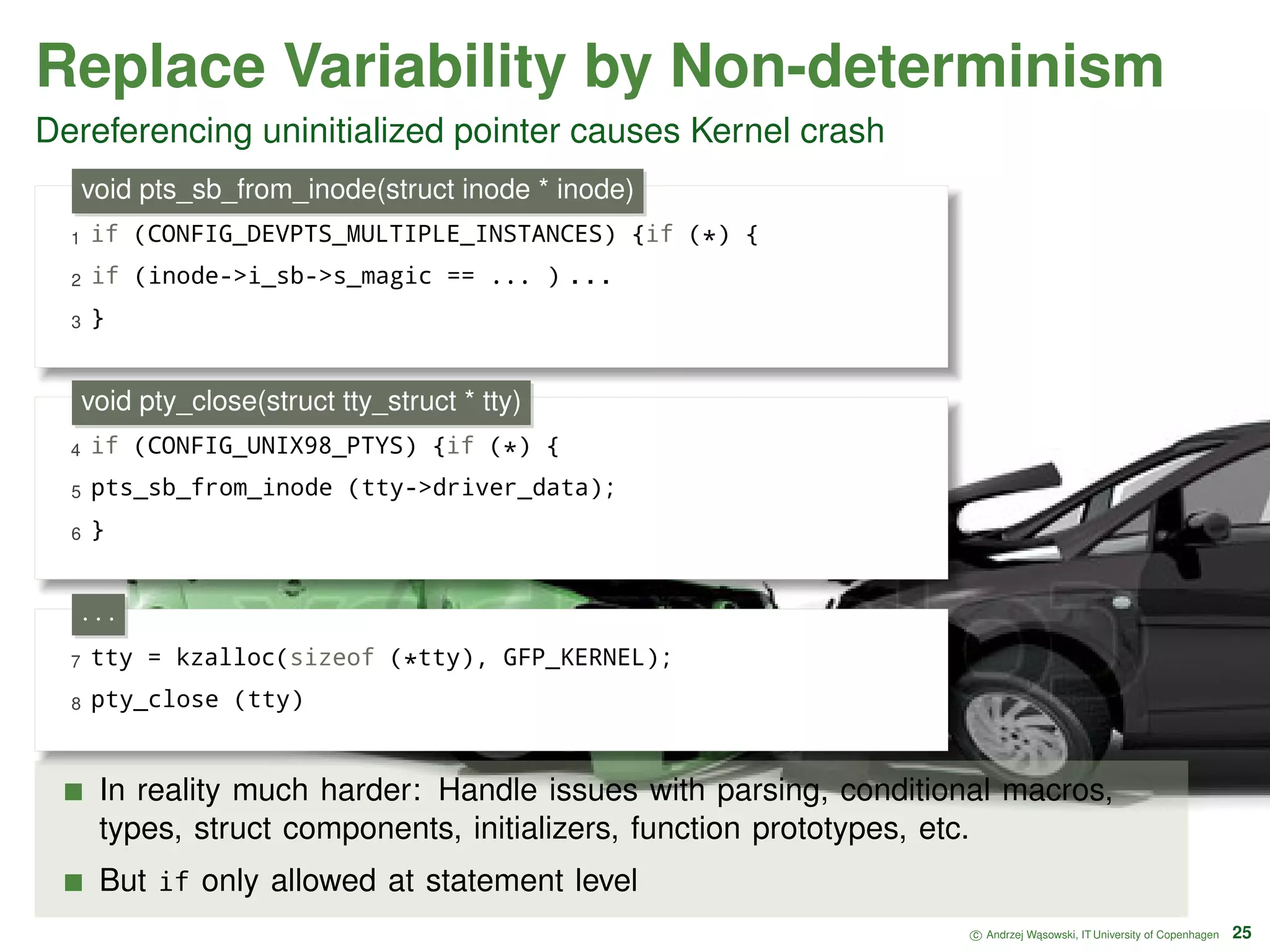
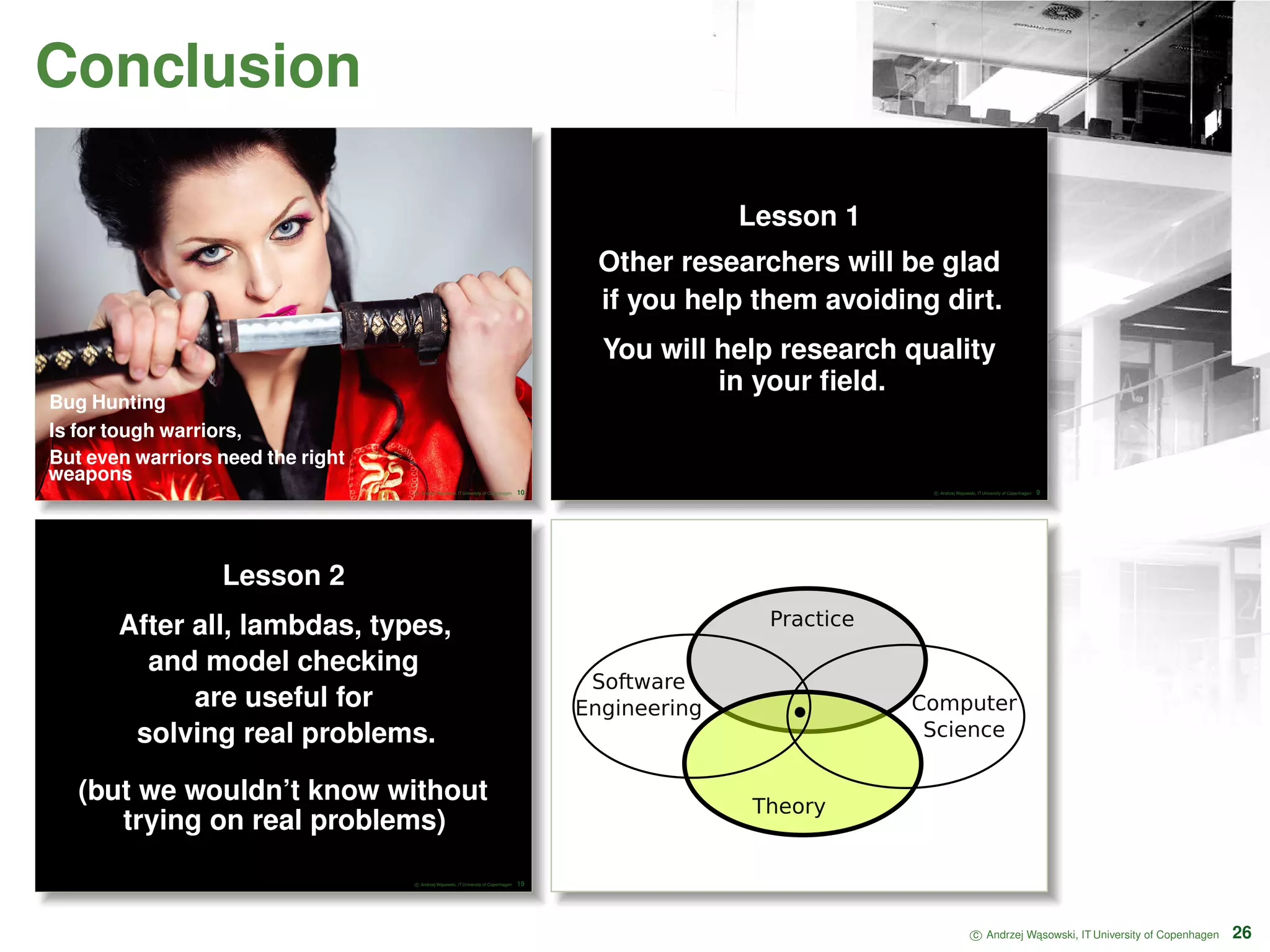
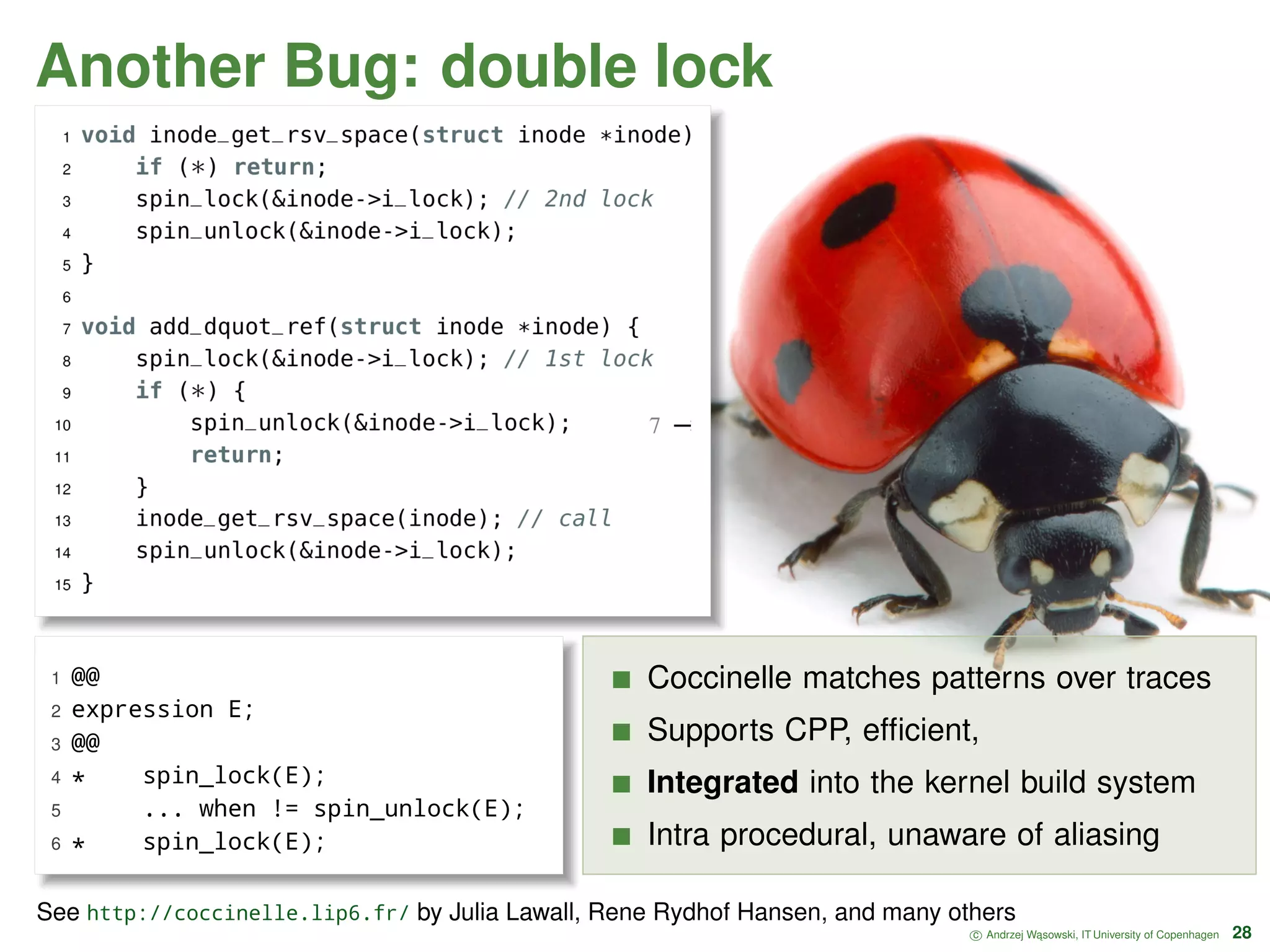
