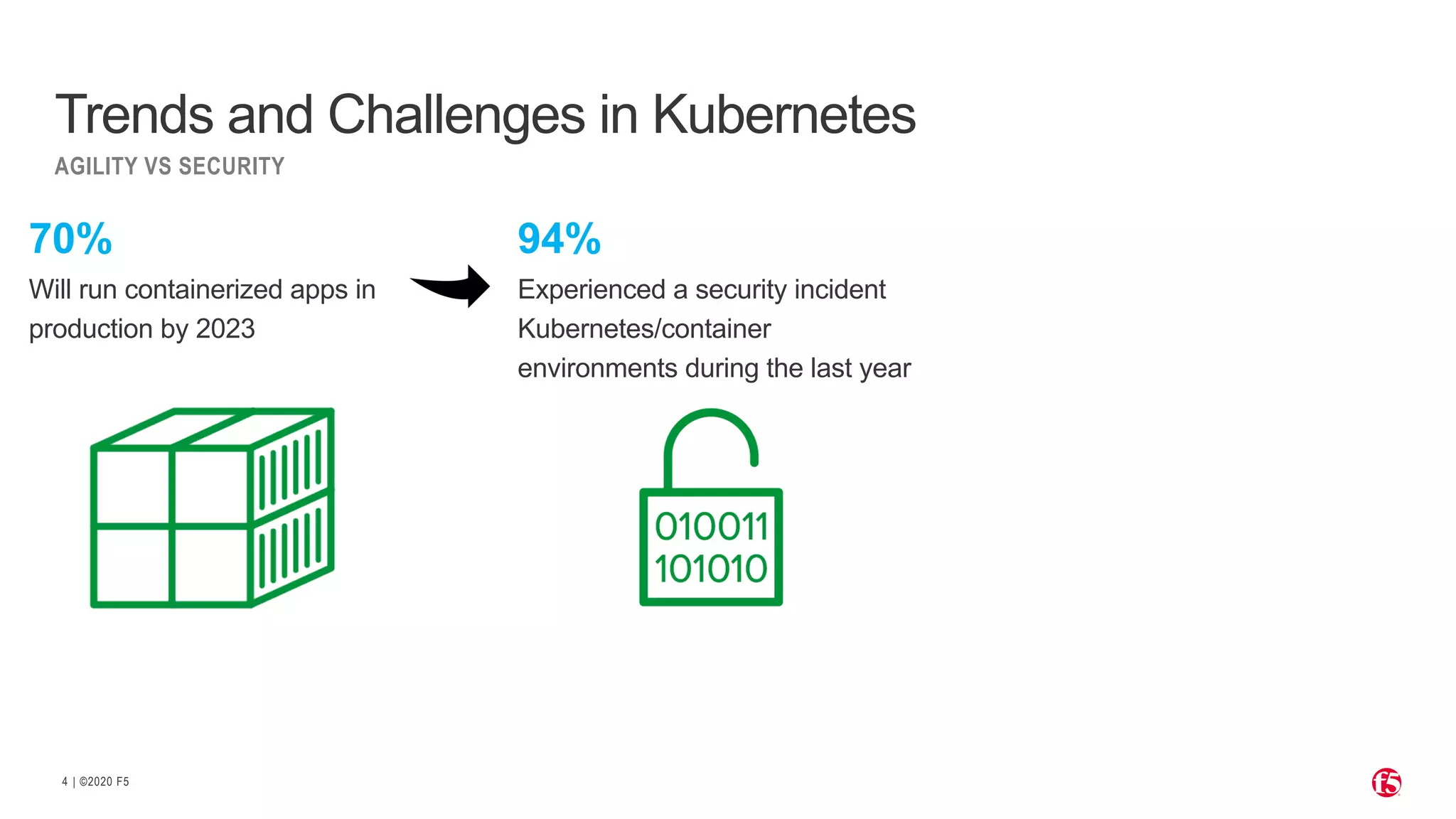
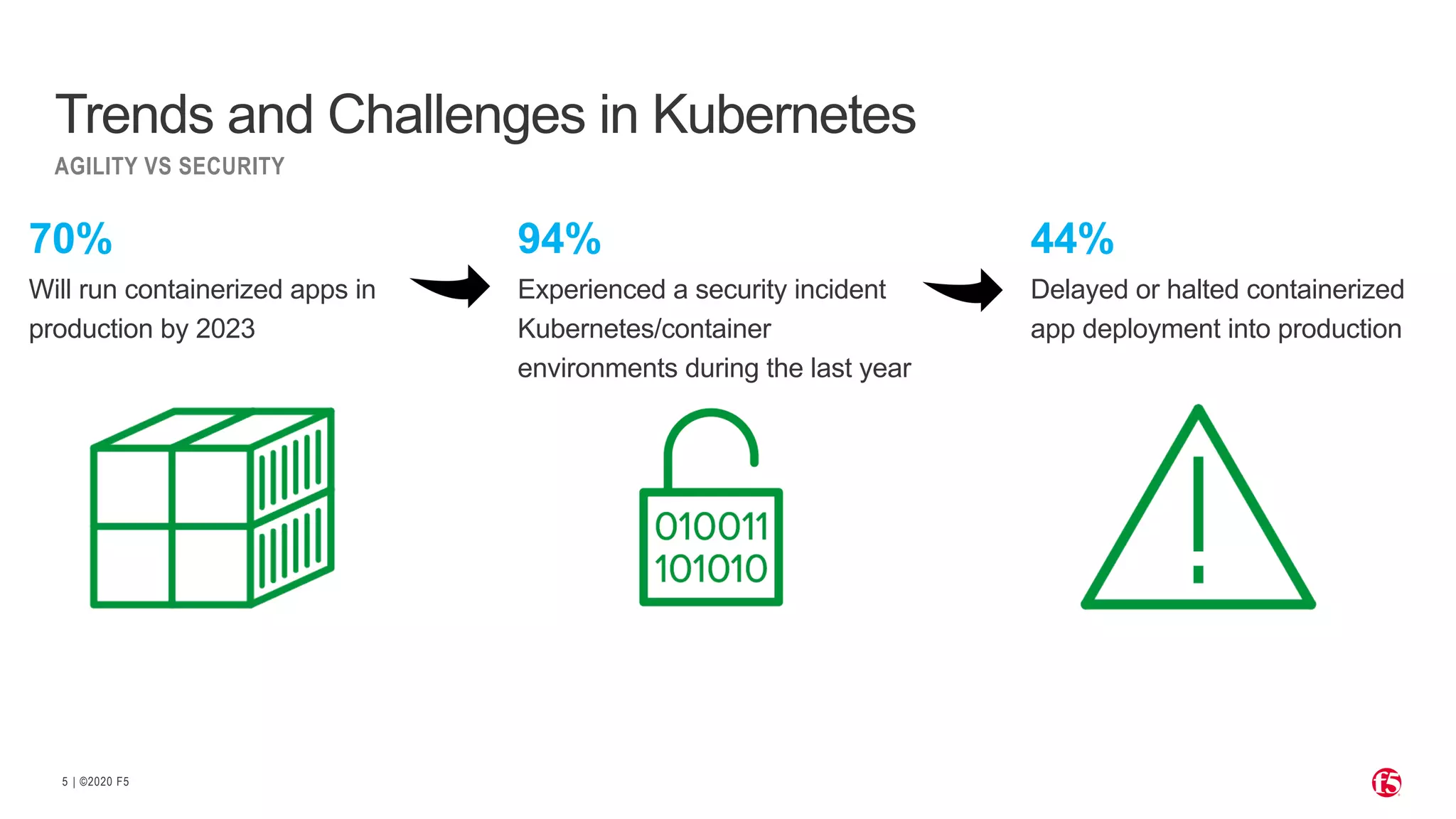
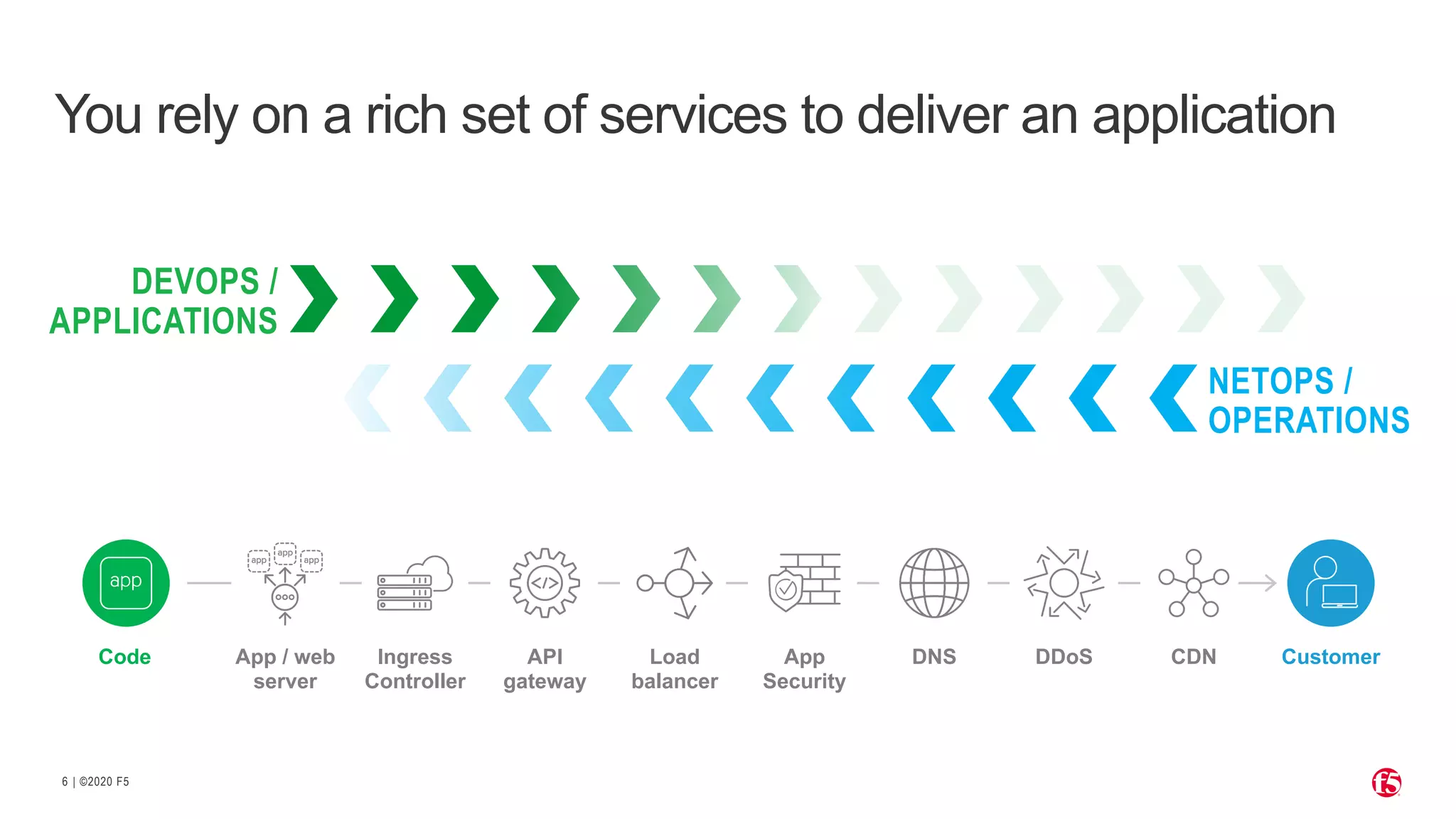
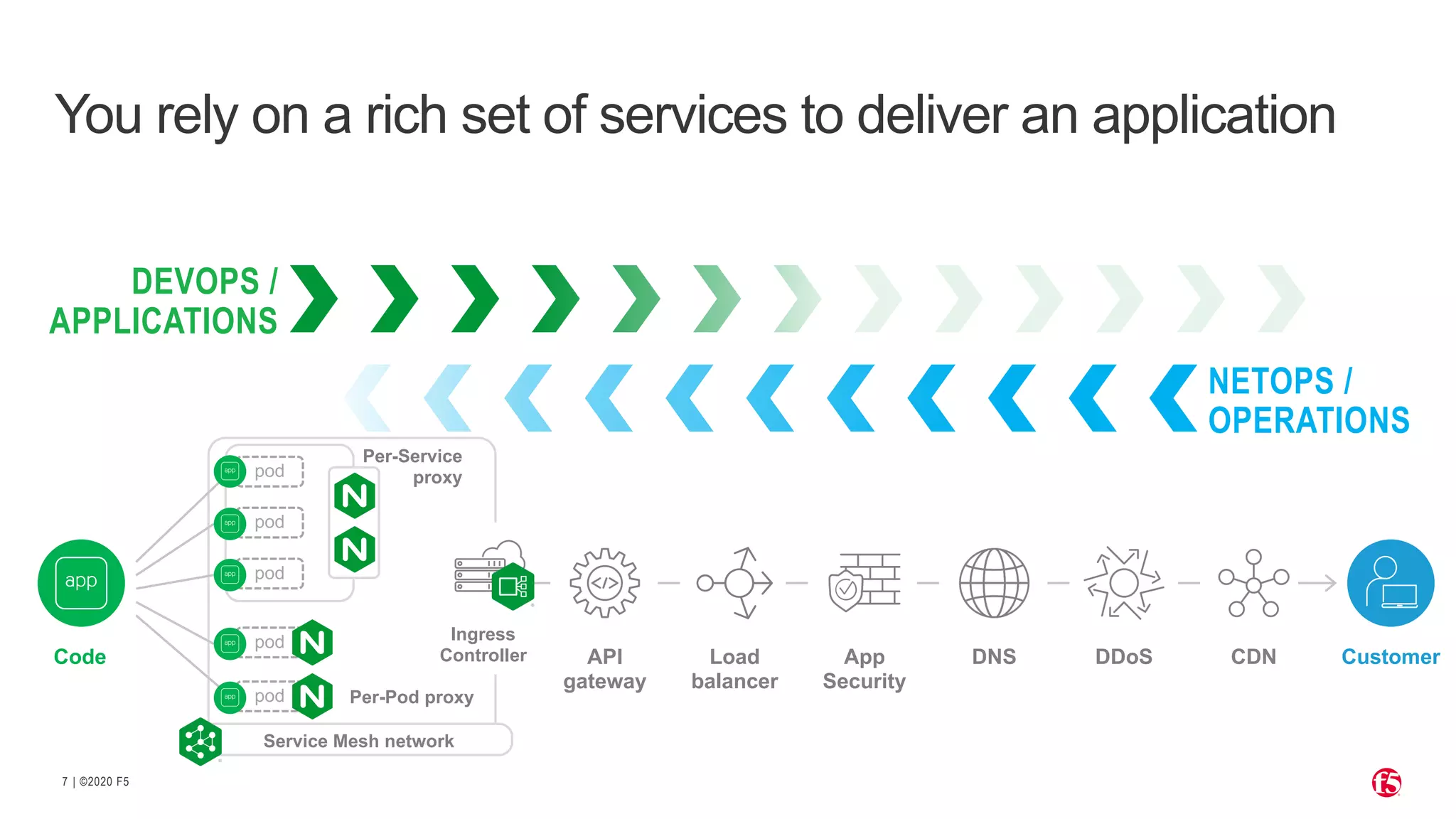
