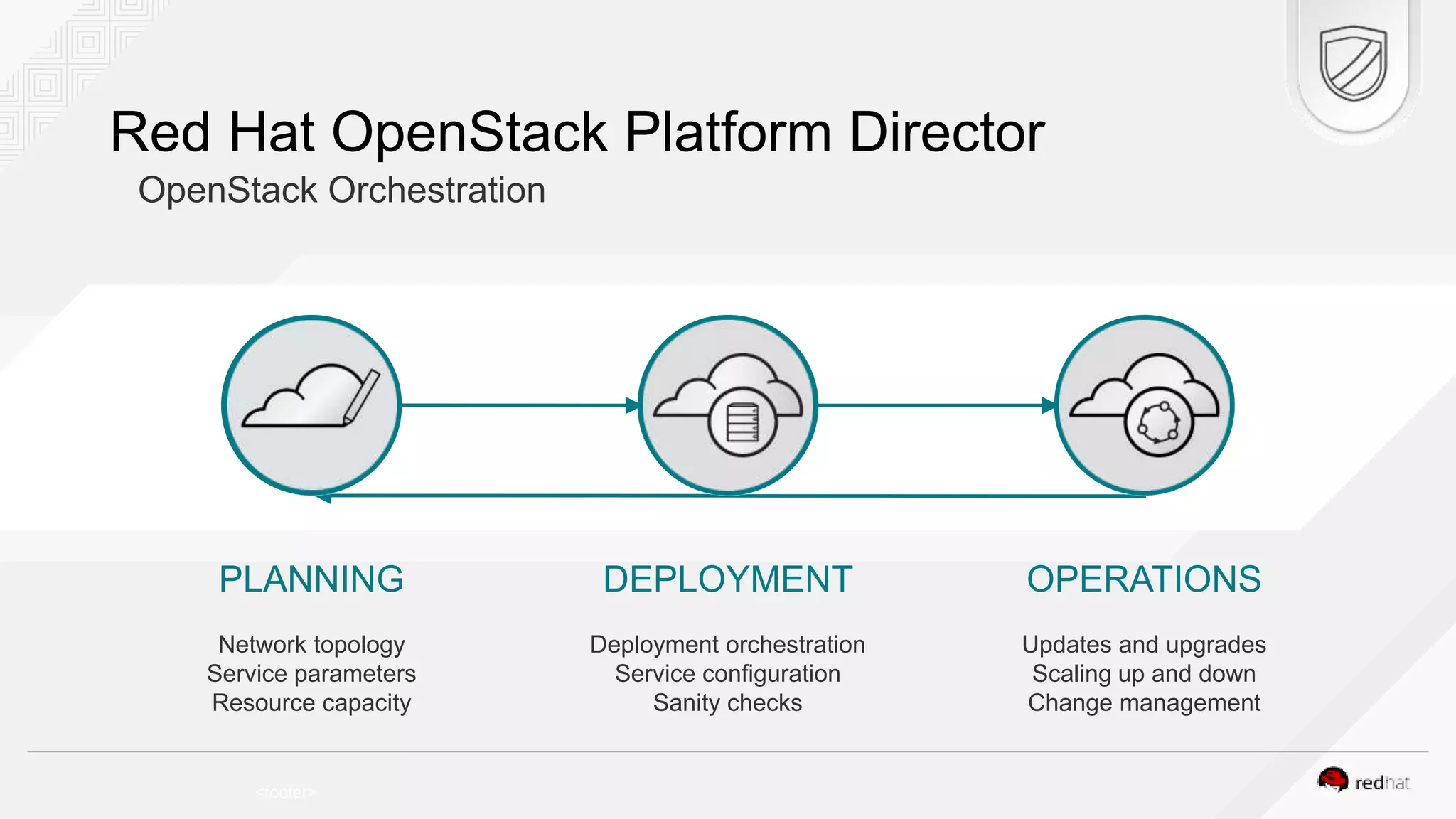
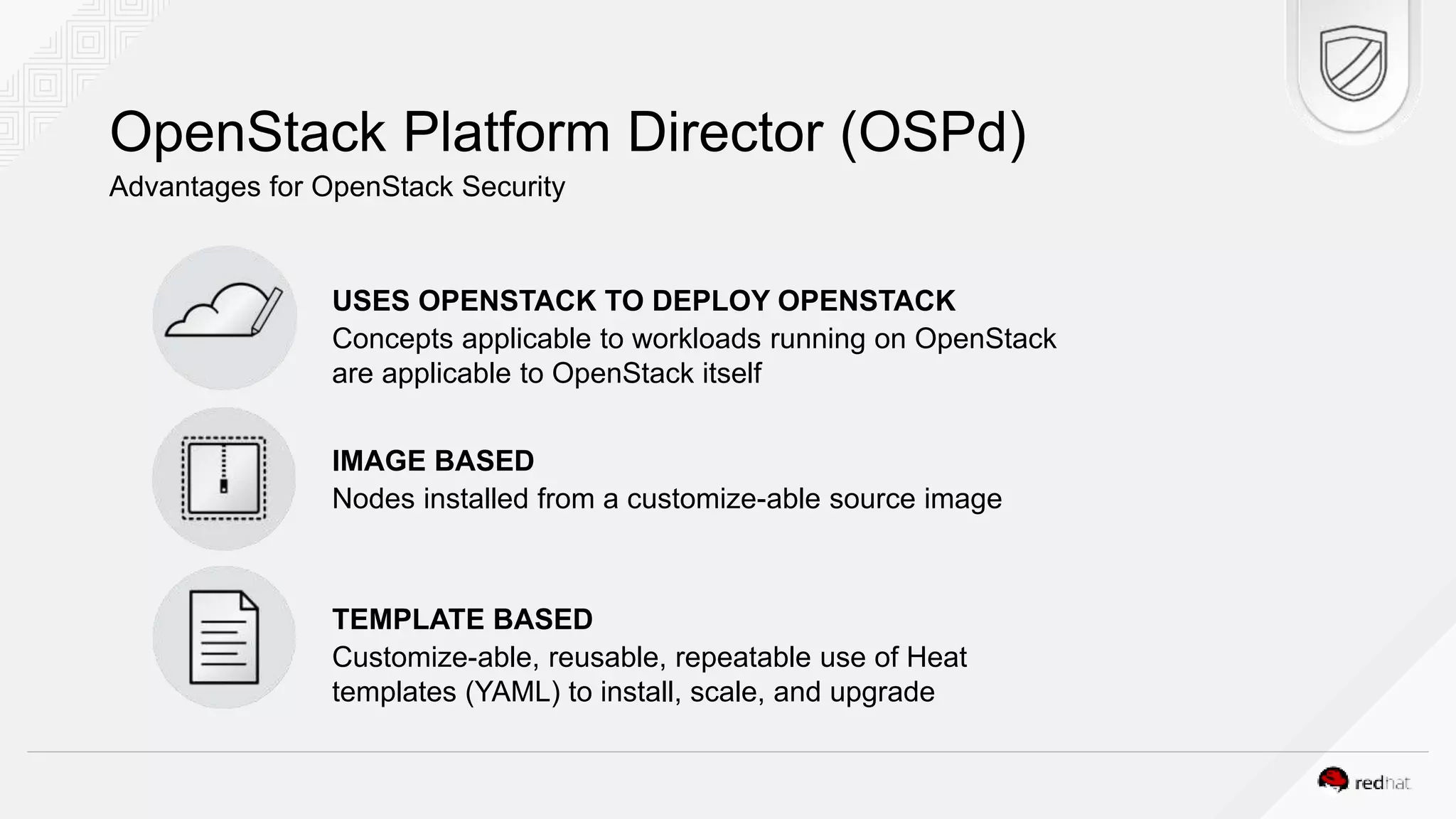
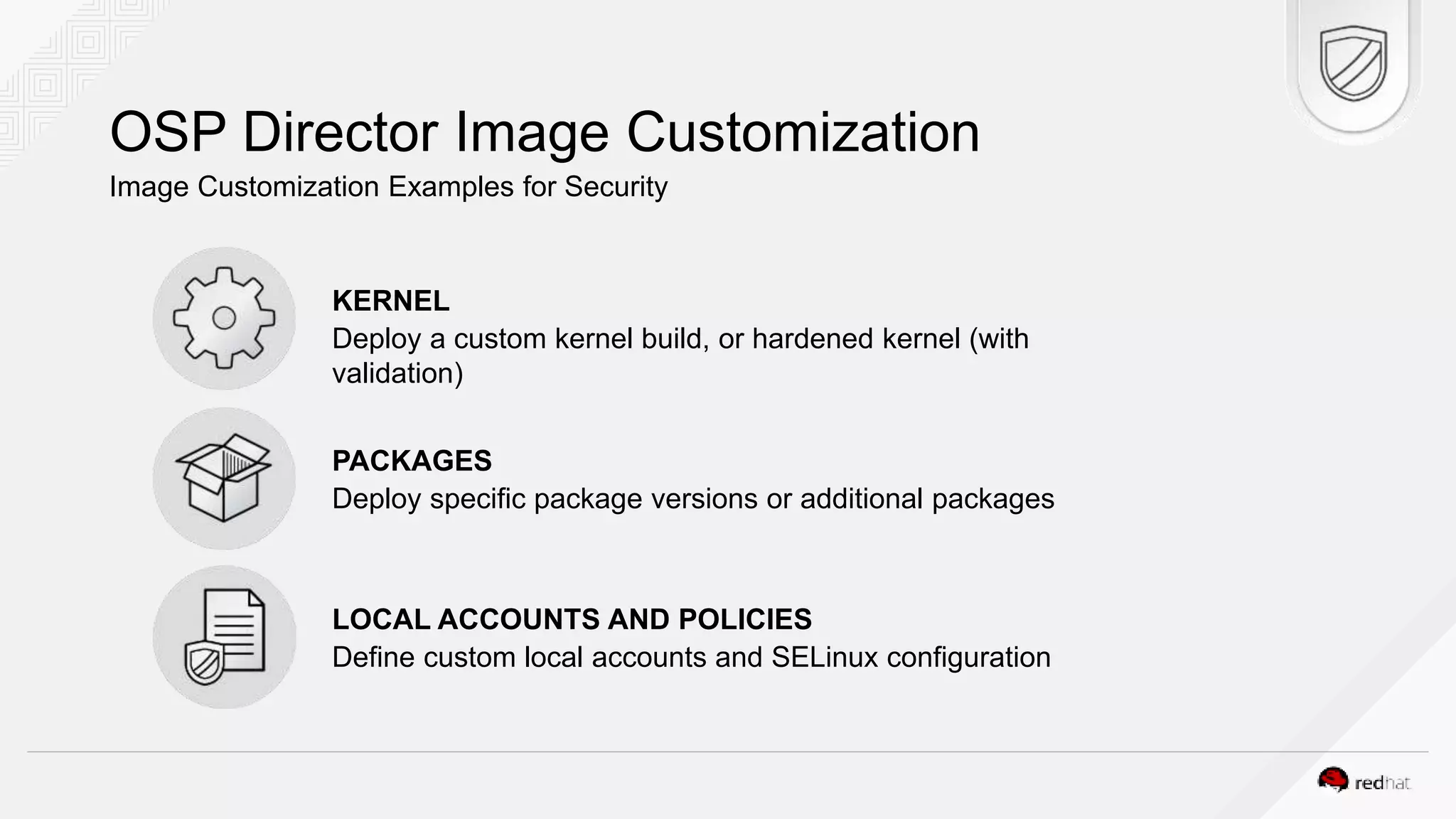
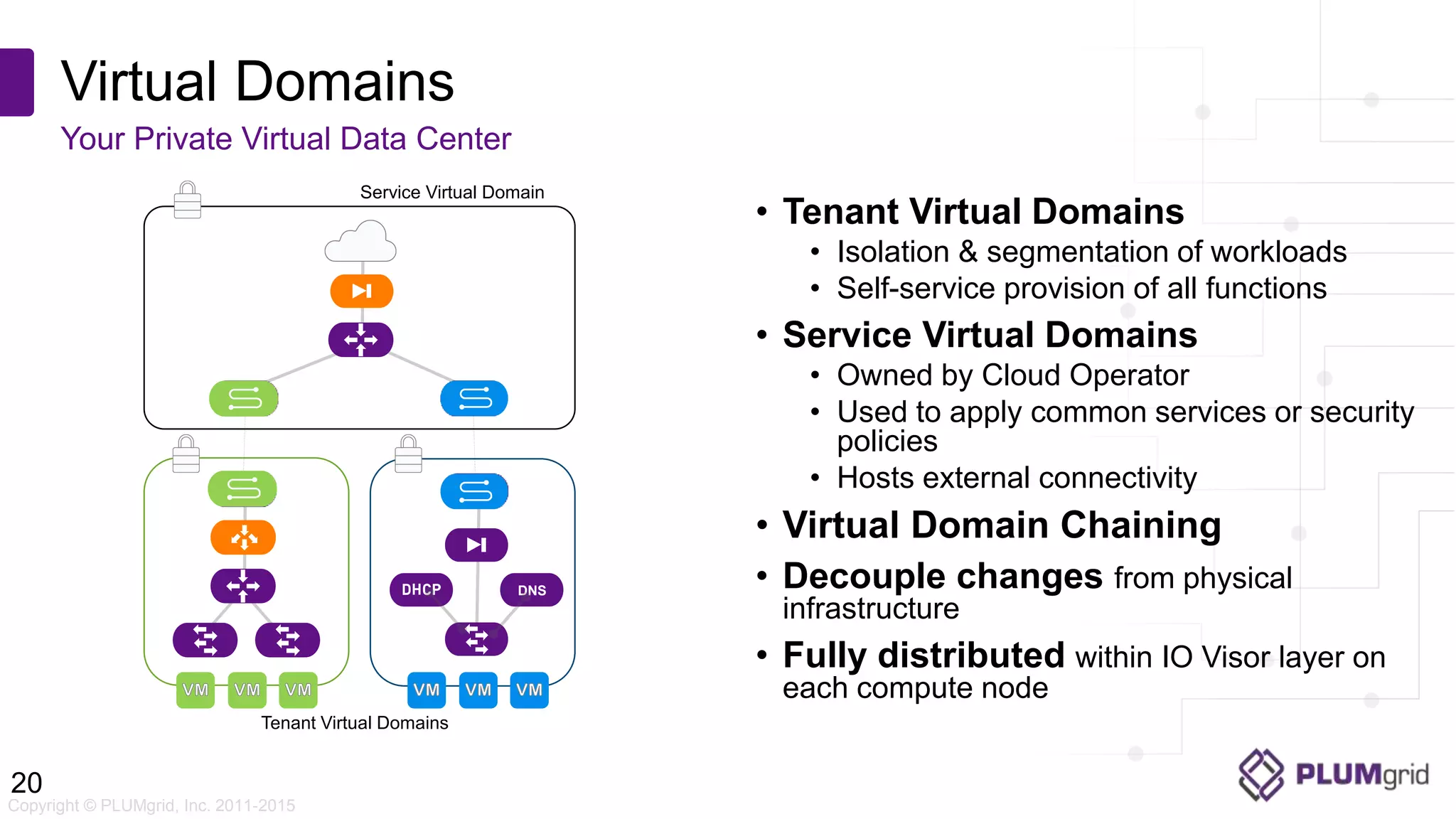
This document discusses using Red Hat OpenStack Platform and micro-segmentation to securely deploy financial services clouds. It covers common OpenStack security challenges, how Red Hat OpenStack Platform addresses these challenges through automation and templates, and how micro-segmentation provides isolation and strict access controls. The presentation then demonstrates micro-segmentation using virtual domains to separate workloads and apply fine-grained security policies in a demo.