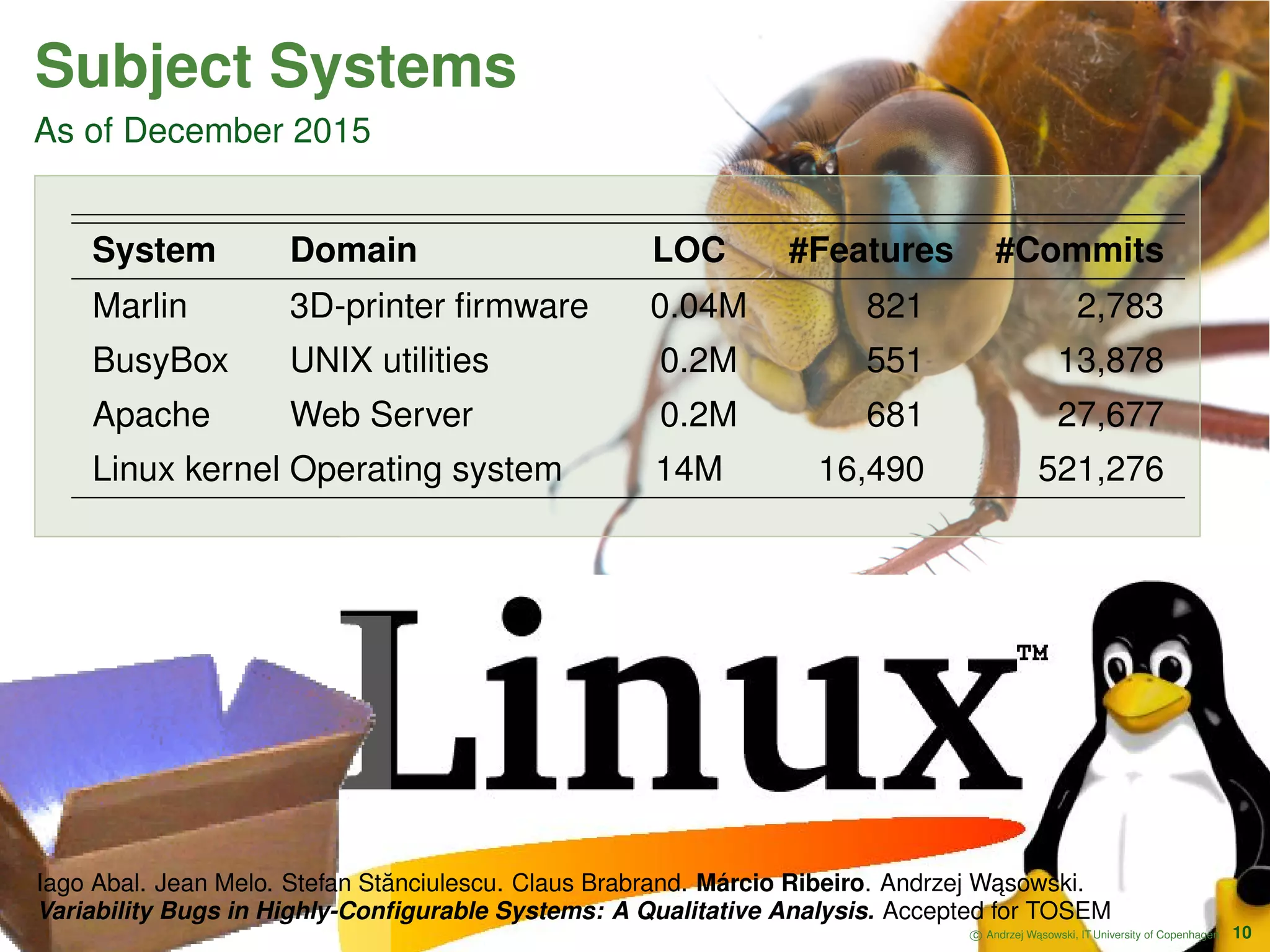
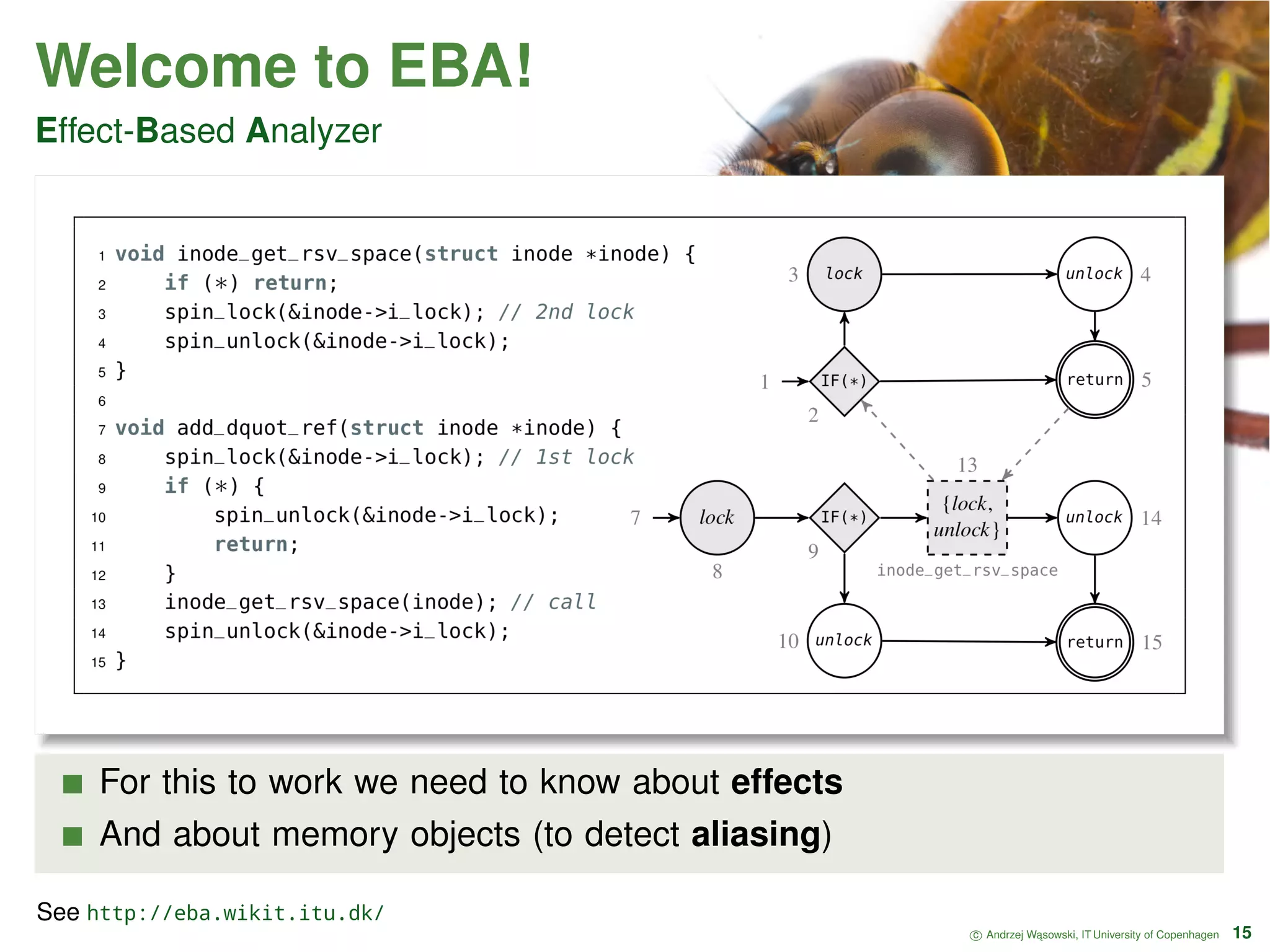
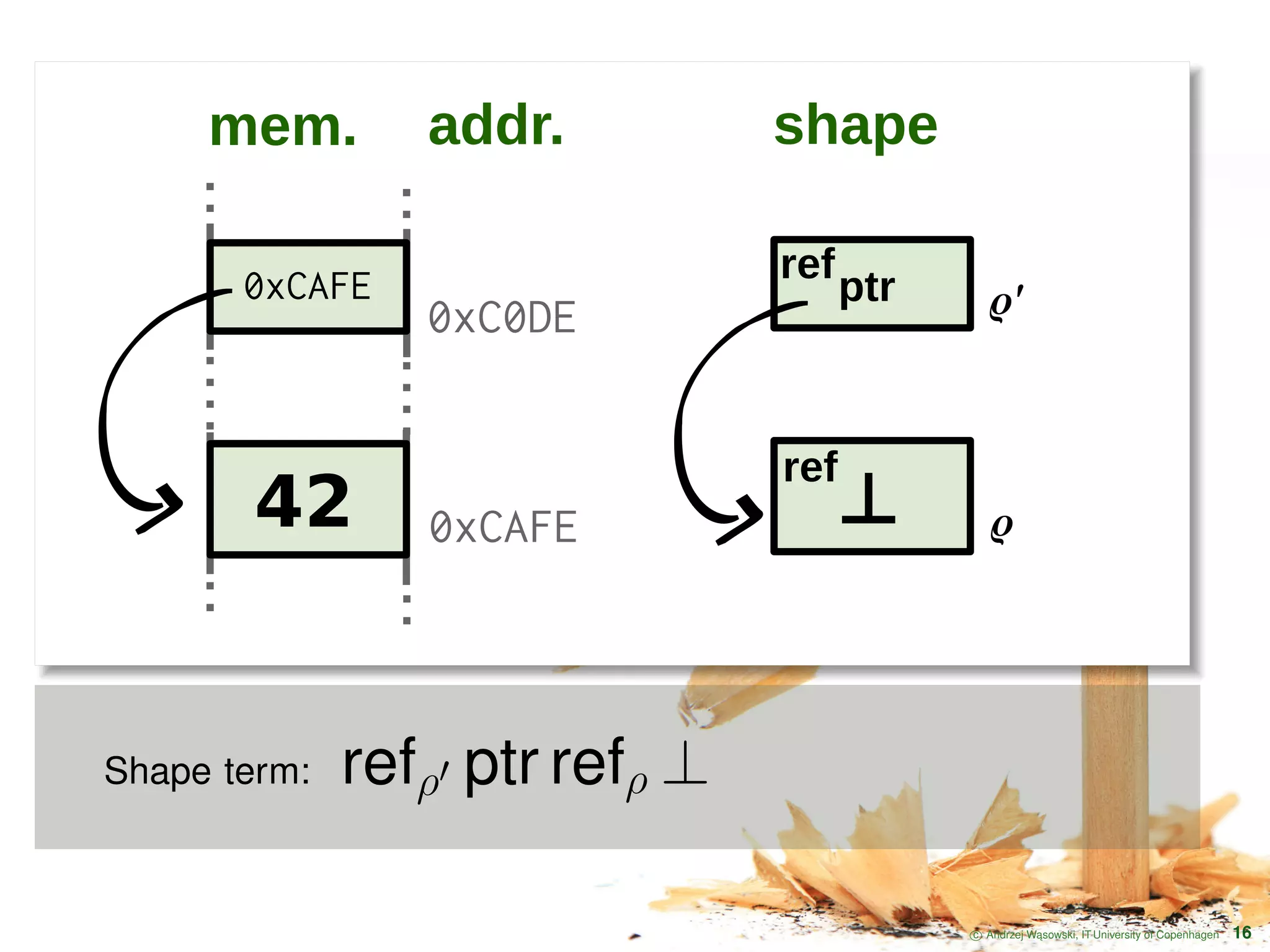
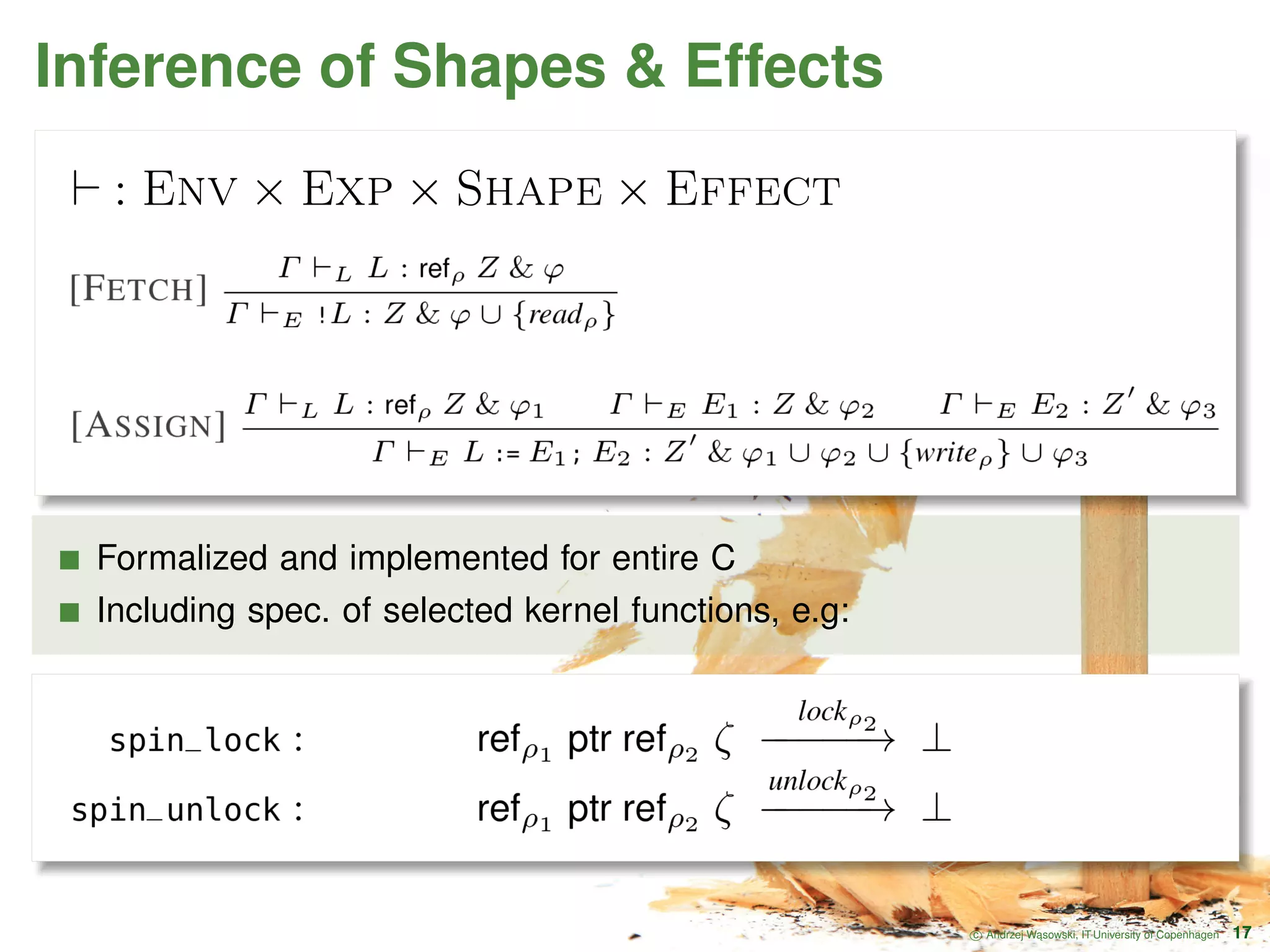