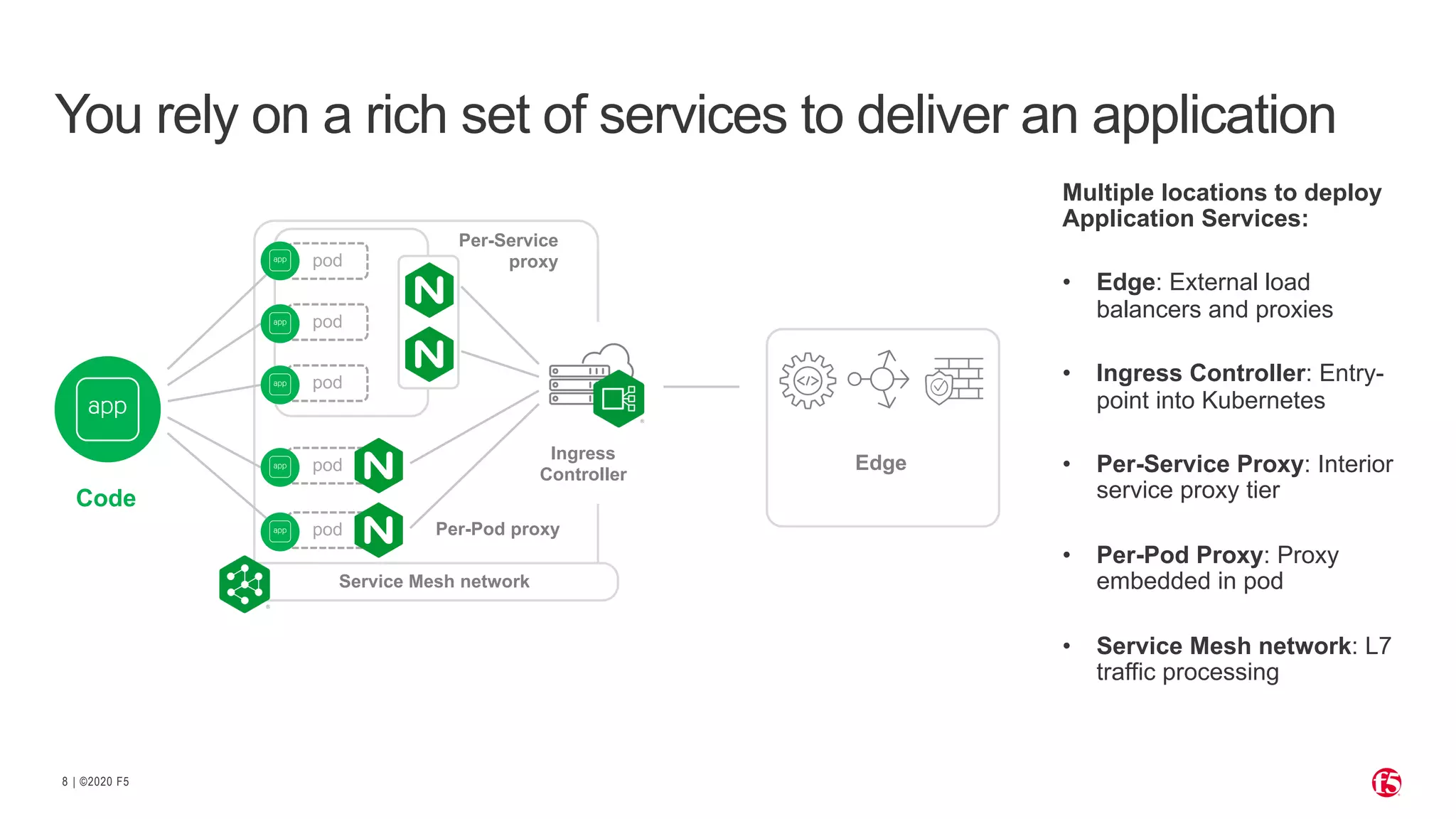
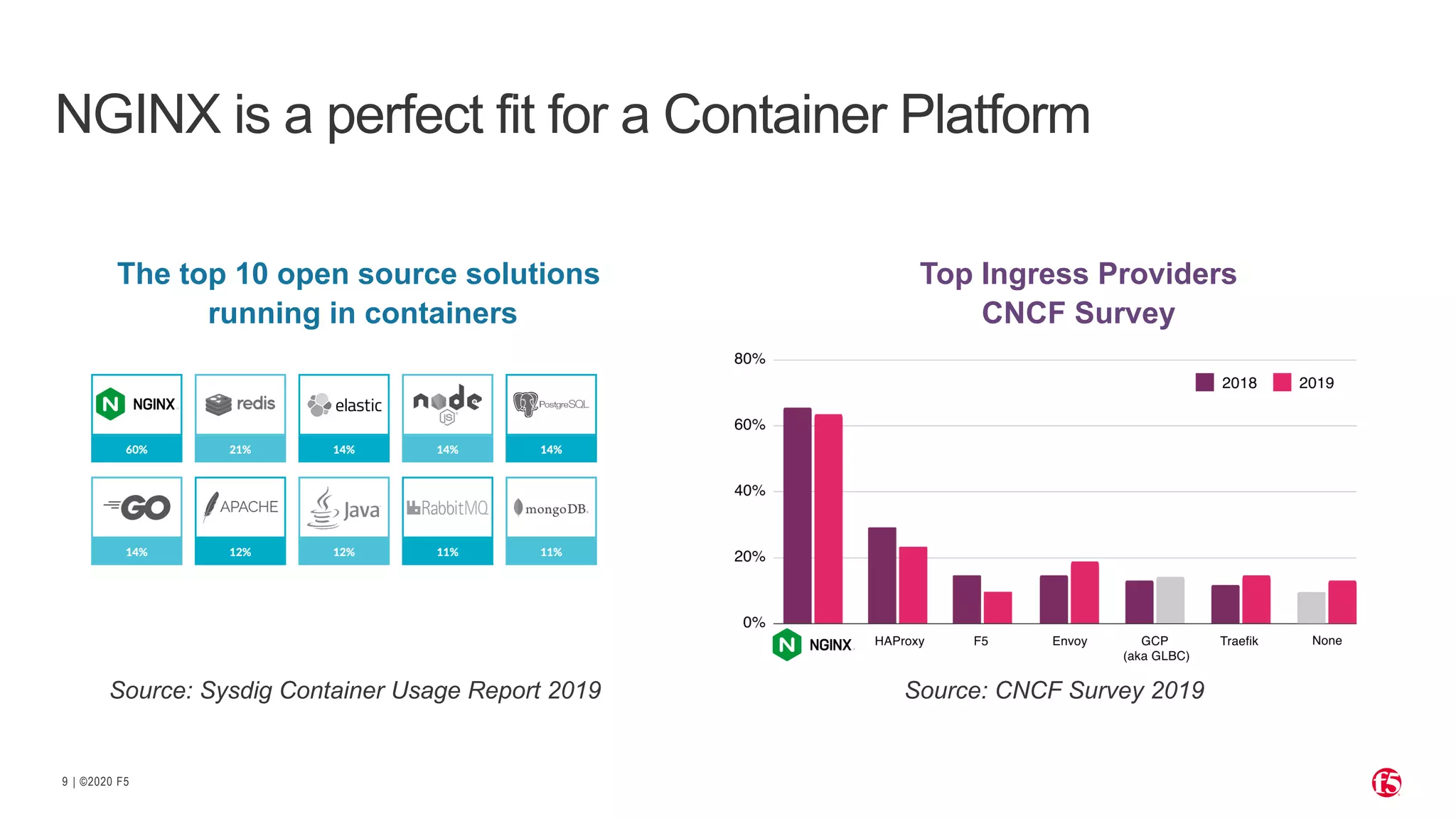
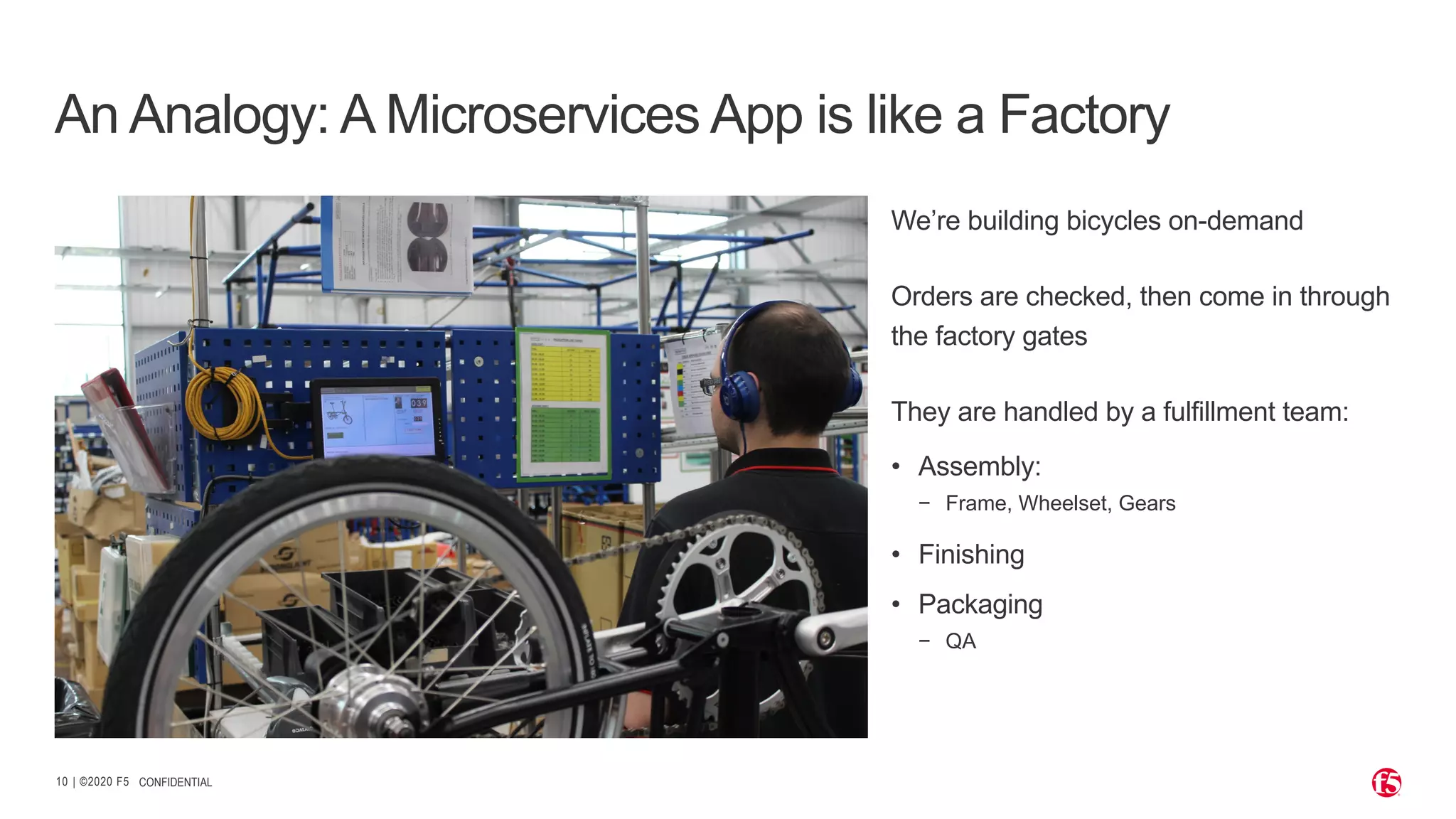
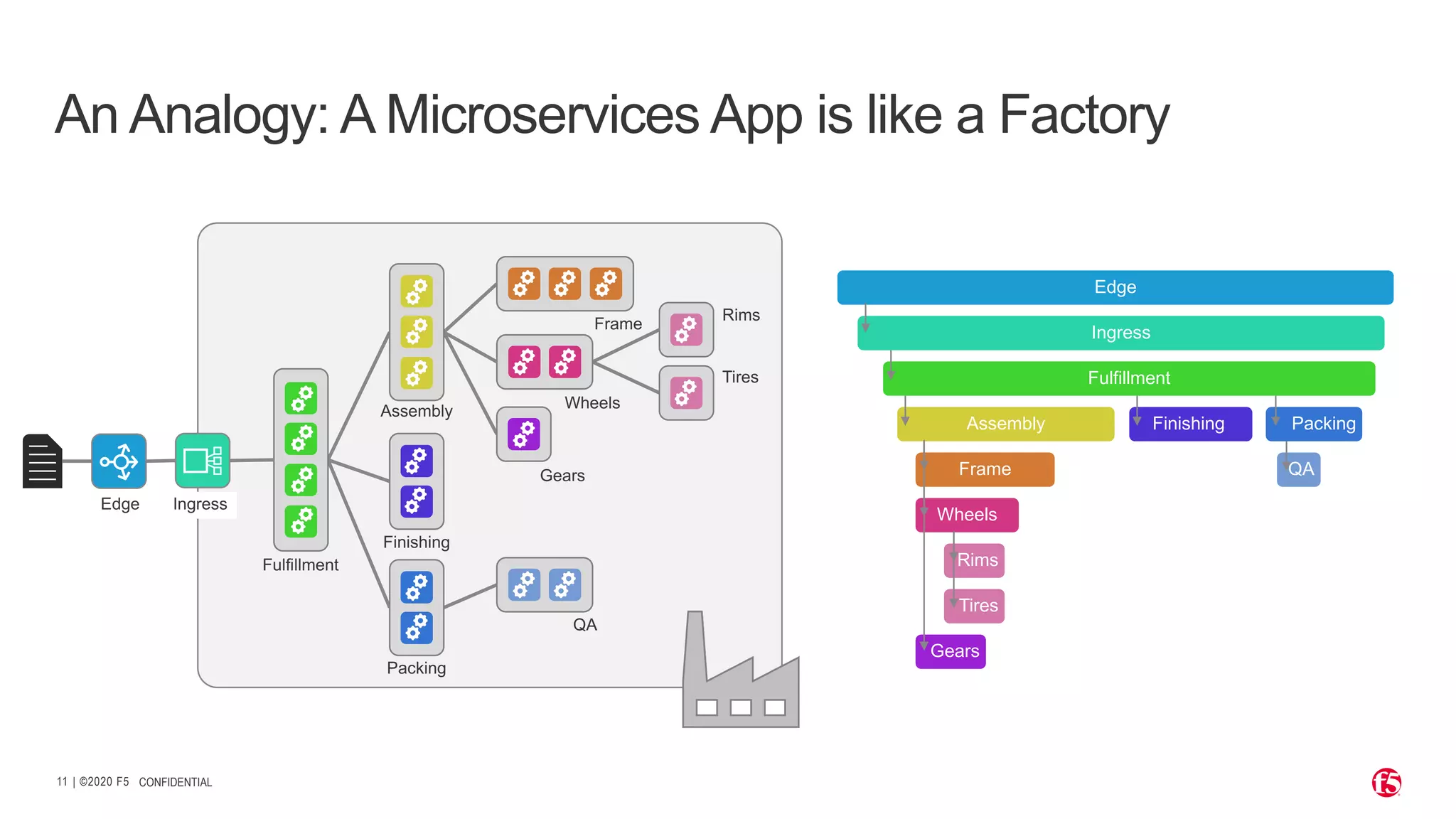
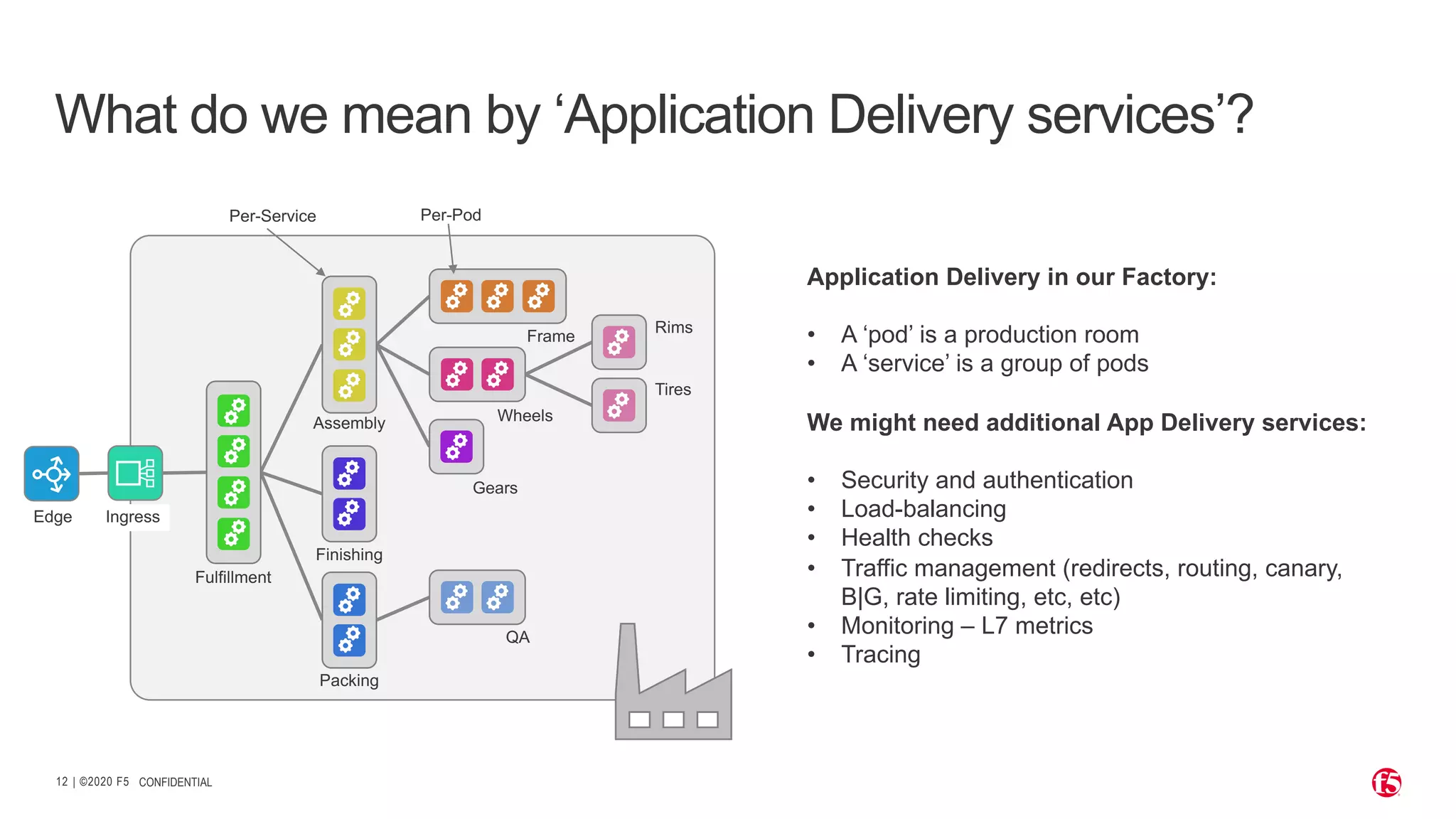
