- Notifications
You must be signed in to change notification settings - Fork 282
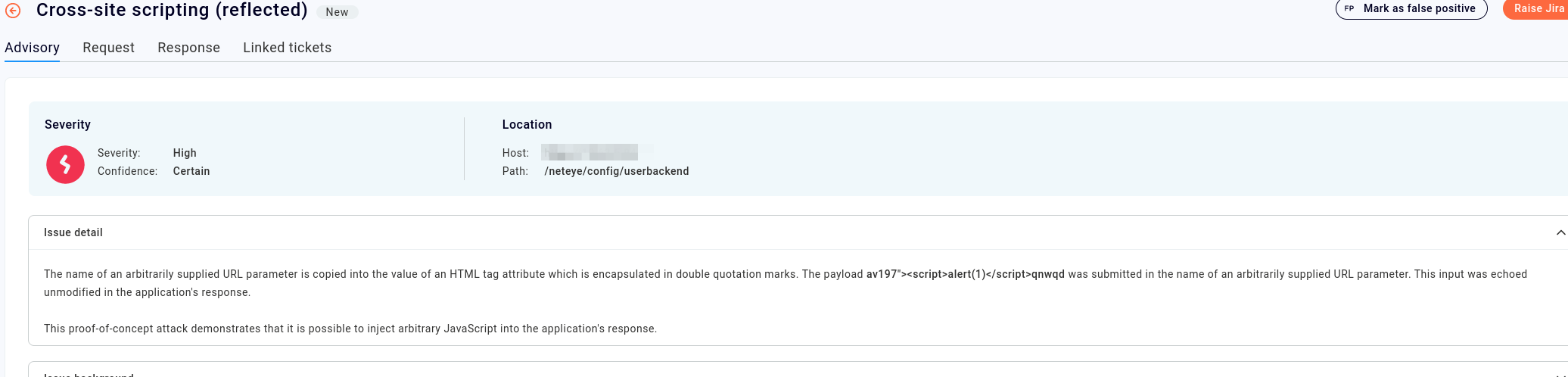
Description
Describe the bug
The /config/userbackend page is vulnerable to XSS (reflected). The url of the request to this page is rendered in the response as it arrives to the server, so an attacker can manipulate the url so that the response triggers the execution of a script.
The vulnerability should be exploitable on older browsers (for example on older versions of IE), while the vulnerability does not seem to be present for modern browsers since they automatically url-encode every url.
This vulnerability was reported by the Burp Suite Vulnerability Scanner:
To Reproduce
- Send an authenticated HTTP request like the following:
GET /config/userbackend?av197"><script>alert(1)</script>qnwqd=1 HTTP/1.1 Host: 10.0.0.1 Accept-Encoding: gzip, deflate Accept: */* Accept-Language: en-US;q=0.9,en;q=0.8 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/107.0.5304.107 Safari/537.36 Connection: close Cache-Control: max-age=0 Cookie: icingaweb2-tzo=3600-0; icingaweb2-session=<value>; Icingaweb2=<value> X-Icinga-Accept: text/html X-Icinga-Container: col1 X-Requested-With: XMLHttpRequest X-Icinga-WindowId: kmweftriogql Content-Type: application/x-www-form-urlencoded; charset=UTF-8 Sec-CH-UA: ".Not/A)Brand";v="99", "Google Chrome";v="107", "Chromium";v="107" Sec-CH-UA-Platform: Windows Sec-CH-UA-Mobile: ?0 - The response includes the following HTML:
<form id="form_reorder_authbackend-kmweftriogql" name="form_reorder_authbackend" enctype="application/x-www-form-urlencoded" method="post" action="/neteye/config/userbackend?av197"><script>alert(1)</script>qnwqd=1"> Expected behavior
The server should escape the parameters of the request so that it avoids possible XSS vulnerabilities
Screenshots
Your Environment
Include as many relevant details about the environment you experienced the problem in
- Icinga Web 2 version and modules (System - About): 2.10.1
- Web browser used:
- Icinga 2 version used (
icinga2 --version): r2.11.9-1 - PHP version used (
php --version): 7.4.30 - Server operating system and version: Red Hat Enterprise Linux release 8.7
Additional context
The instruction which is not sanitizing the input seems to be the following:
https://github.com/Icinga/icingaweb2/blob/master/application/views/scripts/form/reorder-authbackend.phtml#L1