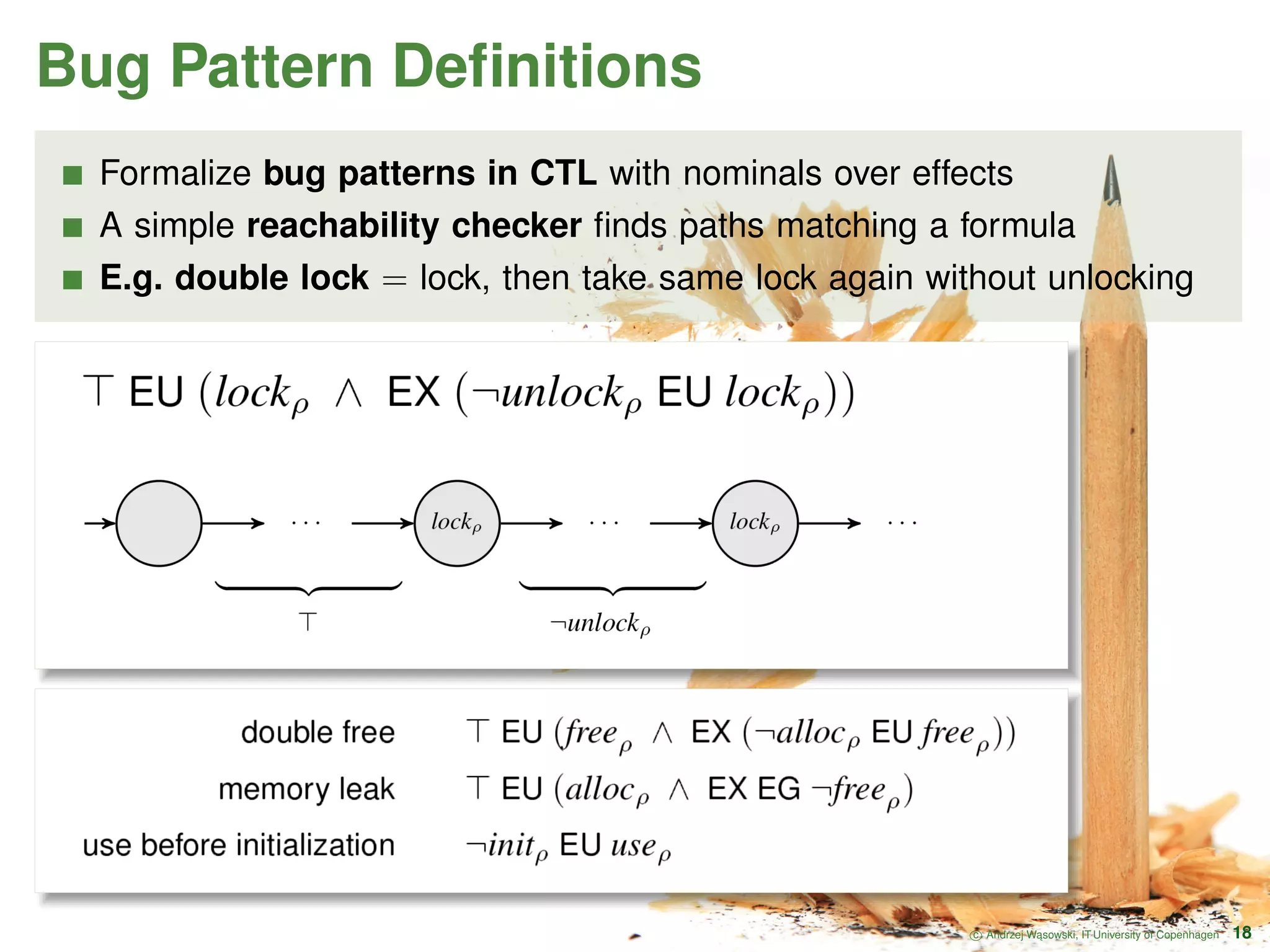
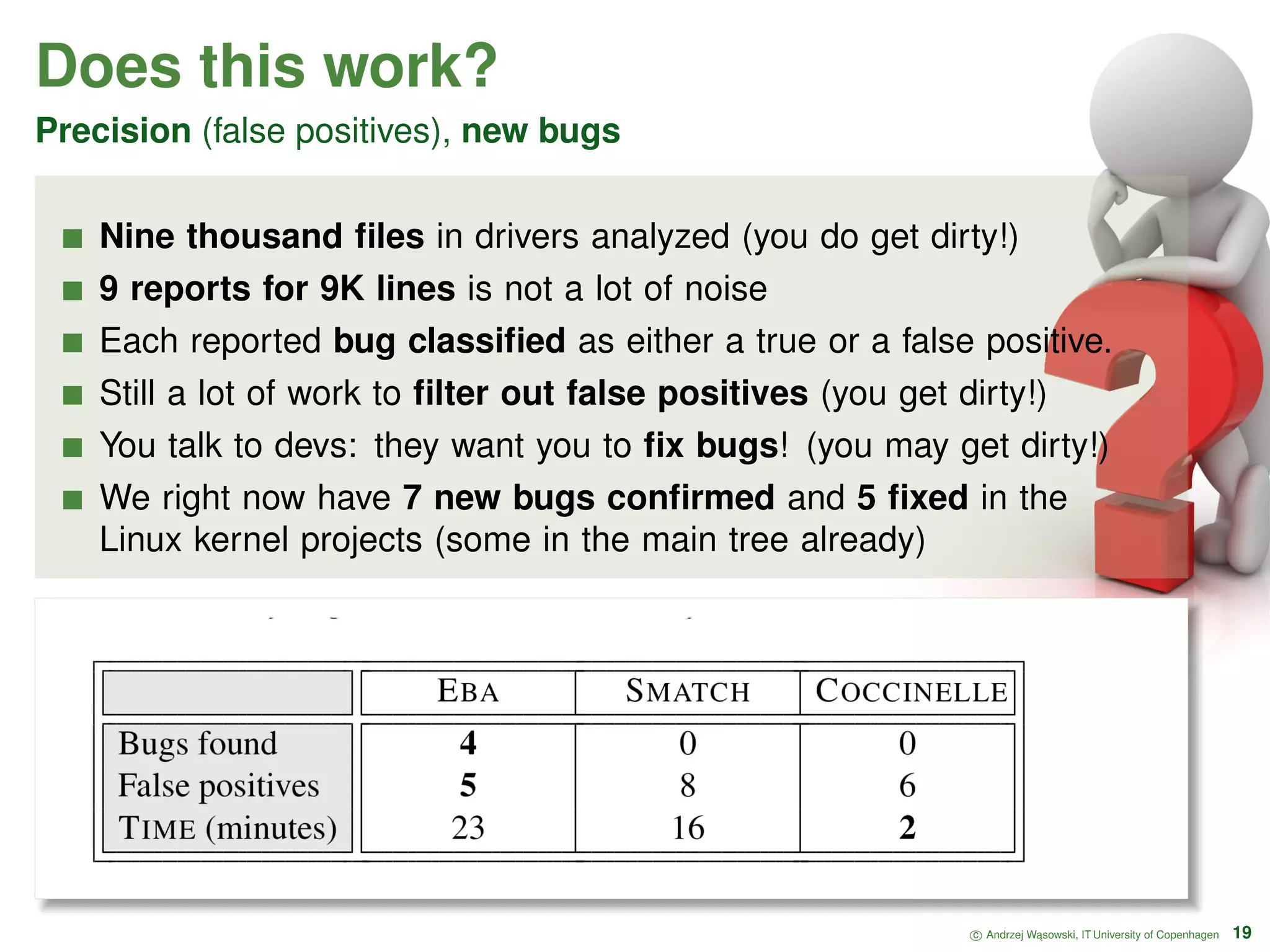
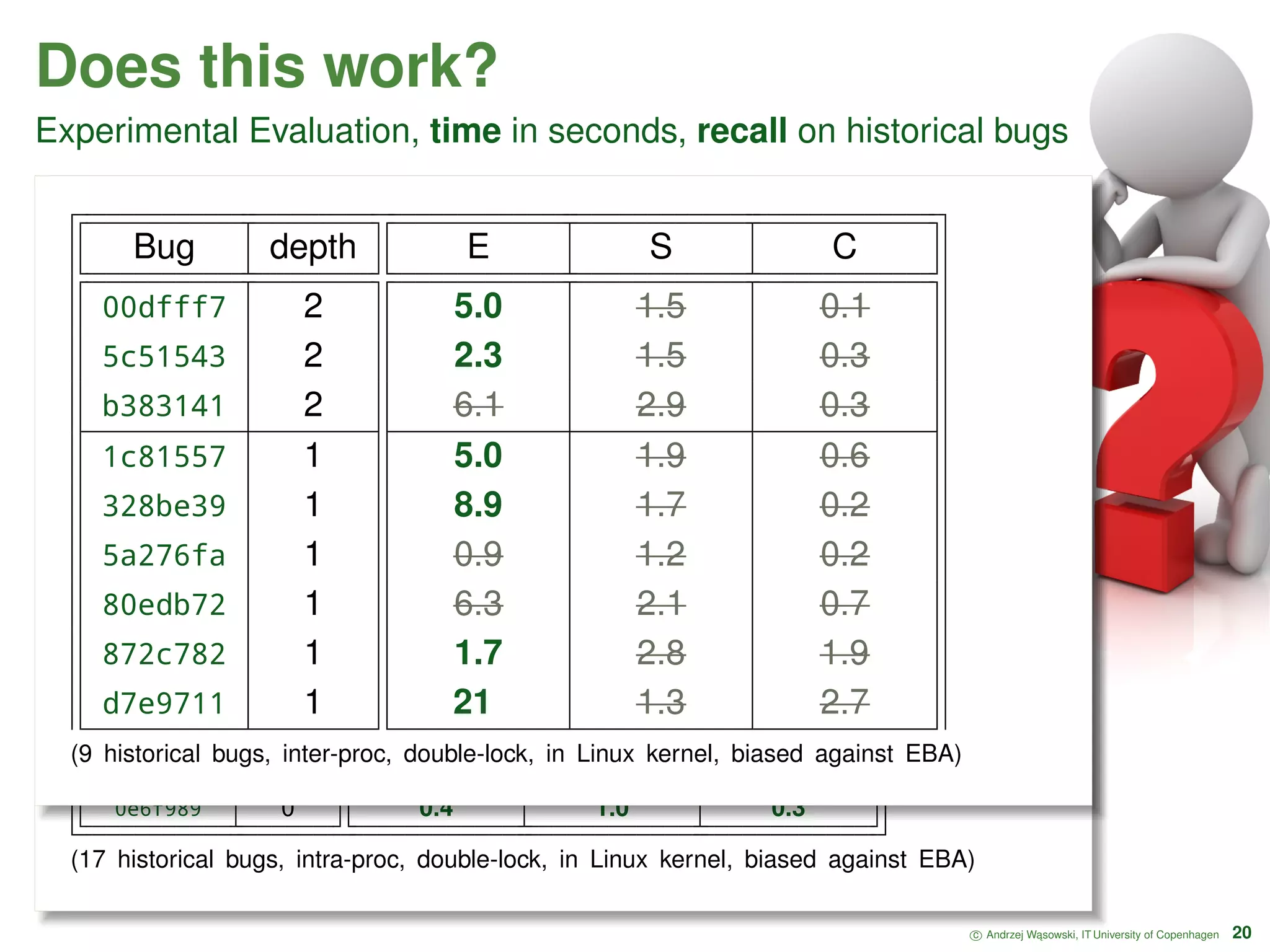