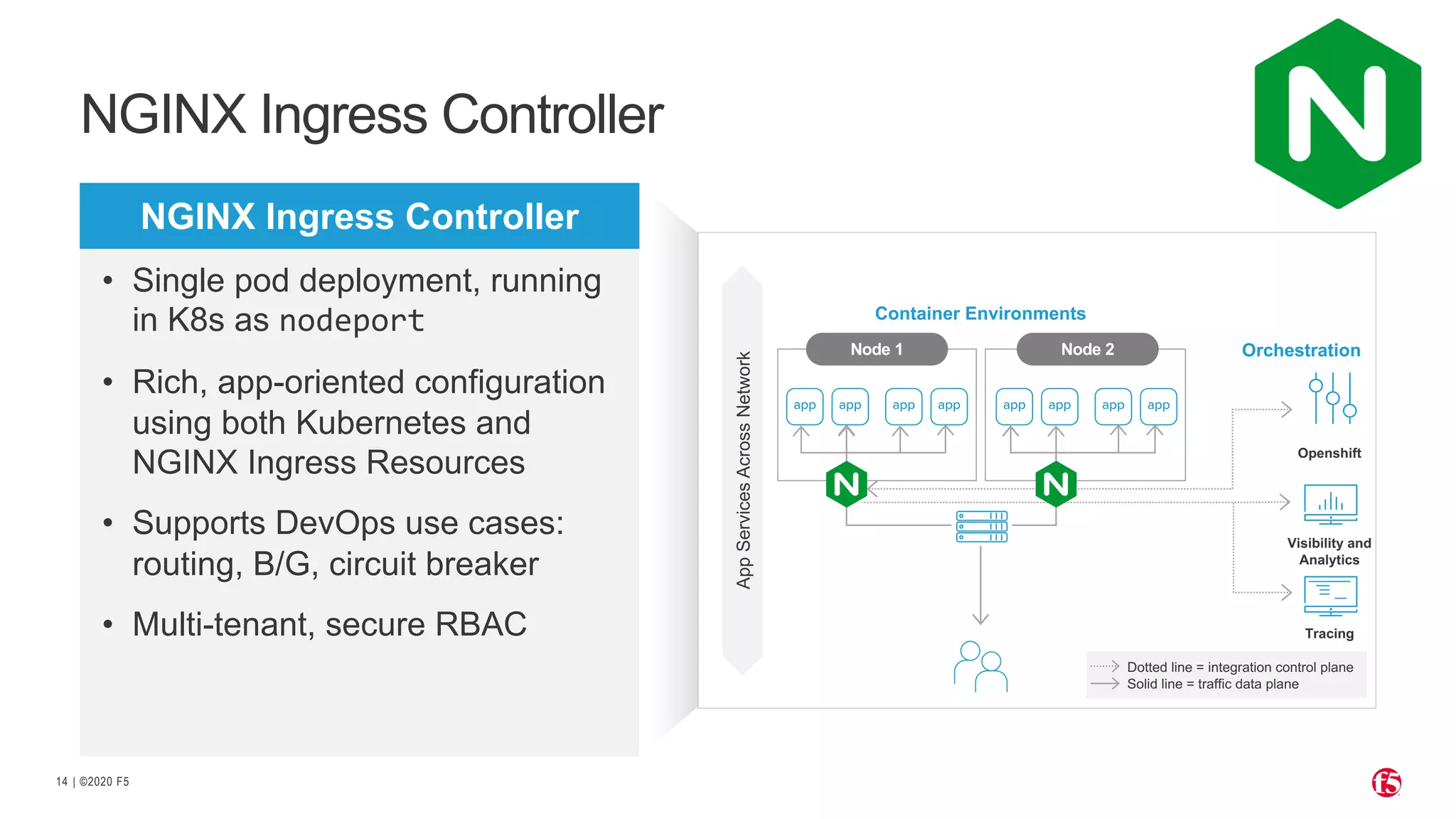
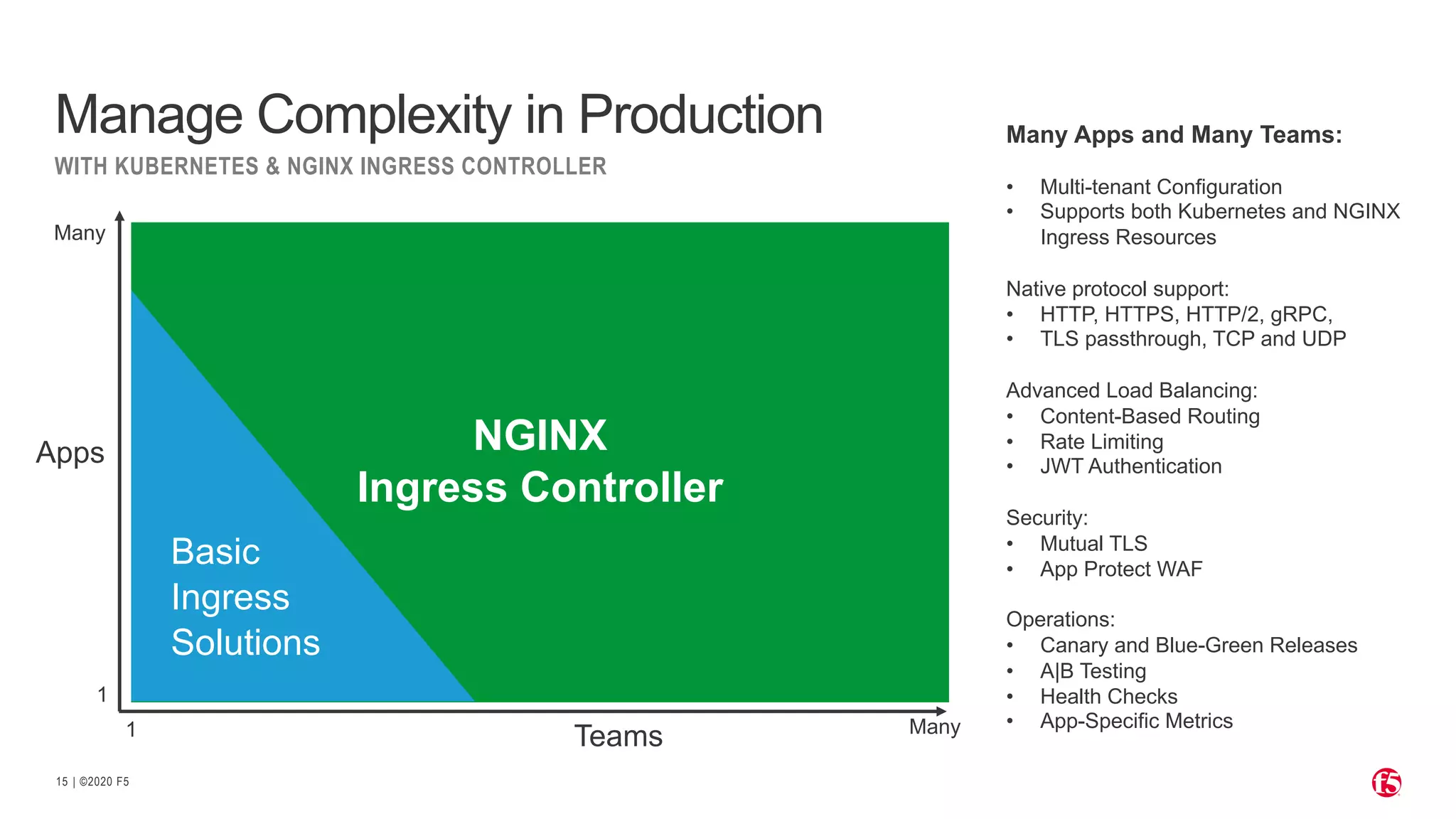
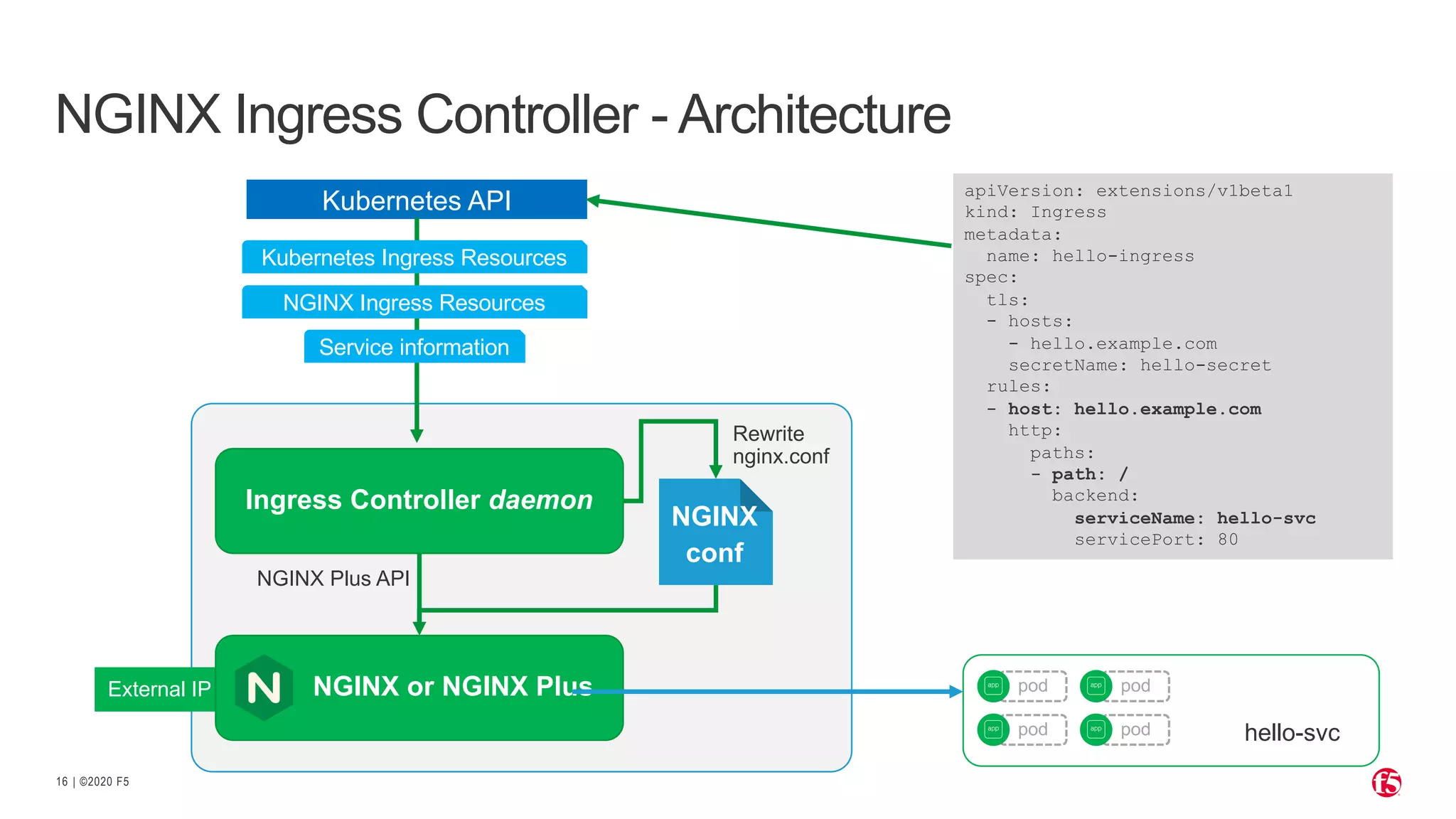
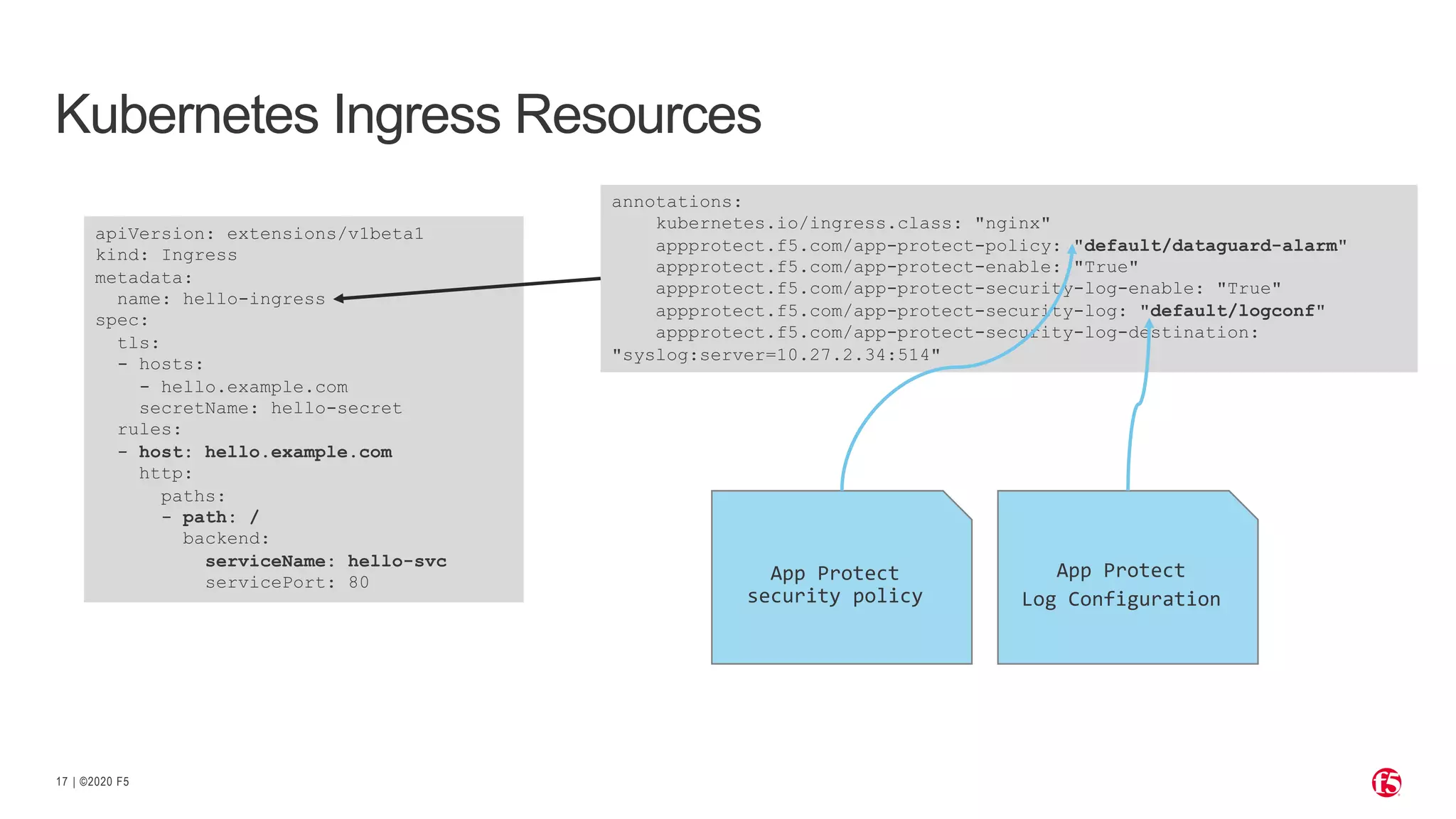