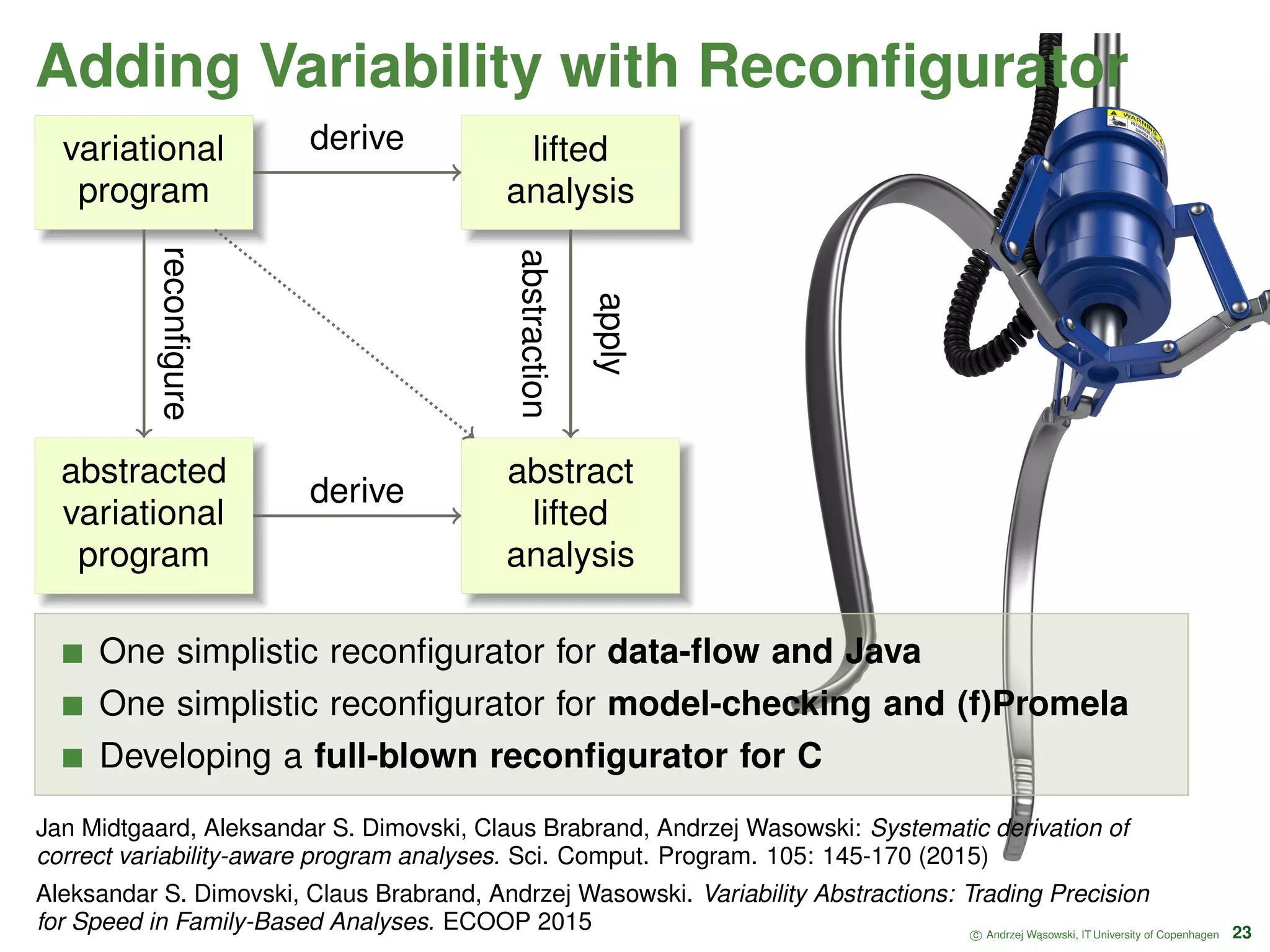
This document discusses finding bugs in Linux kernel code using type-and-effect abstraction. It describes how type and effect inference can be used to model Linux kernel code and detect bugs related to memory safety, data races, and other issues. The approach has been implemented in a tool called the Effect-Based Analyzer (EBA) and has found several new bugs in Linux driver code. Handling preprocessor directives (#ifdefs) is important for analyzing highly-configurable systems like the Linux kernel and is an area of ongoing work.
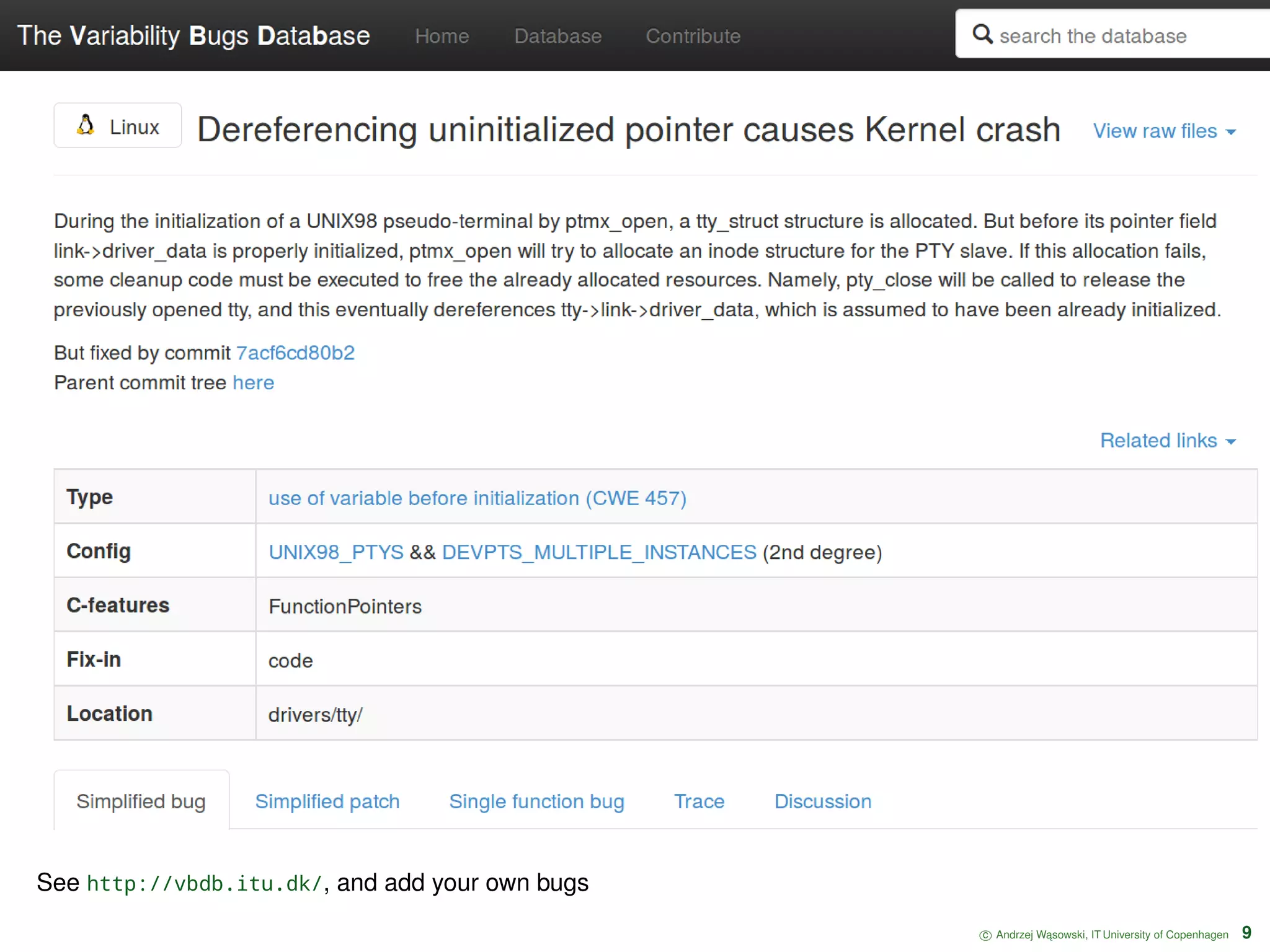
![Let’s look at a bug Dereferencing uninitialized pointer causes Kernel crash 1 #ifdef CONFIG_DEVPTS_MULTIPLE_INSTANCES 2 if (inode->i_sb->s_magic == ... ) . . . 3 #endif void pts_sb_from_inode(struct inode * inode) 4 #ifdef CONFIG_UNIX98_PTYS 5 pts_sb_from_inode (tty->driver_data); 6 #endif void pty_close(struct tty_struct * tty) 7 tty = kzalloc(sizeof (*tty), GFP_KERNEL); 8 pty_close (tty) · · · Domain knowledge Data flow Inter-procedural data-flow Pointers Nested structs [real bug] cross compilation unit and subsystem [real bug] function pointers (pty_close) c Andrzej W ˛asowski, IT University of Copenhagen 4 Bug 7acf6cd, see http://vbdb.itu.dk/#bug/linux/7acf6cd Iago Abal, Claus Brabrand, Andrzej Wasowski. 42 variability bugs in the Linux kernel: a qualitative analysis. ASE 2014: 421-432 + journal submission](https://image.slidesharecdn.com/sbcars-170920184901/75/Finding-Resource-Manipulation-Bugs-in-Linux-Code-4-2048.jpg)
![Let’s look at another bug Control-flow Unsafe casts help generic programing of data structures Type casts, pointers to ints; Do not loose shapes and aliasing info Function pointers used heavily (OO) Inter-procedural data-flow not possible without control-flow [elsewhere] conditional struct components (with incompatible casts) c Andrzej W ˛asowski, IT University of Copenhagen 5 Bug 657e964e74](https://image.slidesharecdn.com/sbcars-170920184901/75/Finding-Resource-Manipulation-Bugs-in-Linux-Code-5-2048.jpg)



![Let’s look at a bug Dereferencing uninitialized pointer causes Kernel crash 1 #ifdef CONFIG_DEVPTS_MULTIPLE_INSTANCES 2 if (inode->i_sb->s_magic == ... ) . . . 3 #endif void pts_sb_from_inode(struct inode * inode) 4 #ifdef CONFIG_UNIX98_PTYS 5 pts_sb_from_inode (tty->driver_data); 6 #endif void pty_close(struct tty_struct * tty) 7 tty = kzalloc(sizeof (*tty), GFP_KERNEL); 8 pty_close (tty) · · · Domain knowledge Data flow Inter-procedural data-flow Pointers Nested structs [real bug] cross compilation unit and subsystem [real bug] function pointers (pty_close) c Andrzej W ˛asowski, IT University of Copenhagen 24 Bug 7acf6cd, see http://vbdb.itu.dk/#bug/linux/7acf6cd Iago Abal, Claus Brabrand, Andrzej Wasowski. 42 variability bugs in the Linux kernel: a qualitative analysis. ASE 2014: 421-432 + journal submission](https://image.slidesharecdn.com/sbcars-170920184901/75/Finding-Resource-Manipulation-Bugs-in-Linux-Code-24-2048.jpg)