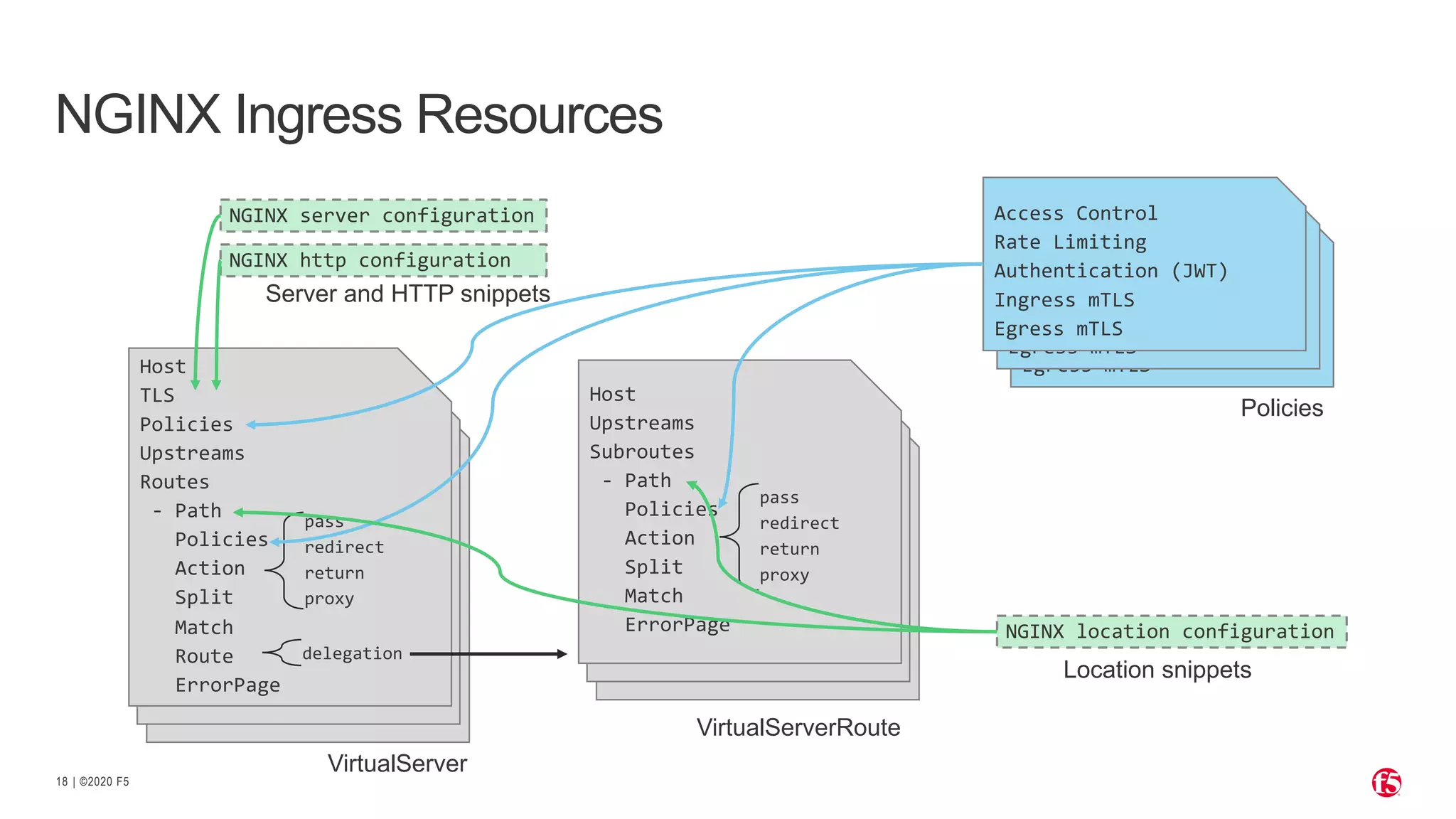
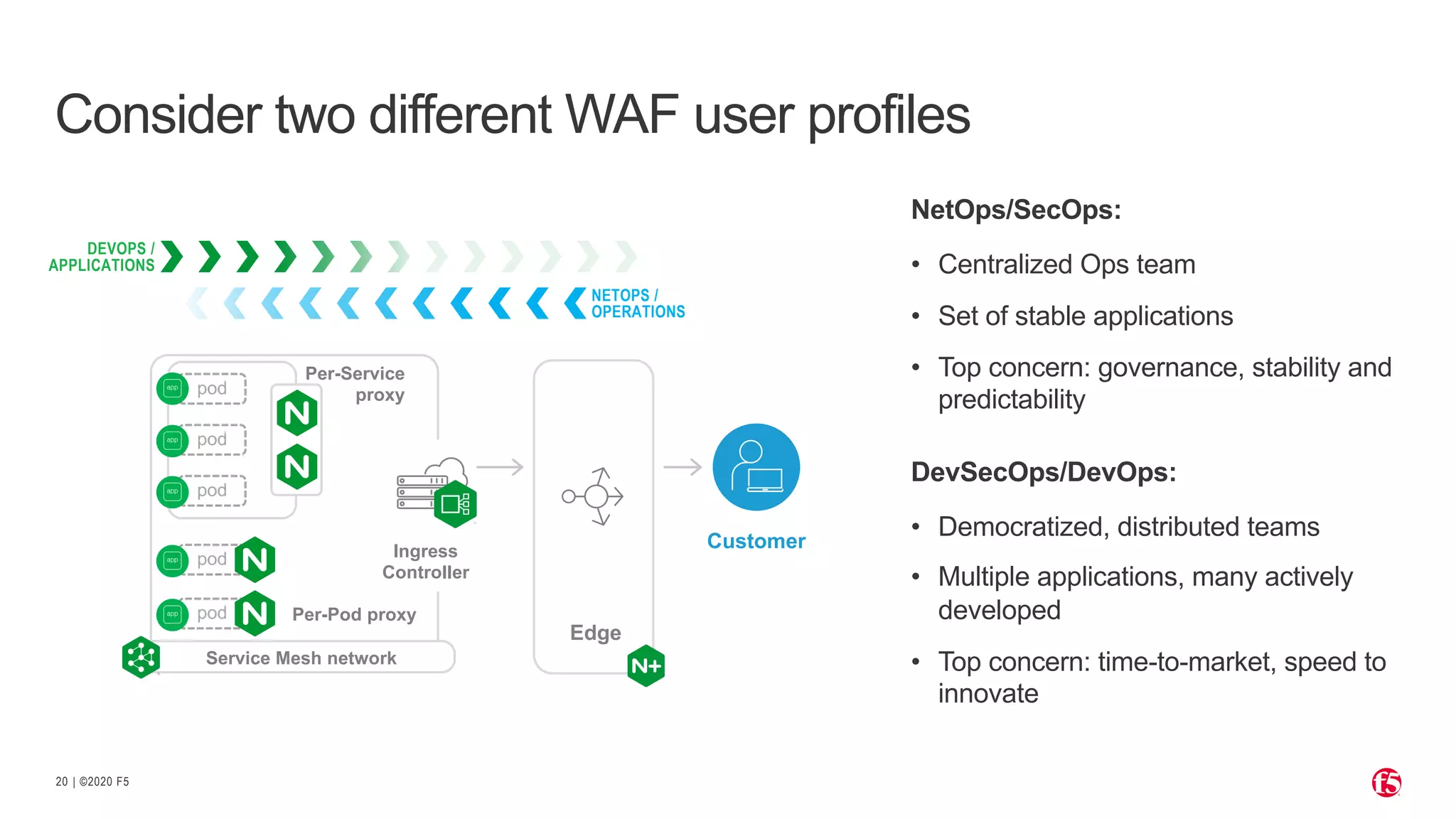
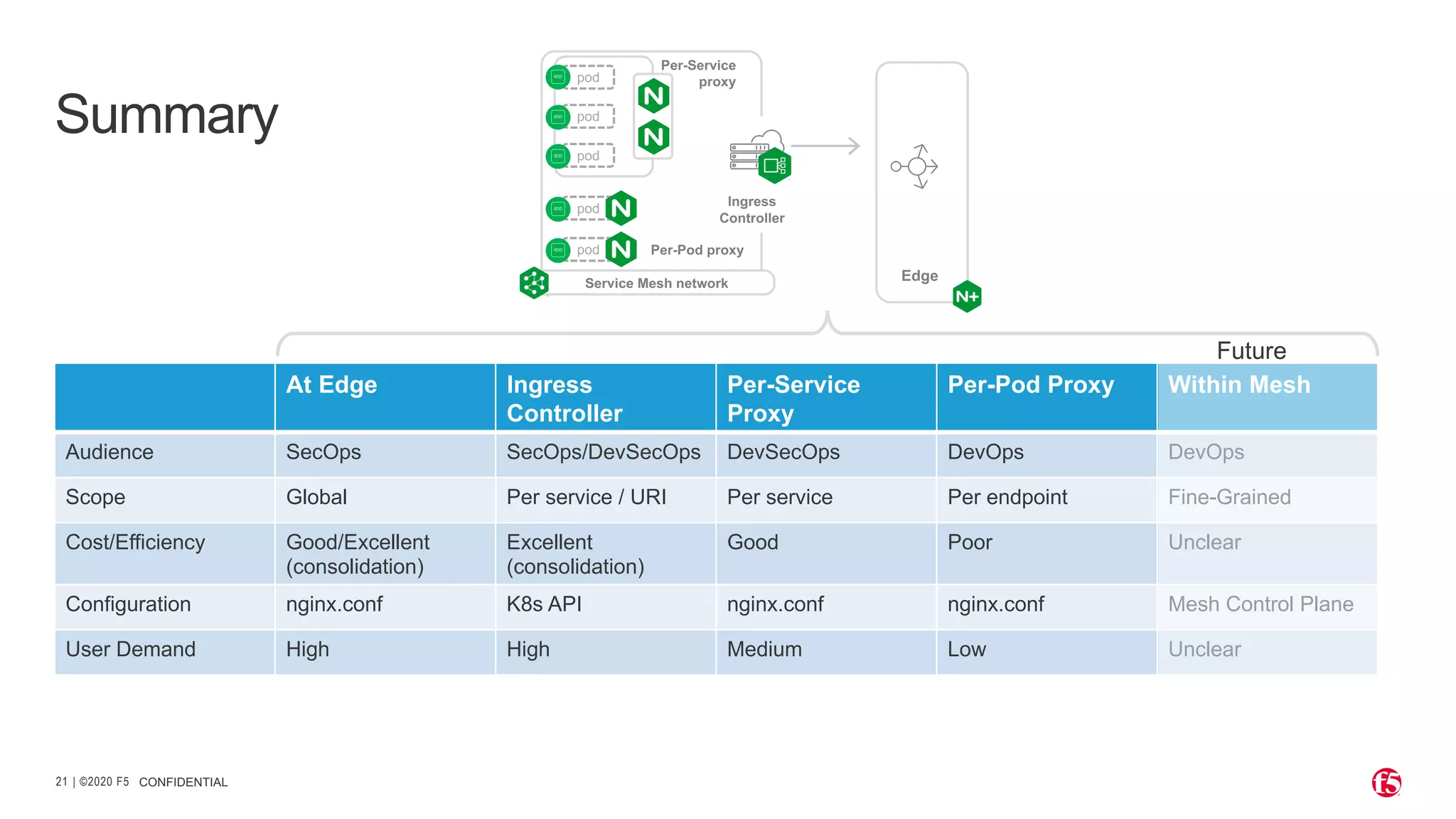
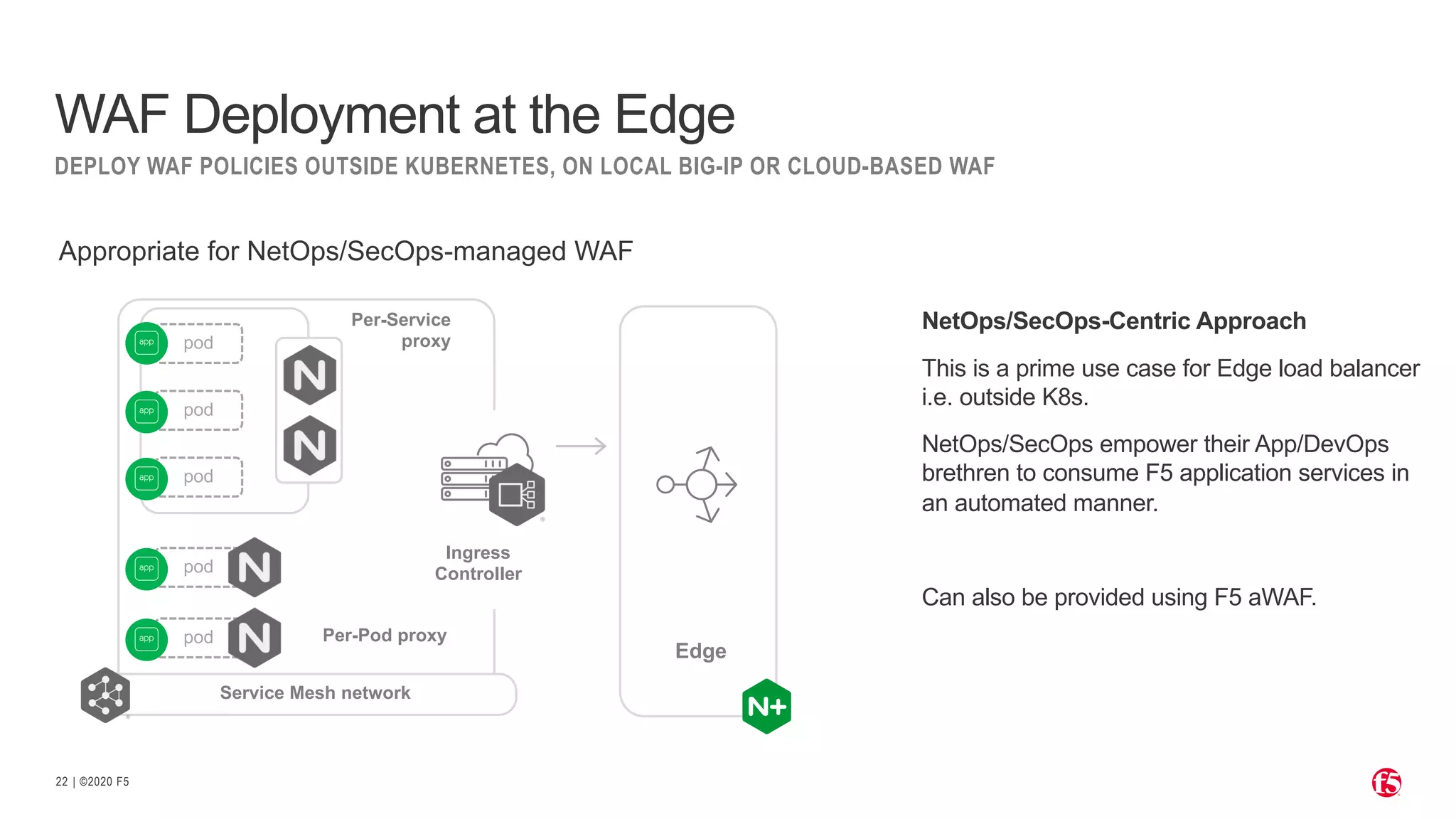
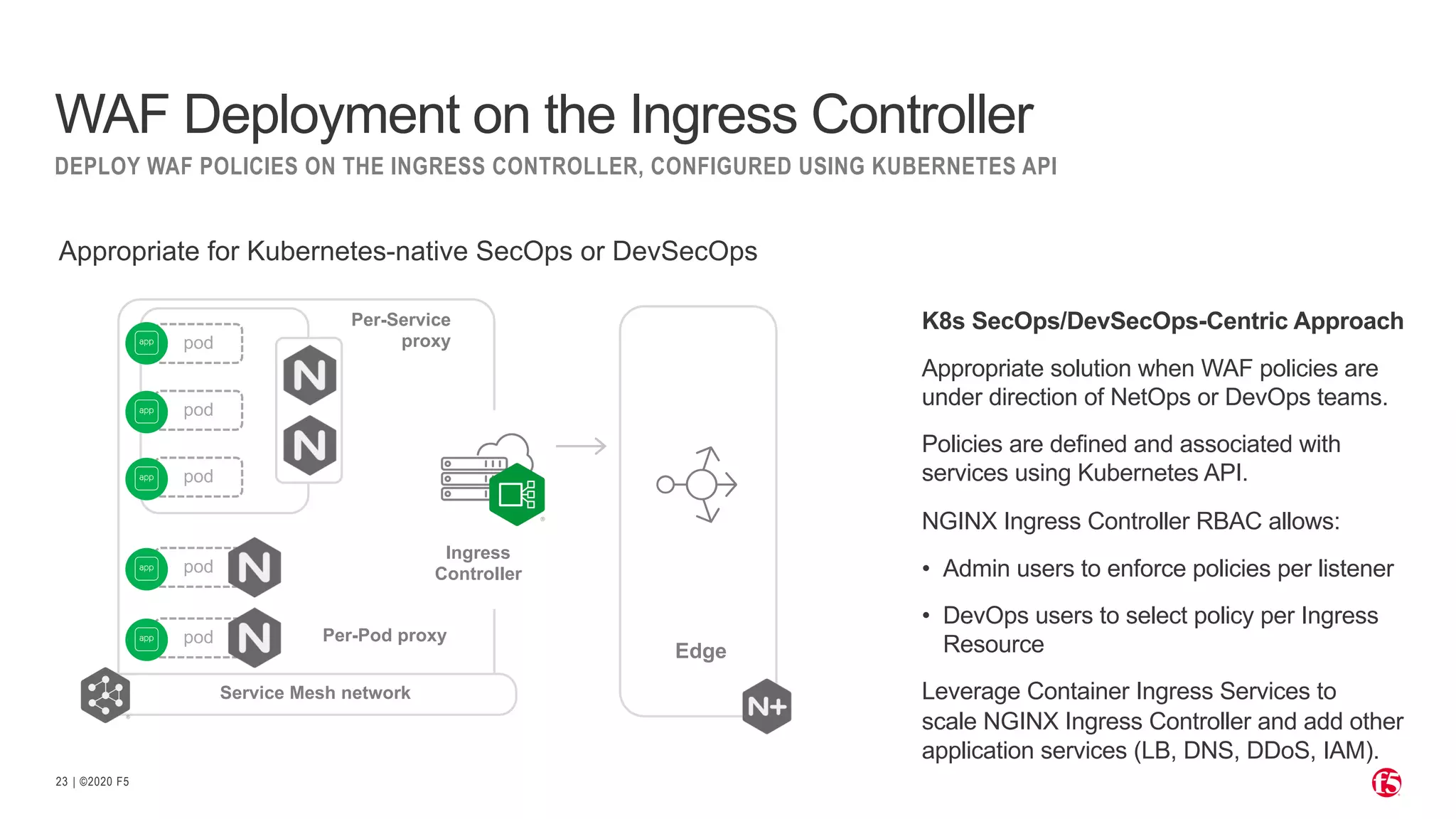
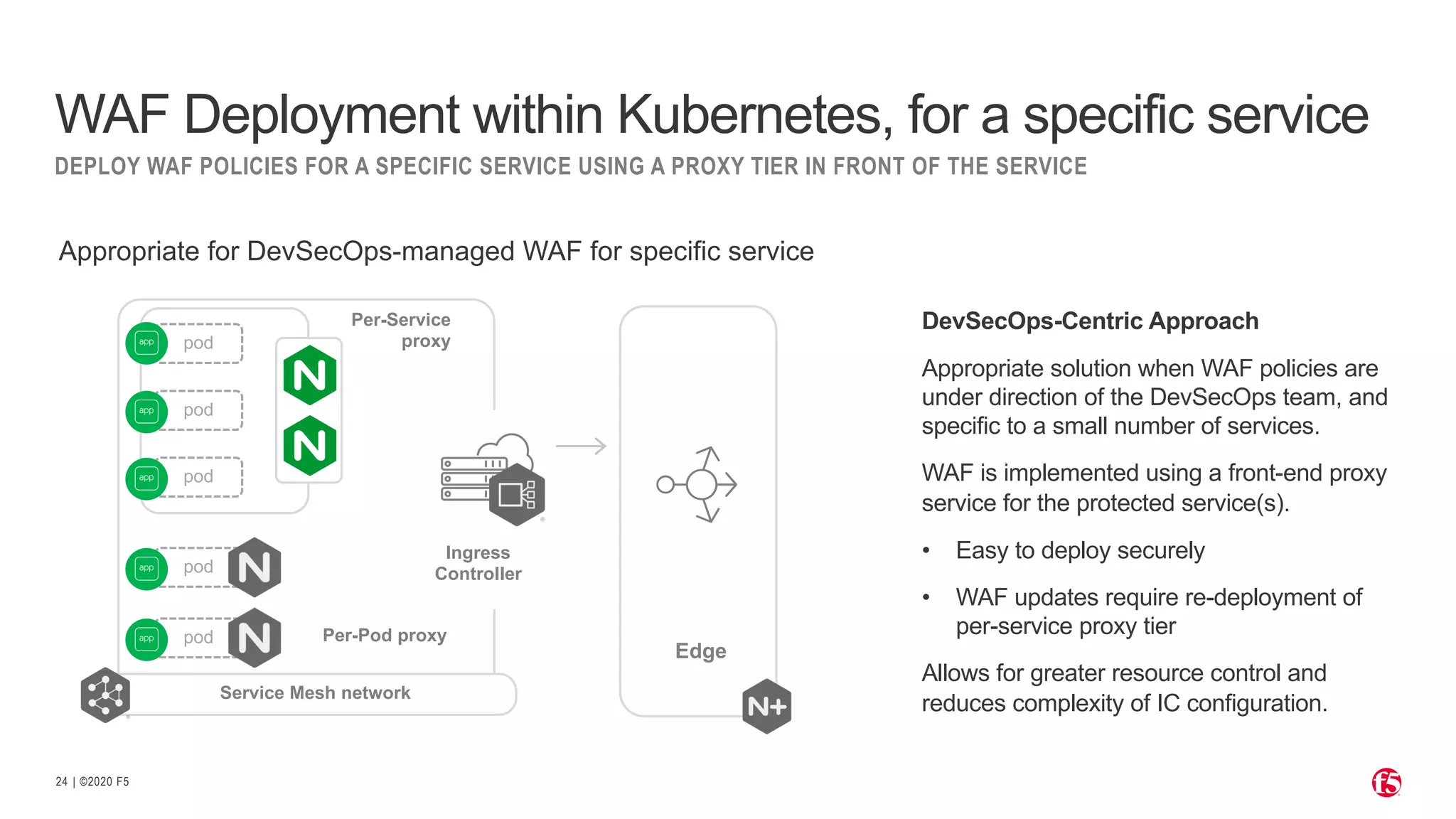
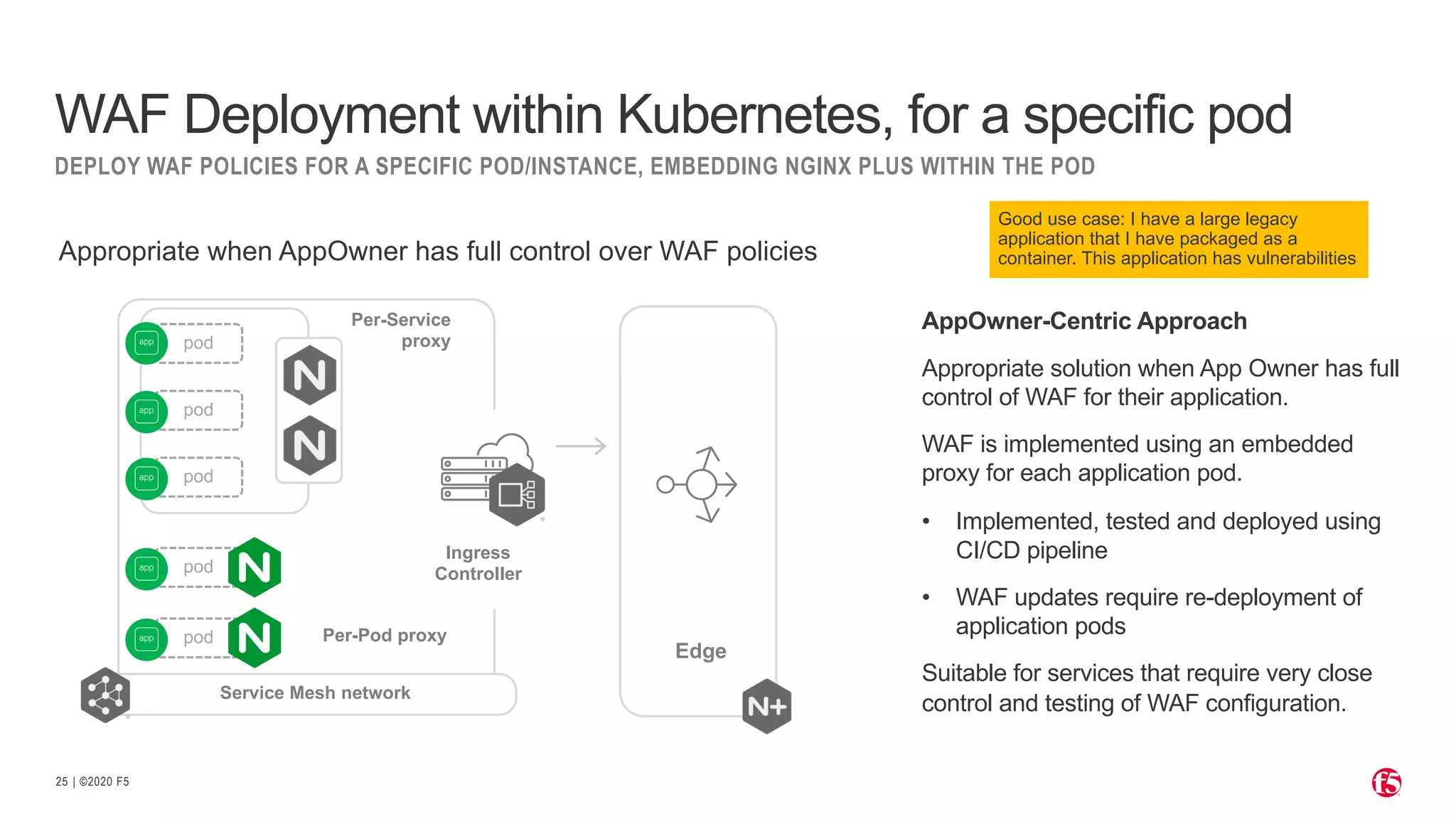
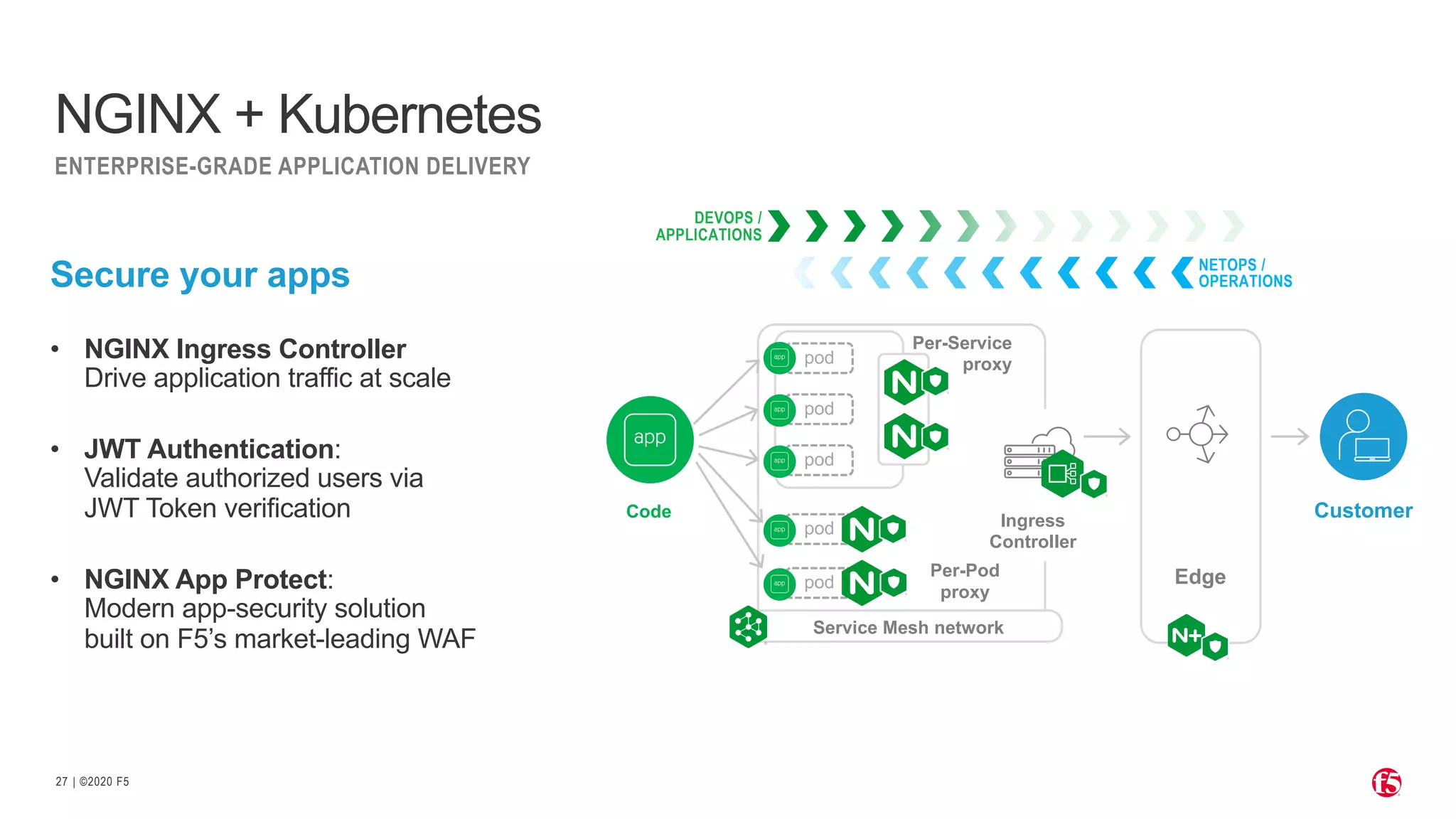
The document discusses optimizing Kubernetes with NGINX for effective application delivery, highlighting the increasing adoption of containerized apps and the associated security challenges. It outlines the architecture and functionalities of the NGINX Ingress Controller, emphasizing services like load balancing, security, and application monitoring. Additionally, it details various deployment strategies for Web Application Firewalls (WAF) in different environments, focusing on the need for governance and speed in modern dev operations.